Author: Kian Maher
In recent weeks, the Cofense Phishing Defence Center (PDC) has noted a number of emails utilising the SwissTransfer service to achieve successful phishes against recipients. A common vector and preferred vector for attackers, file sharing services such as WeTransfer, Microsoft OneDrive and Dropbox have been utilized to spread files containing anything from scams to malware leading to ransomware.
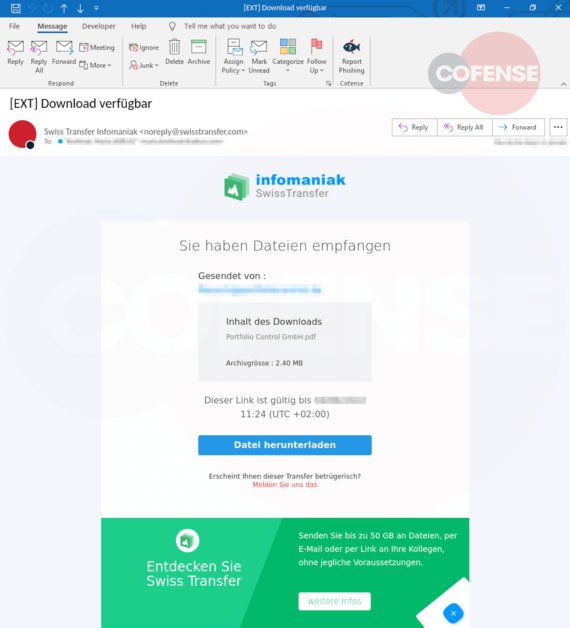
Figure 1: Phishing Email
Based in Switzerland, this file sharing service has been seen mostly in attacks against users of German speaking nations. The file sharing capabilities and clean image of the site can easily trick a user into downloading a file they believe is legitimate and from a known contact; however, with the ability to add any alias to a sent file, impersonation becomes exceedingly easy.
Navigating to the link on the email will present the user with a legitimate SwissTransfer download page where a PDF file named “Portfolio Control GmbH.pdf” can be downloaded by the user, as seen in Figure 2.

Figure 2: File Download Page
Once the file has been downloaded, and the recipient opens the PDF, clicking on the link will redirect the user to a Microsoft login page.
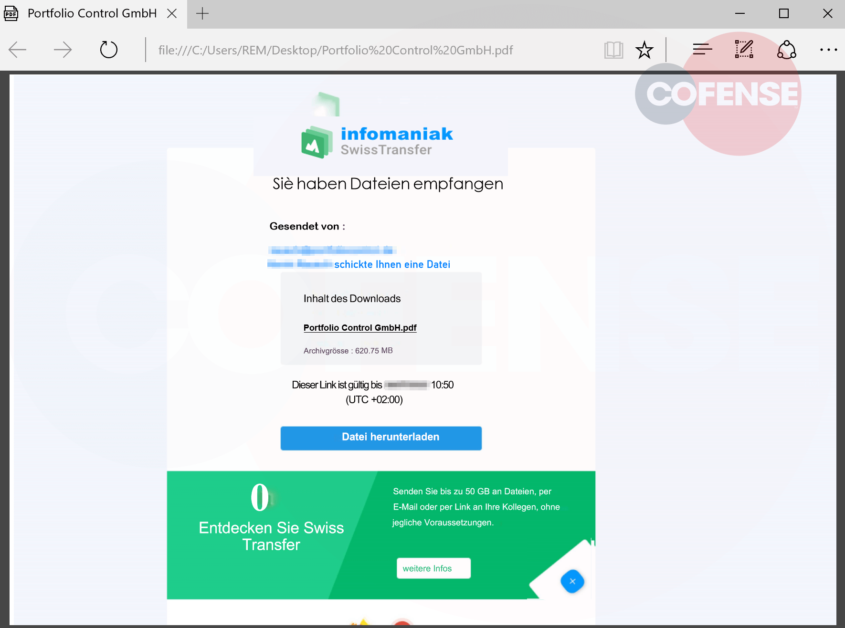
Figure 3: PDF Document
The login page spoofs the standard Microsoft layout and the only indicator that something is amiss is the URL seen in the address bar.
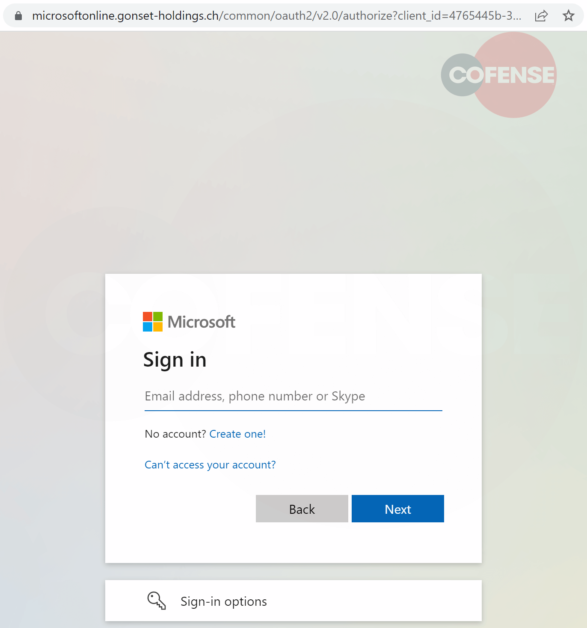
Figure 4: Landing Page
Beware of emails coming from legitimate services such as SwissTransfer, WeTransfer and Microsoft OneDrive, as phishing attacks are constantly evolving and are becoming more convincing and complex by the day. Equally as important is to ensure the same password is never used for more than one account. Additionally, never perform any password resets or account retrievals outside of the legitimate website of any email provider you use or through a corporate environments’ approved methods.
Malicious emails like this are a constant threat in the enterprise space due to constant use of services such as Microsoft Outlook and it is important that users are made aware of this so that they can be more vigilant when receiving emails. With Cofense suite of products and services, malicious emails can be identified, and indicators of compromise (IOC)’s given and shared. Find out what we can do for your enterprise.
| IOC | IP |
| hXXps://www[.]swisstransfer[.]com/d/3835eb76-db5c-4e5a-9aa6-044bac8b46ce | 185.125.25.5 |
| hXXps://microsoftonline[.]gonset-holdings[.]ch/common/oauth2/v2.0/authorize | 190.123.44.153 64.98.145.30 |