By Tonia Dudley, Cofense Security Solutions
Every day, CofenseTM threat analysts and researchers monitor phishing and cyber security threats in the wild. In June of 2019, our researchers uncovered a sextortion botnet that contained a list of 200 million email addresses. Read the original announcement here.
That database has since grown to over 330 million email addresses.
We have also identified an increase in the number of unique web domains being targeted by the botnet. When we released our original findings, the database had close to 6 million unique domains. That total has grown to 7.4 million unique domains.
To be clear, this threat is not a breach of any Cofense data or systems. Rather, it’s a botnet that our research team discovered out in the wild. The botnet uses email addresses and credentials which we believe were acquired via a series of breaches over the past decade. Visit our info center for additional resources.
 Fig. Sample containing text as images to deceive automated analysis
Fig. Sample containing text as images to deceive automated analysis
Cofense LabsTM has created a sextortion lookup tool to check impacted accounts and domains as well as a resource center with helpful tips on how to protect your organization and your personal accounts from falling victim to these types of threats as well as the steps you can take should you receive a sextortion scam.
Cofense Labs will continue to monitor the botnet and share updates on our Twitter handles @Cofense and @CofenseLabs.
HOW COFENSE SOLUTIONS CAN HELP
Reports of sextortion and other ransom scams to the Cofense Phishing Defense CenterTM are increasing. Condition users to be resilient to evolving phishing attacks with Cofense PhishMeTM and remove the blind spot with Cofense ReporterTM.
Quickly turn user reported emails into actionable intelligence with Cofense TriageTM. Reduce exposure time by rapidly quarantining threats with Cofense VisionTM.
Attackers do their research. Every SaaS platform you use is an opportunity for attackers to exploit it. Understand what SaaS applications are configured for your domains – do YOUR research with Cofense CloudSeekerTM.
Thanks to our unique perspective, no one knows more about REAL phishing threats than Cofense. To understand them better, read the 2019 Phishing Threat & Malware Review.
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats.
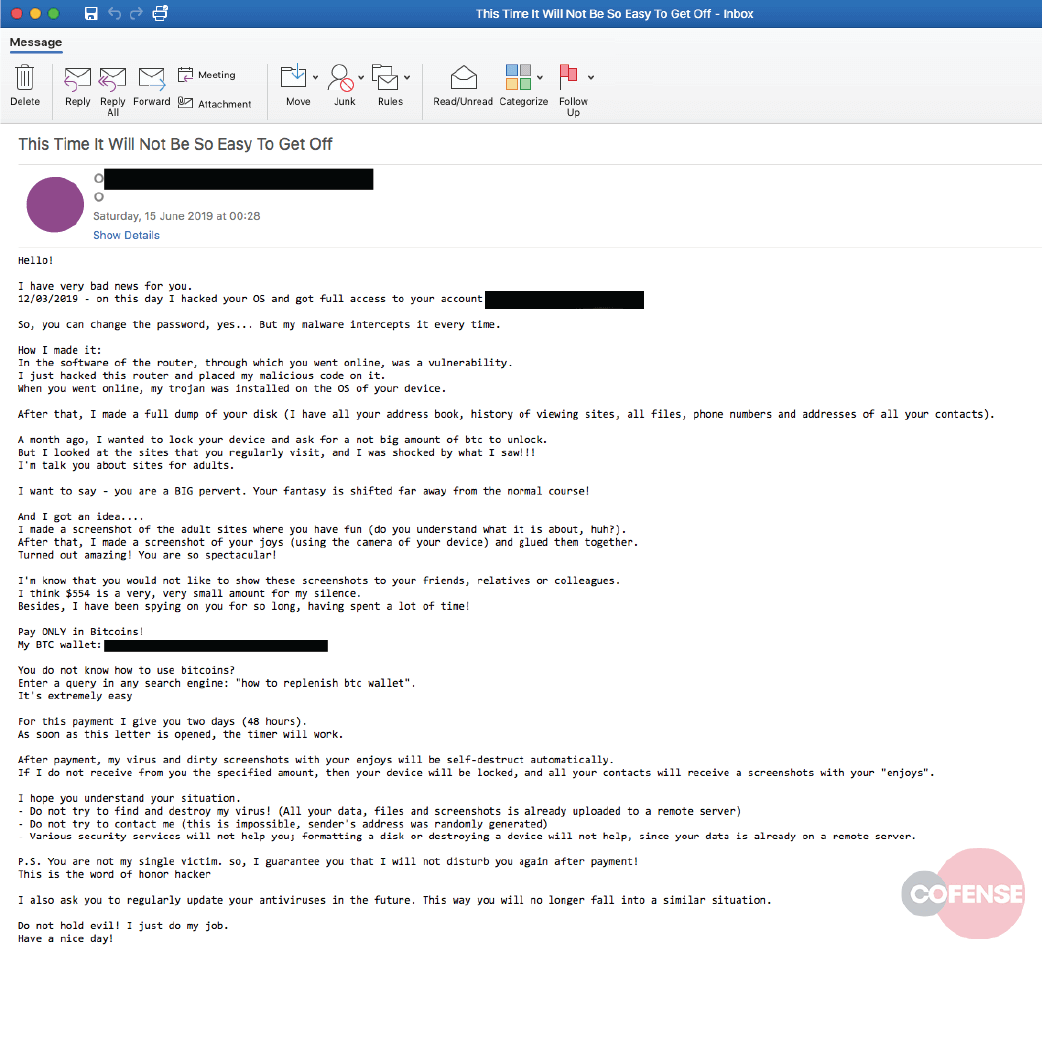 Fig. Sample containing text as images to deceive automated analysis
Fig. Sample containing text as images to deceive automated analysis

