Microsoft EOP
The Cofense Phishing Defense CenterTM has detected a new wave of attacks targeting the US taxpayer by delivering Amadey botnet via phishing emails. Amadey is a relatively new botnet, first noted late in Q1 of 2019. Known for its simplicity, it is available to hire for a very steep price compared to other commercially available botnets with similar functionality. Threat groups like TA505 have been known to leverage Amadey botnet as recently as July 2019 to deliver secondary malware like FlawedAmmy (RAT) and email stealers.
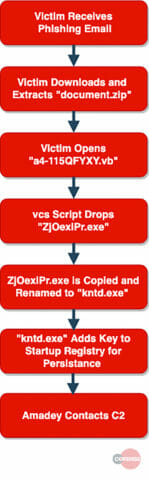
Here’s how a typical attack works:
Figure 1: Infection chain
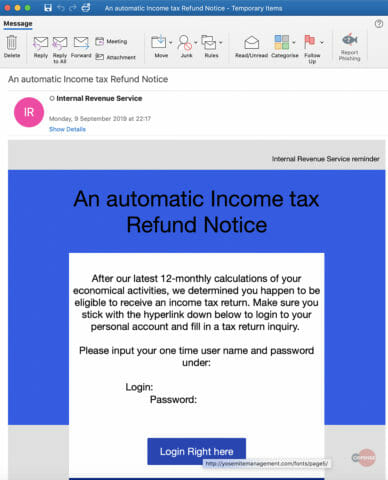
Figure 2: Email Body
The email body reports to be from the Internal Revenue Service (IRS) and claims that the recipient is eligible for a tax refund. The recipient is presented with a “one time username and password” and urged to click the “Login Right Here” button. As seen above in figure 1, the login button is an embedded Hyperlink and redirects to hxxp://yosemitemanagement[.]com/fonts/page5/. Here the recipient is presented with an IRS login page to enter the one-time password.
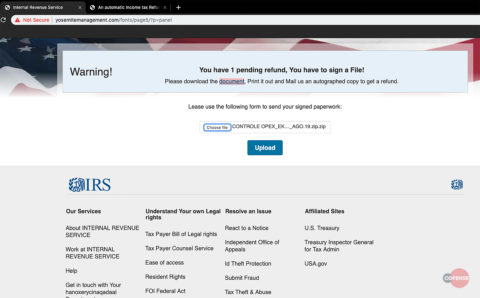
Figure 3: Infection Page
Once the recipient is logged into the fake IRS portal they are informed that they have “1 pending refund” and asked to download a document, print and sign, then either mail it back or upload a copy to the portal. When the recipient clicks to download the document, a zip file called “document.zip” is presented, which contains a Visual Basic script dropper.
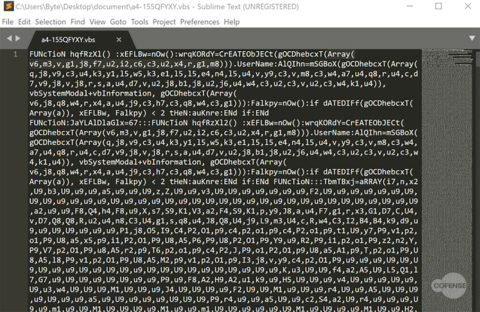
Fig 4. Obfuscated vbs Script
The VBScript is highly obfuscated and encrypted. For more details on how this VBScript was decoded, please take a look at the Cofense™ Labs detailed write-up, which can be found here.
At a high level, once executed the script decrypts itself at run time and drops an executable file called “ZjOexiPr.exe” in C:UsersByteAppDataLocalTemp. Once dropped it then proceeds to install the executable kntd.exe in C:ProgramDatafa42aa593 and execute the process.
Figure 5: Persistence
The Amadey process installs itself in C:ProgramDatafa42aa593 and to maintain persistence it uses Reg.exe, a command line tool for editing the registry. Next the script issues the command “REG ADD “HKCUSoftwareMicrosoftWindowsCurrentVersionExplorerUser Shell Folders” /f /v Startup /t REG_SZ /d C:ProgramDatafa42aa593”
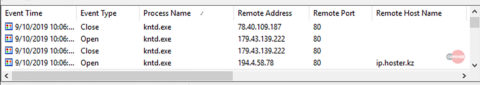
Figure 6: C2 channels
Amadey instantly beacons out to its command and control (C2) channels sending system diagnostic information back to the C2 server and awaits further instructions. Amadey connects out via HTTP on port 80 to multiple C2 servers.
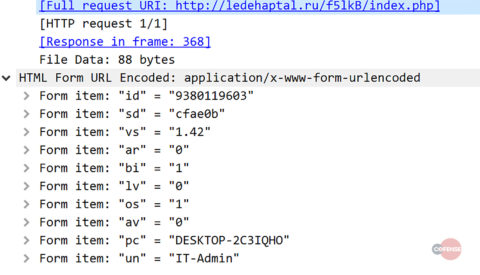
Figure 7: Network Traffic
If we take a closer look at the HTTP traffic we can see that Amadey sends system information back to its C2 server.
From the values given we can infer that:
ID – Unique identifier of the infected system
VS – Version of Amadey
OS – Operating system
AV – Antivirus
PC – System name
UN – Username
Additional Analysis:
Cofense Labs takes this analysis a bit deeper to deobfuscate the malware. To learn more, check out the Lab Notes on this analysis: https://cofenselabs.com/i-see-what-you-did-there/
Indicators of Compromise (IOCs):
Malware Artifacts
| File | MD5 Hash Value |
| document.zip | 7f9a3244d23baed3b67416e32eb949bd |
| a4-155QFYXY.vbs | 79d24672fff4c771830b4c53a7079afe |
| kntd.exe | a046030e2171ddf787f06a92941d37ca |
Network Connections
| URL | IP |
| hxxp://yosemitemanagement[.]com/fonts/page5/ | 160[.]153[.]138[.]163 |
| hxxp://ledehaptal[.]ru/f5lkB/index[.]php | 78[.]40[.]109[.]187 |
| hxxp://nofawacat[.]com/f5lkB/index[.]php | 179[.]43[.]139[.]222 |
| hxxp://Ip[.]hoster[.]kz | 192[.]4[.]58[.]78 |
HOW COFENSE CAN HELP
Cofense Resources
Cofense PhishMeTM offers a phishing simulation, “Tax Refund Notice –Amadey Botnet,” to educate users on the attack described in today’s blog.
89% of phishing threats delivering malware payloads analysed by the Cofense Phishing Defense Center bypassed secure email gateways. Condition users to be resilient to evolving phishing attacks with Cofense PhishMe.
Remove the blind spot with Cofense ReporterTM—give users a one-click tool to report suspicious messages, alerting security teams to potential threats.
Quickly turn user reported emails into actionable intelligence with Cofense TriageTM. Reduce exposure time by rapidly quarantining threats with Cofense VisionTM.
Easily consume phishing-specific threat intelligence to proactively defend your organisation against evolving threats with Cofense IntelligenceTM.
Thanks to our unique perspective, no one knows more about REAL phishing threats than Cofense. To understand current threats, read the 2019 Phishing Threat & Malware Review.
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks.