Email attacks are the primary mechanism impacting companies to deploy ransomware, steal credentials, or trick recipients with business email compromise (BEC) attacks. When they occur, these attacks are capable of inflicting financial and reputational damage to an organization. That’s where the Cofense Technology Alliance Program (TAP) comes in. For more than five years, Cofense has been strengthening phishing detection and response for security teams through our technology partnerships. And our list of partners keeps growing.
Current Cofense TAP partners and areas of focus below include:
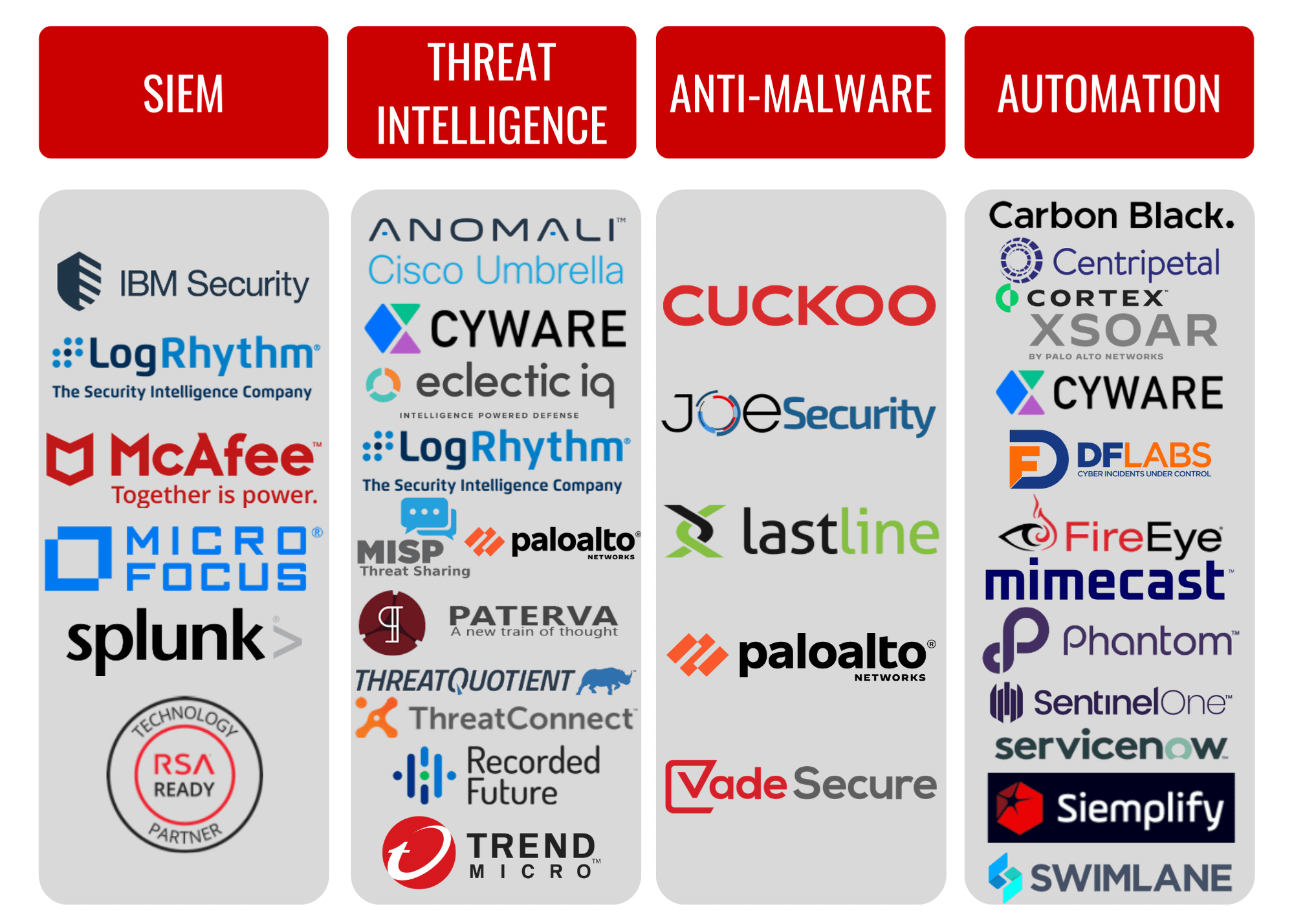
To become a Cofense TAP partner, visit here.
How it Works
When armed with Cofense Triage™ and Cofense Intelligence™, organizations can leverage a combination of employee-reported phish bypassing secure email gateways (SEGs) and 100% human-verified phishing threat intelligence. Both Cofense Triage and Cofense Intelligence enrich automation, orchestration and response. Cofense Triage and Cofense Intelligence offer security teams the ability to harness the power of credible employee-reported and human-verified phishing intelligence.
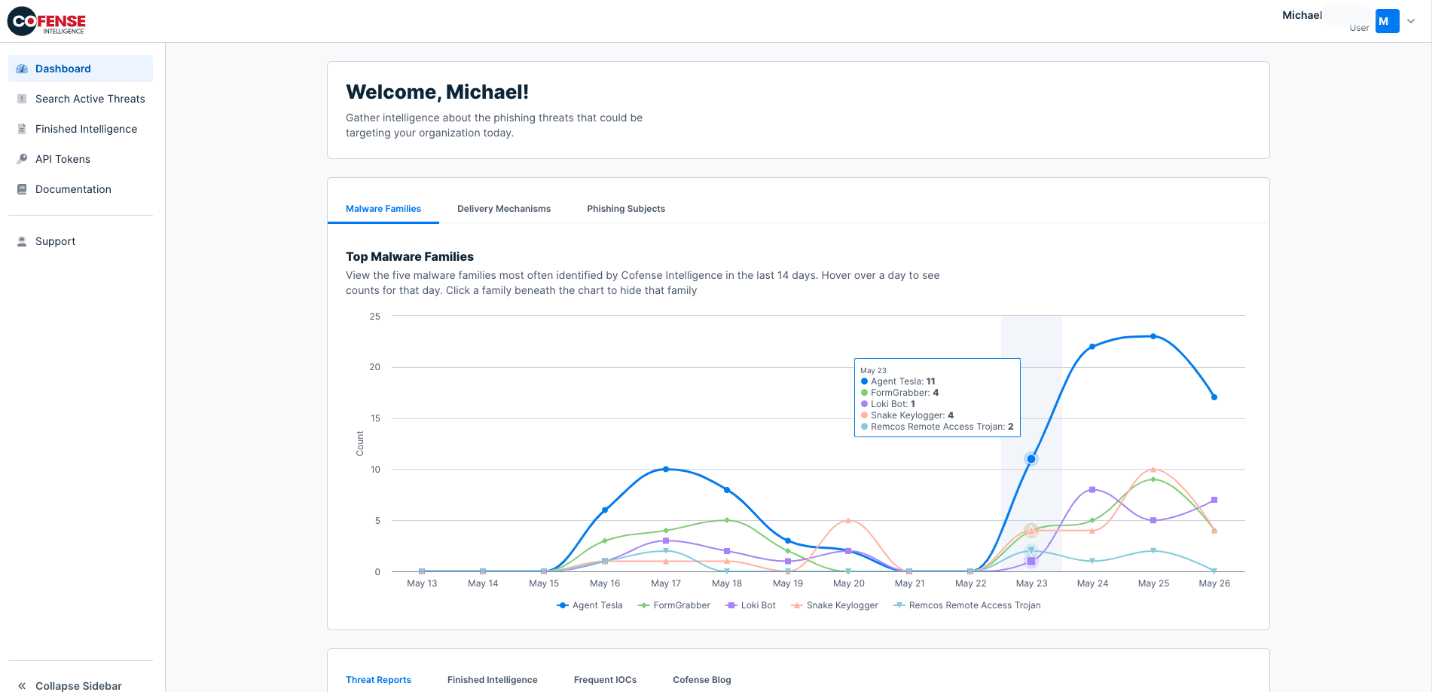
Cofense sees more phishing data across more environments than anyone else in the world
Cofense Triage ingests and analyzes employee-reported phishing emails that have bypassed the legacy, costly and slow-to-deploy SEGs. Analysts using a threat intelligence platform (TIP) or security orchestration automation and response (SOAR) solution can ingest phishing indicators from Cofense Triage’s API. For SOAR platforms, Cofense Triage provides appropriate automation to enable the analyst to be able to prioritize and analyze reported emails to identify non-malicious false positives and threats. Relevant context allows the analyst to quickly understand the potential impact and business risk of phishing threats and take rapid and decisive action to contain them.
But don’t just take our word for it.
“Palo Alto Networks’ Cortex XSOAR and Cofense integrate to help mutual customers defend against phishing attacks. The Cofense Triage and Cofense Intelligence content packs, available in the Cortex XSOAR Marketplace, automate phishing response workflows across the enterprise. Leveraging playbooks that provide contextual enrichment of reported phishing attempts, this powerful combination helps the SOC identify and stop phishing attacks in minutes as opposed to hours or days,” said Matthew Chase, Director, Partner Success, Palo Alto Networks.
“ThreatQuotient customers rely on credible threat intelligence and phishing is a top threat regardless of industry. The Cofense Intelligence integration helps mutual customers focus on highly credible phishing intelligence to defend their environment. In addition, customers can configure ThreatQ to ingest employee-reported phishing indicators from Cofense Triage. ThreatQ integrations with Cofense help analysts operationalize indicators of phishing and leverage automation for quick incident response decisions,” Haig Colter, Director, Alliances, ThreatQuotient said.
Cofense Intelligence comprised of human-verified indicators is a valuable source of intelligence security analysts can use during incident investigation and threat hunting. Unobstructed views into credible phishing threats results in higher confidence and allows analysts to take action based on the indicator results sent back into their platform.
“Cyware’s threat intelligence platform, CTIX, ingests human-verified phishing indicators and contextual reports from Cofense Intelligence. In addition, our SOAR solution, CSOL, integrates with Cofense Triage to ingest phishing indicators reported by employees that bypassed their email gateway. Security teams run playbooks to automate and respond to phishing threats, which frees analysts up for other cybersecurity tasks, said Avkash Kathiriya, VP, Research and Innovation, Cyware Labs.
The Cofense TAP program, comprised of an ecosystem of leading security providers and multiple, key technical integrations, was introduced in March 2016. The goal was to provide joint customers with easy and effective integrations that strengthen security, improve operational workflow and manageability, maximize security investments and reduce the risk of falling victim to phishing-driven cyberattacks. Since inception, TAP has continued to deliver exceptional value to mutual customers since its formation, and the alliance has further strengthened its ability to protect organizations from today’s advanced threats. Created to deliver security benefits that can only be achieved through close cooperation and shared intelligence, the Cofense TAP program actively shows what can be achieved through a shared commitment to increased security operations efficiency and maximized customer value.
“I am very proud of the Cofense TAP program and the growth that we have achieved with our partners over the last 5 years,” said Allan Carey, Cofense VP, Business Development. “We have developed both Cofense Triage and Cofense Intelligence to seamlessly integrate with existing security operations technologies and processes. We are committed to continuing to expand this program for our customers so they can strengthen their phishing detection and response.”
Managed Phishing Detection and Response
While our integrations can easily be used and managed by internal Security Operations teams, many organizations choose to use Cofense Managed Phishing Detection and Response (MPDR) a service delivered by the Cofense Phishing Defense Center (PDC). Operating 24×7 out of strategic locations around the world, the Cofense PDC is staffed by experienced phishing threat analysts to handle all elements of analysis of reported emails. Supported by the Cofense Research and Intelligence teams, the PDC is able to utilize as needed an array of proprietary, open source, and commercial threat analysis tools.
Cofense MPDR customers participate in a collaborative phishing defense network – 27 million strong and growing — enabling a global perspective of threats. This approach also gives PDC analysts the most up to date understanding of evolving phishing threat actor tactics and the techniques needed for effective analysis to capture all IOCs, even when automated approaches fail. Once threats have been identified, the PDC passes actionable intelligence to customer teams.
Take advantage of the power of managed phishing defense expertise to enrich other security platforms after phishing analysis.
With MPDR, organizations can focus their often resource-constrained Security Operations teams on activities that mitigate attacks and proactively protect the business, rather than spending time on phishing email analysis. Once a phish has been verified, integrations leveraging Cofense APIs ensure security teams can take additional action on verified phishing threats. Find out more about Managed PDR here.


