[vc_row][vc_column animation_iteration=”1″][mvc_infobox info_style=”mega_info_box_2″ info_opt=”show_icon” icon_size=”35″ icon_height=”75″ icon_radius=”15px” border_width=”2″ title_color=”#cd202c” font_icon=”fa fa-exclamation-triangle” icon_color=”#cd202c” border_clr=”#dd3333″ info_title=”Gateways Bypassed” title_size=”25″ css=”.vc_custom_1583878355515{margin-top: 20px !important;margin-bottom: 30px !important;}” hoverclr=”#cd202c” icon_bg=”#ffffff” hoverbg=”#ffffff”]
Symantec
[/mvc_infobox][/vc_column][/vc_row][vc_row][vc_column][vc_column_text c_id=”.vc_1597861508515″]By Jake Longden
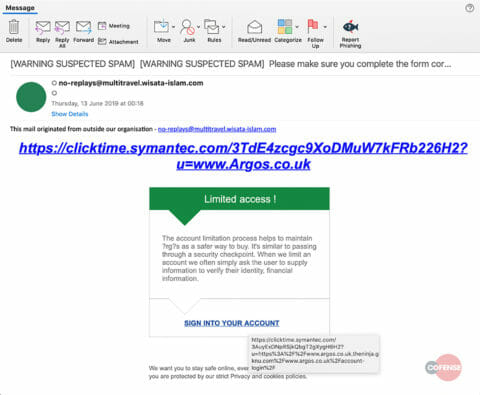
The Cofense Phishing Defense Center™ has observed a phishing campaign that purports to be from Argos, a major retailer in the UK and British High Street. During 2018, Argos was the subject of a large number of widely reported phishing scamsi; this threat specifically targets Argos customers for their personal information and looks like a continuation of what was seen last year.
With the goal of stealing your store credit card and login information, here’s how it works:
All third-party trademarks referenced by Cofense™ whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks.
Fig 1. Email Body
Email Body:
The message itself follows a standard phishing template to inform the user that their account has been restricted and that user sign in is required for verification. The use of bad grammar and typos are a dead giveaway that this email communication is not genuine.
Message body in plain text:
In reviewing the body of the email, we see the hyperlink for “Sign into your account” which directs the potential victim to: hxxps://www[.]argos[.]co[.]uk[.]theninja[.]gknu[.]com/www[.]argos[.]co[.]uk/account-login/
The attacker repeatedly used the string of the legitimate Argos site in the URL, both as part of the subdomains, and as a subdirectory. This was an attempt to mask the true source, and to lure the victim into trusting the legitimacy of the website.
Upon examination, we see that the link is wrapped by a URL filtering service.
href="hxxps://clicktime[.]symantec[.]com/3AuyExDNpRSjkQbgT2gXygH6H2?u=hxxps://www[.]argos[.]co[.]uk[.]theninja[.]gknu[.]com/www[.]argos[.]co[.]uk/account-login/" target="_blank" rel="noopener"><span class="ox-dad7652f0e-m_609589041267919212link-blue ox-dad7652f0e-m_609589041267919212MsoHyperlink ox-dad7652f0e-m_609589041267919212MsoHyperlinkFollowed">SIGN INTO YOUR ACCOUNT
Fig 2. Email Body in Plain Text
Email Headers:
Analysis of the headers indicates that the “from” address is spoofed; the “reply to” field contains the address ‘no-reply[@]creativenepal[.]org’, which does not match ‘no-replays[@]multitravel.wisata-islam[.]com’.
Research on the ‘multitravel.wisata-islam’ domain failed to produce relevant data and reinforces the suspicion that the address is spoofed. At the time of analysis, we were unable to resolve an IP address, or load the domain.
From: <no-replays[@]multitravel[.]wisata-islam[.]com>
To: <[email protected]>
Subject: [WARNING SUSPECTED SPAM] [WARNING SUSPECTED SPAM] Please make sure
you complete the form correctly.
Thread-Topic: [WARNING SUSPECTED SPAM] [WARNING SUSPECTED SPAM] Please make
sure you complete the form correctly.
Thread-Index: AQHVIXUk7CjiCOKjHEyntcvh4etMFg==
Date: Wed, 12 Jun 2019 23:18:17 +0000
Message-ID: <[email protected]>
Reply-To: <“:no-reply”[@]creativenepal[.]org>
Fig 3. Email Headers
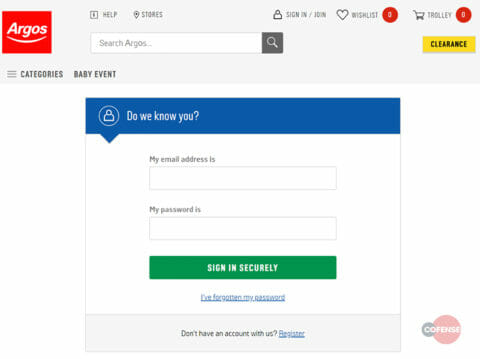
Phishing Page:
Once the user clicks on the “Sign into your account” hyperlink, they are redirected to a convincing imitation of the true Argos login page requesting the victims’ Username and Password.
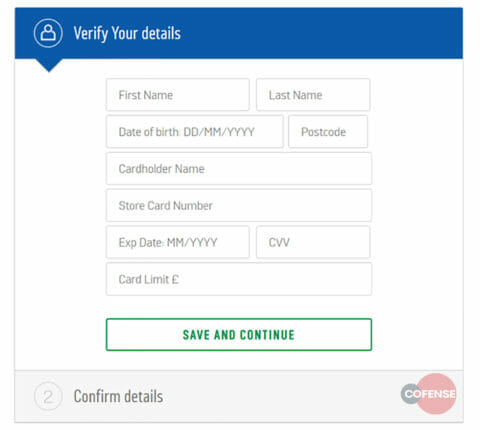
This then leads the user to a second page, where the user is requested to supply details for their Argos store credit card account. This page follows the standard format for regular credit/debit cards with one key difference: the additional request for a ‘Card Amount’. This request is specific to the Argos Card as referenced in the copy: “The Argos Card lets you shop at Argos, with flexible payment plans that give you longer to pay” (see: https://www.argos.co.uk/help/argos-card/apply). This deviates from standard forms by asking the user for their credit limit.
Fig 4. Phishing Page
Gateway Evasion:
This campaign has been observed to pass through the ‘Symantec Messaging Gateway’.
We can see the influence of the Email gateway which injected ‘Warning Suspected Spam’ headers to the Subject Line and incorrectly presented this phish as a benign marketing email, and not a phishing attempt.
Conclusion:
To help protect against this type of credential phish, Cofense PhishMe™ offers a template called “Account Limitation” in order to improve phishing awareness training.
This credential phish eluded gateways and was actually mis-identified as harmless marketing spam. In fact 75% of threats reported to the Cofense Phishing Defense Center are Credential Phish. Protect the keys to your kingdom – condition end users to be resilient to Credential Harvesting attacks with Cofense PhishMe.
All third-party trademarks referenced by Cofense™ whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks.
i Google Search “Argos Data Breach 2018”[/vc_column_text][/vc_column][/vc_row]