With this release, SOC teams can quickly identify and remediate reported emails that contain actionable intelligence from Cofense Intelligence and new features to increase security and close down vulnerabilities attackers are known to exploit. In Cofense Triage 1.26, you can easily increase efficiency and security.
Integration with Cofense Intelligence IOC Feed
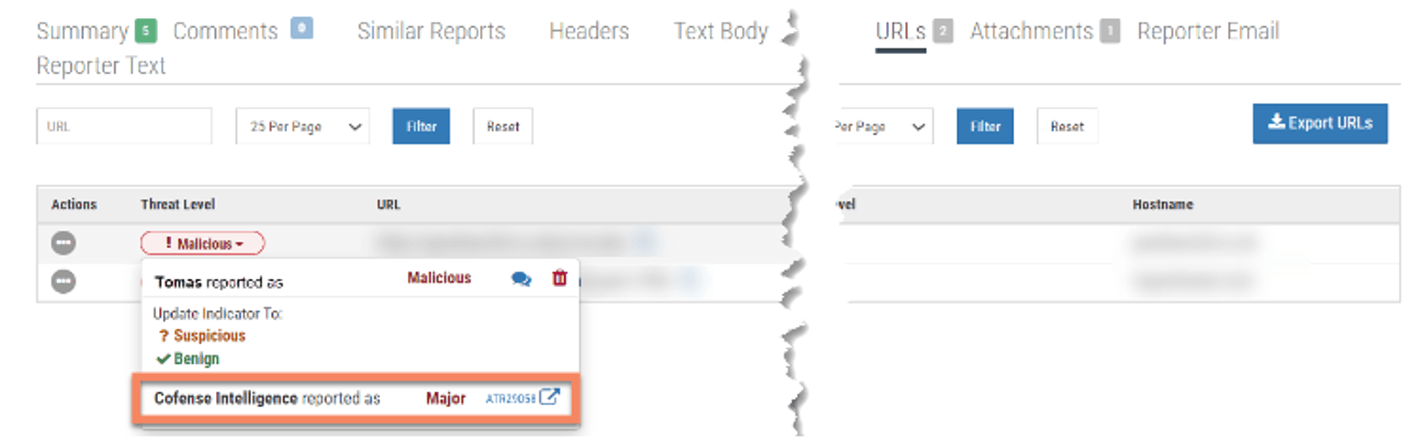
Cofense Intelligence™ provides a timely, accurate, and actionable phishing IOC (Indicator of Compromise) threat feed, enabling quick detection of actual malicious emails found within enterprise environments. Intelligence classifies the impact of each indicator as major, moderate, or minor. This product integration pulls Major indicators from Cofense Intelligence into Cofense Triage and clearly tags them on active reports or clusters. This alerts your SOC analyst that this email contains actionable intelligence so they can immediately take action, remediate the threat, and overall increase their efficiency and reduce Mean Time to Detect (MTTD) and Mean Time to Response (MTTR).
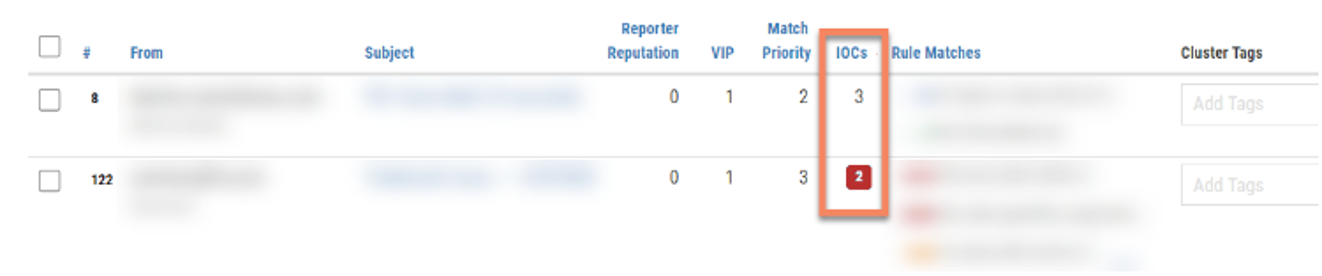
The most difficult part of working on any email investigation is the lack of context. With the integration of Cofense Intelligence and Cofense Triage, you can clearly see when a Major Incident is tagged by Cofense Intelligence. Our Cofense Intelligence network consists of several proprietary data sources that include the Cofense PDC and Cofense Reporter ecosystem and is based on actual malicious emails and zero-day threats found within enterprise environments. In other words, our PDC receives thousands of emails a day from enterprise and Fortune 500 organizations, analyzes and then shares the malicious ones with Cofense customers around the globe so they can be automatically removed from inboxes or remediated.
You can create a playbook to run a remediation plan for a reported email anytime that a Major Incident is found with Cofense Triage; no investigation is needed as it’s already been confirmed to be a threat by Cofense’s Intelligence Team. However, if you are curious about an IOC, you can easily navigate to Cofense Intelligence ThreatHQ to get more details on it.
SOC teams are constantly overburdened with alerts and face difficulty assigning priority and triaging the most impactful threats first. With this release, we reduce the burden on SOC analysts and reduce MTTD/MTTR by quickly automating email investigations that contain actionable intelligence and, ultimately, save them time so they can focus on other priorities.
Streamlined process for applying operating system security updates
SOC Teams can now install security updates between releases of Cofense Triage without waiting for the next full release to drop. New options on the System Maintenance page enable you to check for security updates, configure Cofense Triage to install security updates automatically on a specific day and time, and configure Cofense Triage to automatically reboot after security updates are installed. Want a “set it and forget it” approach? This new feature helps SOC teams to strengthen their defenses and close down vulnerabilities threat actors are known to exploit.
What else is in this release?
We’ve included a few customer-requested UX updates that will make navigating and automating within Cofense Triage more seamless as well as incremental updates to previous features. You can learn more about these improvements in the release notes.
To learn more about Cofense Triage or to see these new capabilities in action, please request a demo at https://go.cofense.com/live-demo/. Cofense Customers can always reach out to their CX team for more information on upgrading.
*Please note: Customers must have Triage versions 1.25.0 or 1.25.1 in order to upgrade to 1.26.0
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats. Past performance is not indicative of future results.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.


