Over the past few years, we have seen media attention drawn towards the length of our attention spans as related to our use of technology. Some reports claim a drop from 12 seconds to 8 seconds over the past decade, while others refute that data.
In either case, what we do know is that we must take advantage of the time we have our user’s attention during an immersive simulation. It is during those few critical seconds, after falling susceptible to a phishing simulation and while the user’s emotional state is heightened from perceived danger, that we have an opportunity to augment the learning they experience.
Because we measure long-term program success in terms of increases in recognition and reporting capabilities, you’ll want to focus your simulation education pages to facilitate those goals. In other words, you want to ensure users know what clues they may have missed and what action to take should they fall susceptible in the future.
Key Education Components:
- Indicating to your users that the education is part of an authorized phishing simulation.
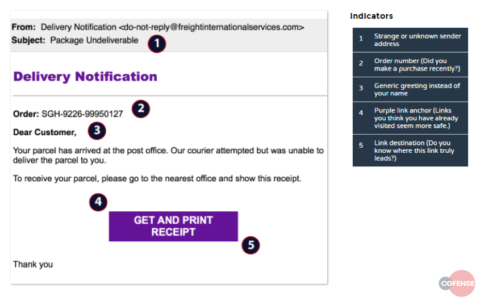
- Providing users an opportunity to review what they may have missed.
- Stressing to your users the importance of reporting suspected phishing attempts.
Program Transparency
As discussed in previous blogs and throughout our best practice materials, anti-phishing program transparency is critical to your overall success. Indicating to your users that what they are seeing is a part of your organization’s security initiatives helps them understand the importance of engaging with the information you are about to provide them.
Effective Recognition
To develop recognition capabilities, ensure your education page shows your users exactly what they may have missed within the specific phishing simulation they just received. This is particularly important when it comes to developing resilience against active threats in the wild or known phishing attempts against your company.
As in the example above, highlight and describe key indicators such as unknown senders, generic / inappropriate greetings and link destinations. If we don’t show our users how to identify and consider these markers of a phishing email, we can’t expect them to improve their recognition capabilities.
Awareness is NOT Enough
In 2017, Cofense™ surveyed office workers and found that 95% of them were aware of phishing, indicating the gap between the knowledge of a problem’s existence and the capability to act to resolve it.
If we are to incorporate our users as a part of our security infrastructures, we must provide them an efficient method of reporting suspected phish and stress that they use it.

Not only will users report simulations, they will retain what they have learned and report real malicious phish that make it past your technology defense. To take advantage of this in your anti-phishing program, it is critical that you are encouraging the reporting suspected phish with all users in your enterprise.
Focused Attention
Getting left of breach requires that we engage our users in the defense of our organizations and focus their attention on what they can do to improve their own recognition and reporting capabilities. We can assist them by providing education that facilitates those goals clearly and succinctly.
Always be sure to tie your simulations to your authorized (and transparent) anti-phishing program. Show users exactly what they missed and encourage them to report. Doing so will increase your company’s phishing mitigation capabilities quickly and effectively.
Don’t miss another threat… Sign up for free threat alerts from Cofense Intelligence™ and Cofense Research.