The Cofense Intelligence team released its Quarterly Phishing Intelligence Review for the second quarter of 2022, which highlights significant shifts in the phishing threat landscape, with some key takeaways highlighted below. 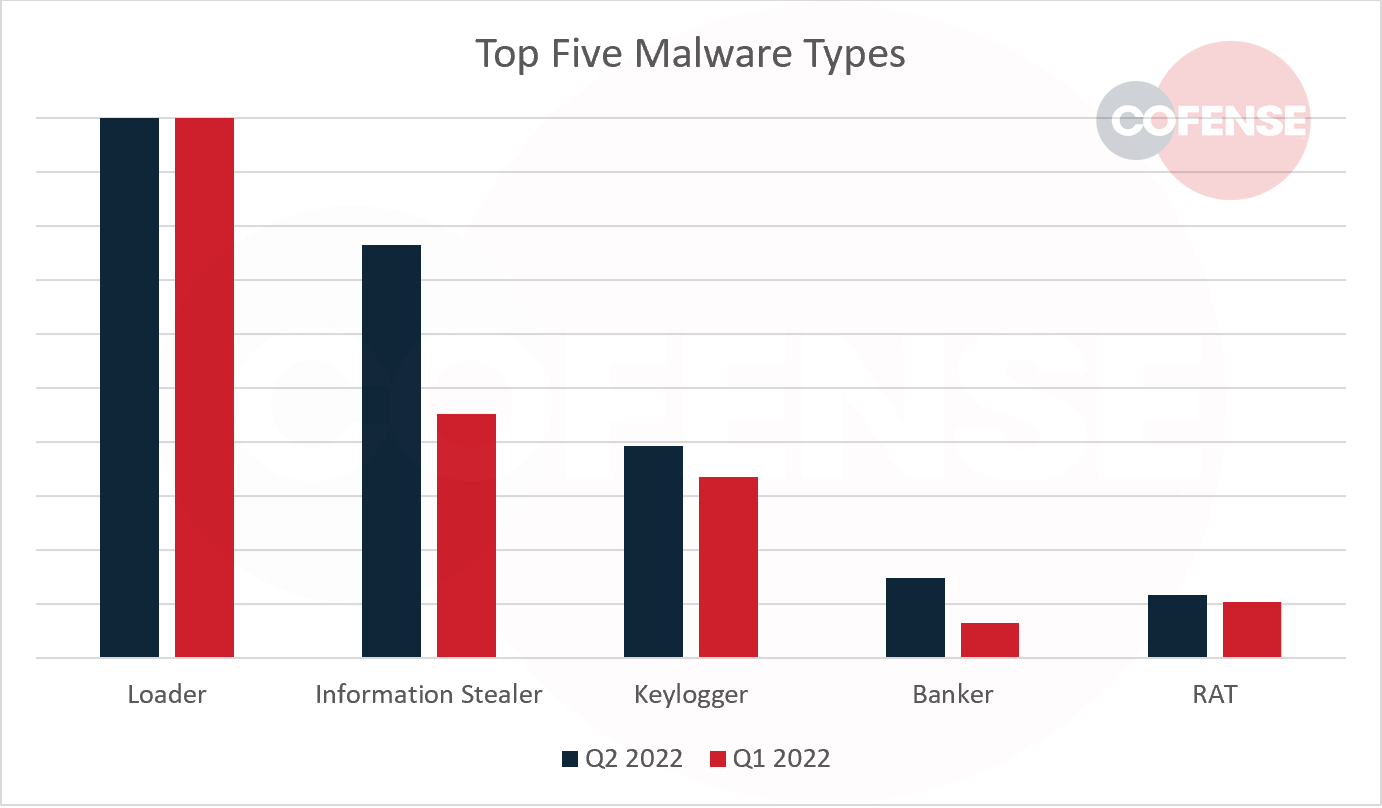
Top five malware types in Q2 2022 and Q1 2022, by volume of emails.
- Emotet campaigns continued to sustain, however their overall volume dropped significantly compared to the first quarter of 2022, leading to an overall reduction in phishing activity. However, don’t get too comfortable. Four of the top five malware families most frequently delivered via phishing (FormGrabber, Agent Tesla, QakBot, and Remcos RAT) all saw increases in volume.
- Changes in QakBot delivery tactics made QakBot a far more potent threat. Phishing campaigns delivering QakBot became the most effective in terms of reaching end users. QakBot campaigns now go to extensive lengths to bypass security measures, avoid detection, and obstruct analysis tactics. Read the report for more details regarding these effective tactics.
- Business Email Compromise (BEC) campaigns continue to impart more financial loss on companies than any other cyber threat. Our team dove into what it looks like when a target interacts with a BEC actor as part of our latest strategic analysis.
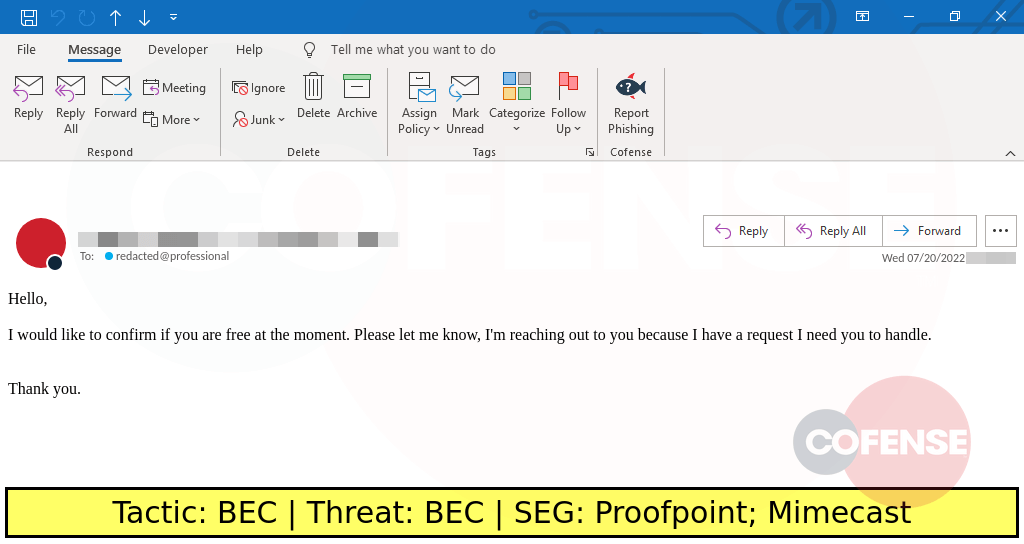
BEC Campaigns Like The One Above Reach End Users Regularly