By Tej Tulachan, Cofense Phishing Defense Center
The Cofense Phishing Defense Center (PDC) has detected a recent phishing campaign that imitates legitimate WeTransfer applications by setting up fake websites that appear genuine. This enables threat actors to bypass email security gateways (SEG) to lure users into sharing their credentials. WeTransfer is a file hosting site that allows users easy access to share files. With the popularity of the service, it’s likely users would overlook the threat level within the email. Threat actors have reimaged this site to entice unsuspecting recipients to click on a malicious link that redirects them to the phishing page, resulting in users handing over their credentials.
Let’s take a closer look at the email to spot the red flags.
Figure 1: Email Body
The threat actor has urged the recipient to respond to this email with urgency as shown above in Figure 1, “Pending files will be deleted shortly.” This adds urgency via the timestamps. The button for the user to click to “Get your files” disguises the malicious URL link that redirects to the WeTransfer phishing landing page. To make this more genuine, threat actors listed common document names.
Another interesting point is the authenticity of the email address. The threat actor has gone to the effort of spoofing the email address to assure recipients that the email has arrived from the correct WeTransfer top level domain: “@wetransfer.com”.
Next, we’ll dive deeper into the email addresses in the email header in Figure 2. Spoofing the email address is the most common technique used in phishing campaigns to gain the user’s trust. The Message-ID below states the top-level domain: @boretvstar[.]com which is not related to WeTransfer at all. Furthermore, we noted that @boretvstar[.]com is for sale and, when accessed, leads to an error page: “This site can’t be reached.” This is another red flag. And finally, there is the failed sender policy framework (SPF) checks, indicating it’s not an authentic address of wetransfer.com.
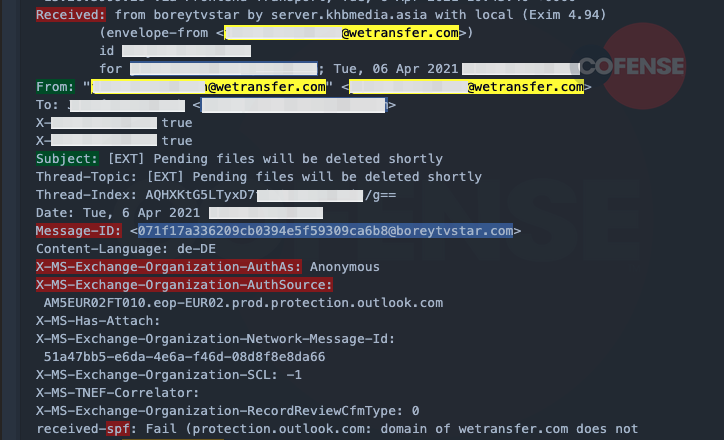 Figure 2: Email Header
Figure 2: Email Header
It clear to see the lengths taken to make the phishing landing page seem as close to the legitimate “WeTransfer” page as possible. However, on further inspection, we note that the Apple and Google logos are missing from the login buttons, and the URL does not correspond to the legitimate URL.
Phishing URL: hXXps://weetraansfeer[.]freesuport[.]ga/transfer.php?file
Legitimate link: https://auth.wetransfer.com/login?state=
In the final stage of the attack, once the user clicks on the button, they are redirected to the fake WeTransfer page as shown on Figure 3. The user is prompted to enter their credentials to download the shared file. The phishing landing page is prepopulated with the user’s email address within the login field. After entering the password, the user is shown a failed login attempt, which is a common tactic used by threat actors. Moreover, there is also another option to authenticate users via different online platforms (Apple, Google or Slack). This is another common tactic threat actors use to harvest multiple credentials.
Figure 3: Phishing Landing Page
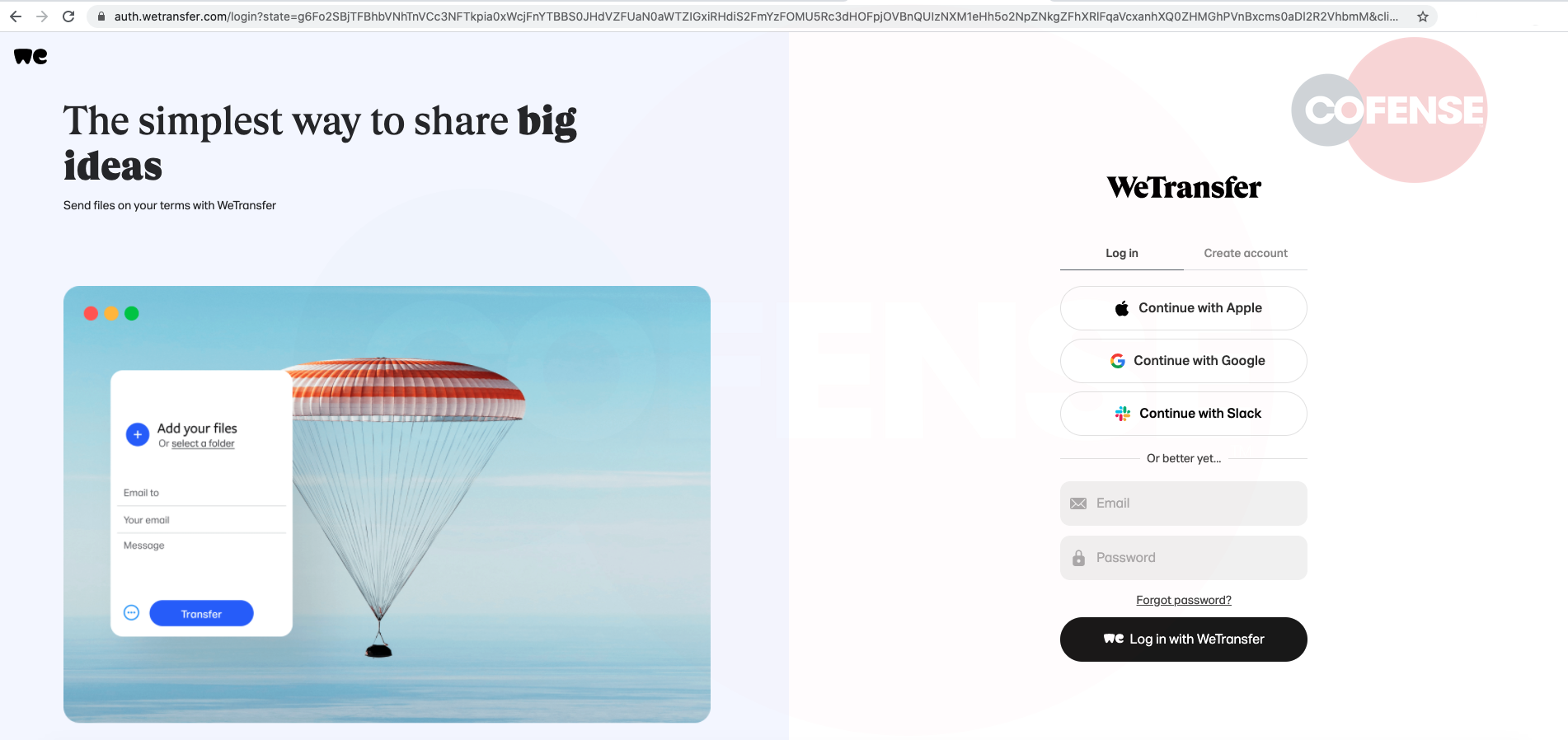 Figure 4: Legitimate Page
Figure 4: Legitimate Page
In recent weeks, the PDC has seen more than 40 similar campaigns across all our customers’ environments reported by well-conditioned users to identify the suspicious email. This phishing campaign is specifically designed to evade SEGs by abusing a genuine file-sharing platform. Users must be vigilant while engaging with such emails. Cofense can help defend against attacks like this. Contact us to find out how. To learn more about the attacks we discover, and that are reported by well-conditioned users, subscribe to our blog.
| Indicators of Compromise |
| hXXps://weetraansfeer[.]freesuport[.]ga/transfer.php?file |
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats. Past performance is not indicative of future results.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.


