By Caleb Karr, Cofense Phishing Defense Center
As our daily lives become increasingly dependent on the internet for services, attackers are finding new and innovative ways to steal personal information from unconventional platforms. Many users use streaming services like Spotify and Apple Music for their convenience, often sharing their listening habits and preferences with friends or followers. Unfortunately, cybercriminals are highly aware of these popular platforms and culturally relevant trends, and they exploit users' trust in these services to deceive them into compromising their accounts. It's important to remember that while these services offer ease and entertainment, they can also become targets for threat actors looking to steal personal information when we least expect it. The Cofense Phishing Defense Center (PDC) team detected a spoofed Spotify email claiming a payment failure and urging users to log in and update their accounts. This is a double-barrel attack: first, attackers capture login credentials, then prompt users to update payment information. While losing access to a Spotify account is inconvenient, the theft of credit card information poses an even greater risk.
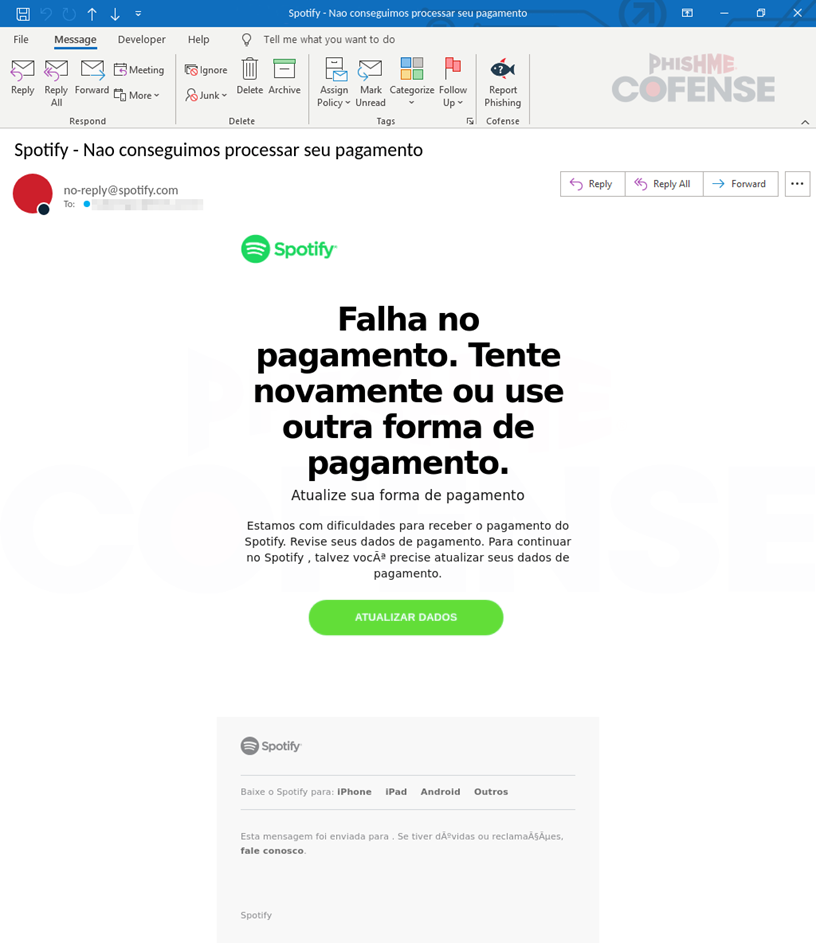
At first glance, this appeared to be a legitimate Spotify email, featuring Spotify’s branding and functional URLs that redirected the user to the Spotify web player. However, upon further investigation, we identified several red flags. First, a header analysis revealed that the email had been spoofed by a malicious actor. While the displayed “From” address appeared as “no-reply@spotify.com,” a deeper examination of the email headers indicated otherwise. The ‘Return-Path’ field, along with other header details, showed that the email was sent from a different domain, “ns3130981.ip-51-75-52.eu” rather than an official Spotify domain. This discrepancy confirmed that the email was not genuinely from Spotify.
.png)
Figure 1: Email Body
Additionally, the content of the email raised suspicion. The message attempted to coerce the user into logging in and updating payment information, which is a common tactic in phishing attacks. After confirming that the email was spoofed, our team conducted a URL analysis. Although the threat actor had inserted several legitimate Spotify URLs to obfuscate the malicious intent, we were able to open the HTML body and uncover a hidden, malicious URL embedded in the green “Update Data” button. The URL (hXXp://40[.]82[.]178[.]115/player/pt-br/) was a clear indication of a phishing attempt.
.png)
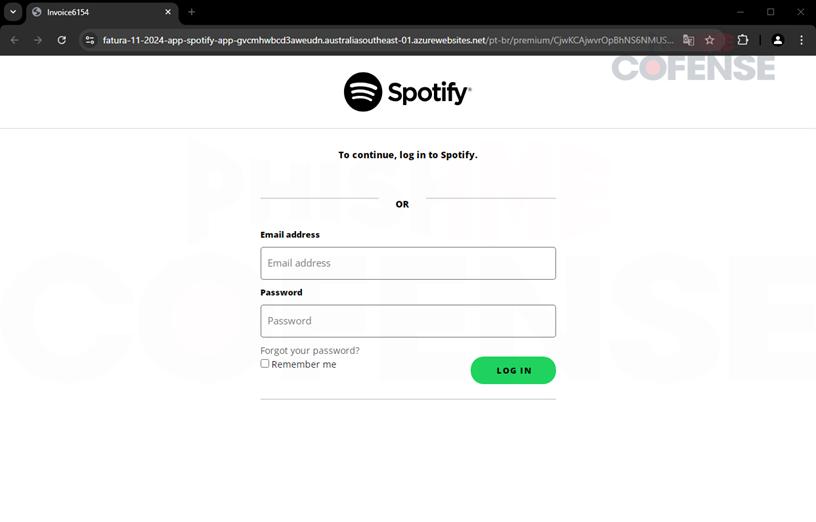
Figure 2: Phishing Page
After clicking the link, victims were redirected to a Linktree page designed to funnel them to malicious sites. The page, which mimicked Spotify's branding, falsely claimed to be an official invoicing page. Once users clicked the "Update Payment Method" button, they were directed to a malicious web page hosted on Azure App Service.
.png)
Figure 3: Phishing Page
The phishing landing page, resembling a cloned Spotify login, contained a suspicious URL with keywords like "fatura" (Portuguese for invoice), “app”, and “Spotify”. However, the default root domain “azurewebsites.net” confirms the page is unrelated to Spotify. The page allowed users to enter their credentials, or reset their usernames and passwords, which were then sent to a PHP C2 controlled by the threat actors.
.png)
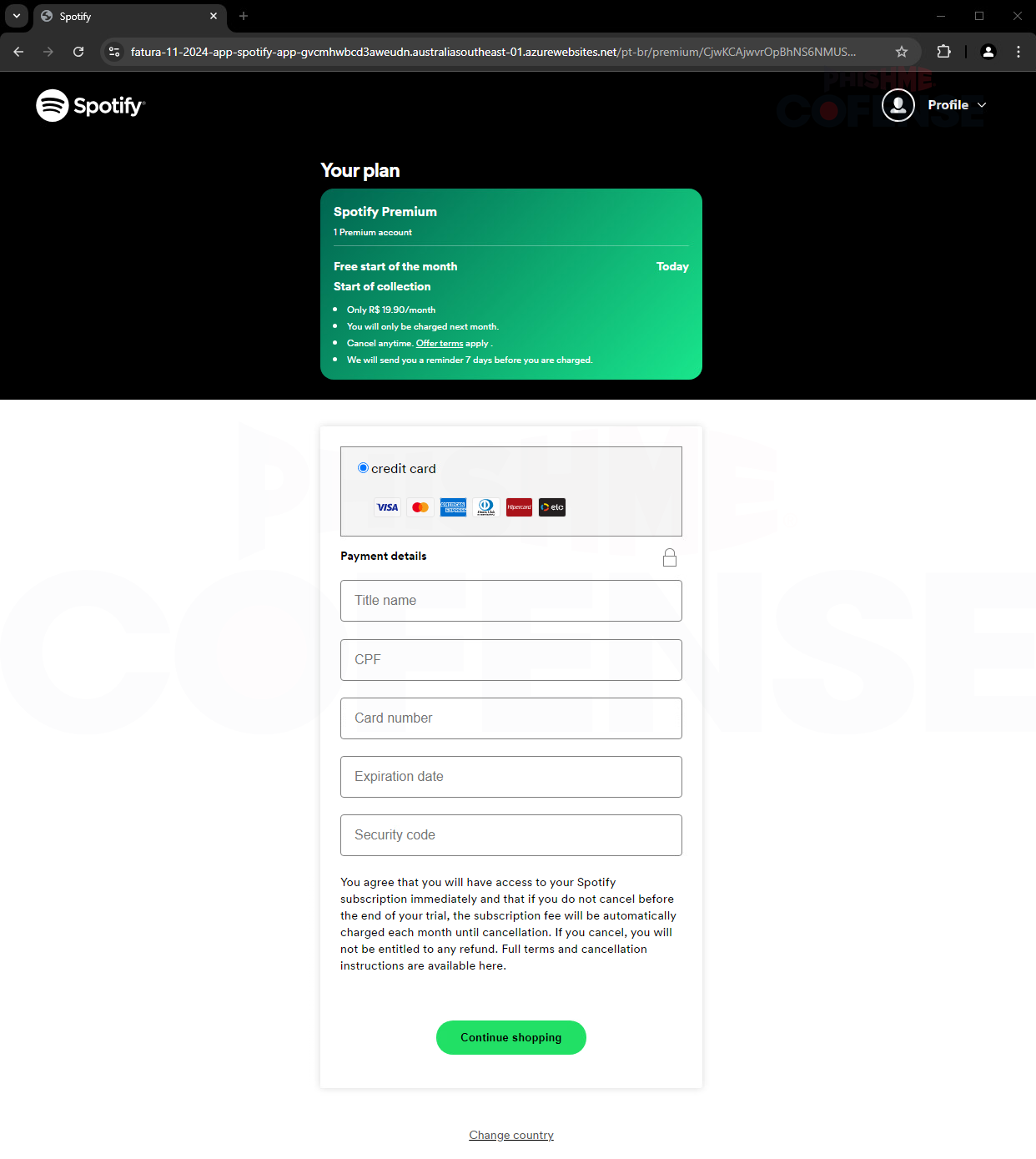
Figure 4: Phishing Page
Once the false credentials had been sent to the threat actors, the users were redirected to a page where they were prompted to fill in their credit card details under the guise of updating payment information. After users submitted their card information, it was sent again directly to a malicious PHP C2 controlled by the threat actors, allowing them to capture and store the data. But the deception didn’t end there.
Figure 5: Phishing Page
Users were then confronted with a final prompt asking for their “password issued by the bank,” which was intended to be a security measure for online transactions. By obtaining this extra information, the attackers could bypass certain security features and gain access to the user’s financial accounts. With all this stolen data, the cybercriminals could not only access the user's funds but also clone the card and potentially use it for fraudulent transactions or sell it on the black market. This multi-layered attack demonstrates the increasing sophistication of phishing schemes, where attackers use a combination of tactics to steal sensitive information and exploit it for financial gain.
In conclusion, while streaming platforms like Spotify and Apple Music offer convenience, they also pose risks to users' personal and financial security. The spoofed email targeting users during this campaign reveals the common tactics attackers use, such as leveraging familiar branding and urgency to deceive victims. This highlights the need for vigilance with unsolicited communications, especially those prompting sensitive actions like logging in or updating payment details. Additionally, it underscores the importance of cybersecurity practices, such as verifying senders, examining URL destinations, and maintaining unique passwords across platforms. As our reliance on the internet grows, staying cautious and alert is essential to protect personal data.
| Indicators of Compromise | IP |
|---|---|
| hXXp://40[.]82[.]178[.]115/player/pt-br/ | 40[.]82[.]178[.]115 |
| hXXps://linktr[.]ee/faturaspotifyapp20 | 151[.]101[.]130[.]133 151[.]101[.]194[.]133 151[.]101[.]66[.]133 151[.]101[.]2[.]133 |
| hXXps://fatura-11-2024-app-spotify-app-gvcmhwbcd3aweudn[.]australiasoutheast-01[.]azurewebsites[.]net/pt-br/premium/CjwKCAjwvrOpBhNS6NMUSICAAPPSPO827SHSAJJSARt04wMAwq59T6FH8l6dUQHvTv7fcMdHhoCoPkQAvD/index[.]html | 13[.]77[.]50[.]115 |
| hXXps://fatura-11-2024-app-spotify-app-gvcmhwbcd3aweudn[.]australiasoutheast-01[.]azurewebsites[.]net/pt-br/premium/CjwKCAjwvrOpBhNS6NMUSICAAPPSPO827SHSAJJSARt04wMAwq59T6FH8l6dUQHvTv7fcMdHhoCoPkQAvD/musicas/BR-PT/ChMI2IvPwKfR7QSMA8SMSPOT83MSSppAPP/default-trial[.]php | 13[.]77[.]50[.]115 |
All third-party trademarks referenced by Cofense whether in logo form, name form, product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding the circumvention of end-point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats. Past performance is not indicative of future results.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog, are registered trademarks or trademarks of Cofense Inc.