[vc_row][vc_column animation_iteration=”1″][mvc_infobox info_style=”mega_info_box_2″ info_opt=”show_icon” icon_size=”35″ icon_height=”75″ icon_radius=”15px” border_width=”2″ title_color=”#cd202c” font_icon=”fa fa-exclamation-triangle” icon_color=”#cd202c” border_clr=”#dd3333″ info_title=”Gateways Bypassed” title_size=”25″ css=”.vc_custom_1585945742558{margin-top: 20px !important;margin-bottom: 30px !important;}” hoverclr=”#cd202c” icon_bg=”#ffffff” hoverbg=”#ffffff” caption_url=””]
Forcepoint
Microsoft 365
[/mvc_infobox][/vc_column][/vc_row][vc_row][vc_column][vc_column_text]
By Tej Tulachan and Milo Salvia
The CofenseTM Phishing Defense Center™ has seen a fresh wave of attacks targeting Blockchain wallet users. The attacks aim to steal all the information needed to hijack unsuspecting victims’ wallets and syphon off their hard-earned crypto gains. In the past week, we have detected more than 180 of these malicious emails, all reported by customers’ users.
Here’s how the phishing emails work.
Red Flag #1: ‘You Have Been Chosen.’
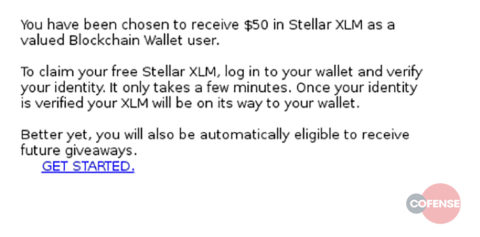
In the message below, we can see that the victim has been “selected to receive” a $50 dollar amount of Stellar (XLM), an up and coming crypto currency. Better yet, they will be automatically eligible to receive future giveaways. Wow! This common attack method works because, well, who doesn’t like free money?
Fig 1. Email Body
Red Flag #2: The Dreaded Embedded Link
If we take a deeper look into the message body, we can see that there is an embedded hyperlink <hxxps://mysccess[.]lpages[.]co/blockchain/> From this, we can instantly tell something is not right. We can also see that the website linked to is NOT the official Blockchain wallet login page “https://login.blockchain.com/#/login”
You have been chosen to receive $50 in Stellar XLM as a valued Blockchain Wallet user. To claim your free Stellar XLM, log in to your wallet and verify your identity. It only takes a few minutes. Once your identity is verified your XLM will be on its way to your wallet. Better yet, you will also be automatically eligible to receive future giveaways. GET STARTED.<hxxps://mysccess[.]lpages[.]co/blockchain/>
Fig 2. Email Body in Plain Text
Red Flag #3: Indicator of Compromised Mailbox
From the email headers we can see that the threat source originates from the domain ame.gob.ec. This domain belongs to an Ecuadorian municipal government body. We also note that the email headers do not appear to be spoofed in any way apart from the “Nickname field” has been change to “Blockchain.” This would indicate that the mailbox used to send the phishing campaign has itself been compromised.
From: Blockchain <__________@ame.gob.ec> Subject: Your airdrop of $50 is ready Thread-Topic: Your airdrop of $50 is ready Thread-Index: ozUHxyzm9QIDwDzmfizGH/nj/m+1AA== Importance: high X-Priority: 1 Date: Tue, 7 May 2019 12:03:45 +0000 Message-ID: <[email protected]> Content-Language: fr-FR
Fig 3. Email Headers
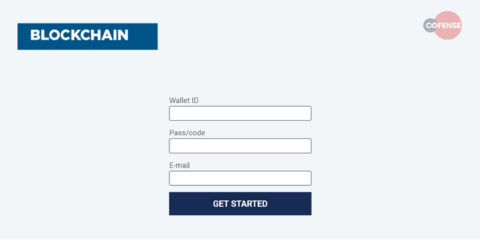
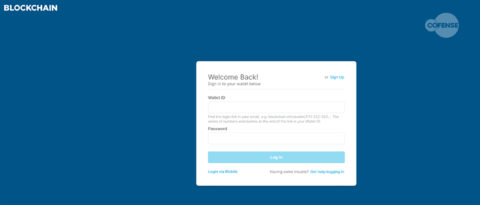
Phishing Page: The main phishing page is a simple imitation of the https://login.blockchain.com/#/login page, but it contains the ability to steal all the information needed for an attacker to fully compromise your bitcoin wallet: wallet ID, passcode, and email address. Once the details are filled in, it will redirect to the legitimate blockchain site.
Fig 4. Phishing Page
Right through the Gateway!
During our analysis, we noticed that the phishing email passed right through two different email security solutions: Forcepoint and Microsoft Anti-Spam and Anti-Malware solution in Office 365.
Conclusion: Again, we’ve detected 180+ of these emails in the past week alone. In recent headlines, hackers stole bitcoin worth $41 million from Binance, one of the world’s largest cryptocurrency exchanges, using a number of techniques including phishing emails. The attack was the latest in a string of thefts from cryptocurrency exchanges around the world. Be sure to educate users about phishing threats in general and Bitcoin wallet phishing in particular!
Learn more about the Cofense Phishing Defense Center. See how we analyze user-reported emails to provide actionable threat intelligence.
IOC’s
hxxps://mysccess[.]lpages[.]co/blockchain/
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. [/vc_column_text][/vc_column][/vc_row]