By Kian Mahdavi, Cofense Phishing Defense Center
The Cofense Phishing Defense Center (PDC) has discovered a phishing campaign that targets Office 365 users and includes a convincing SharePoint document claiming to require an email signature…urgently. The campaign was found in an environment protected by Microsoft’s own secure email gateway (SEG). With thousands of individuals still required to telework, this has created a perfect opportunity for hackers to lure their victims with almost picture-perfect sharing themed emails.
Let’s understand how this attack works.
Figure 1 – Email body
Figure 1 showcases correct spelling and grammar in messaging that includes urgency (“and response urgently”). The user’s name is not apparent in the opening message above, indicating that this is a mass-distribution campaign intended to reach multiple users.
When the user reported this email, suspicion was probably sparked by the sender’s address and the hovered hyperlink, neither of which contained the all-important “Microsoft” reference.
Once the recipient clicks on the hyperlink, the following page will appear:
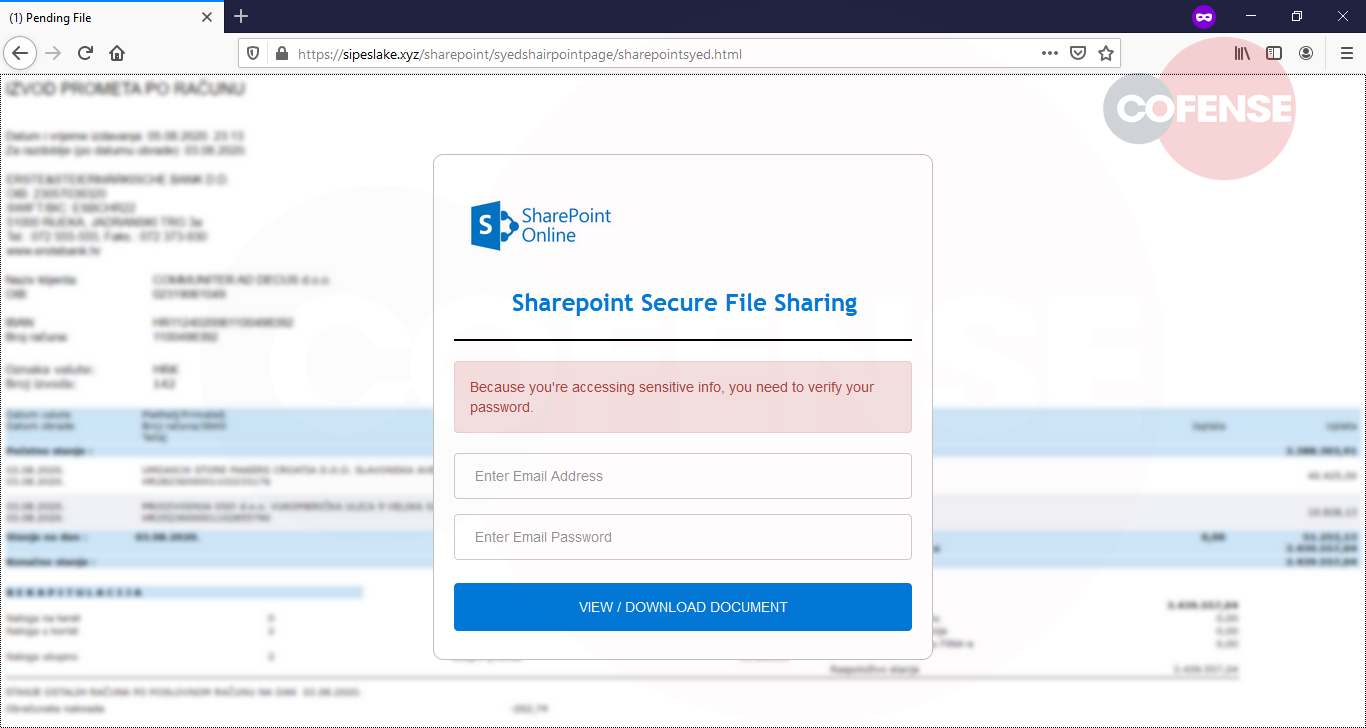
The vendor’s branded logo and the “Pending file” notification could suffice for threat actors to extract and harvest users’ personal data, as shown above in Figure 2. Once credentials have been supplied, the campaign redirects the user to a spoofed unrelated document, which might be enough to trick the user into thinking this is a legitimate transaction.
A user’s personal data could potentially be in the hands of the threat actor, assuming they logged in with their true Microsoft credentials.

An online tool called Whois lookup allows us to extract useful statistical information. We can use this to our advantage to evaluate the legitimacy of the domain name. Basic information such as the quantity of sites hosted, IP location as well as historical lifetime – are all useful for our investigation.
Learn more about threats like this one, and how you can align your security-awareness phishing program to real threats hitting your users’ inbox by checking out our Phishing Email Database. To optimize and simplify phishing threat detection and analysis, take a look at the Cofense Managed Phishing Detection and Response platform for a comprehensive suite of solutions.
Indicators of Compromise:
| Network IOC | IP |
| hxxps//sipeslake[.]xyz/sharepoint/syedshairpointpage/ | 172[.]67[.]196[.]138 104[.]21[.]12[.]229 |


