Author: Tonia Dudley
Report after report continue to highlight phishing as the top threat hitting organizations today, leading either to an incident or data breach. The most recent report published by IBM, report both Business Email Compromise (BEC) and Phishing as the leading cost of a data breach. In our recent webinar, we discussed various factors to consider in your email security program related to phishing well beyond the basics of phishing simulation.
For those that missed our webinar, below are three key insights that we discussed as ways to address ransomware as an organization.
During the webinar, we highlighted one of our recent blogs that allowed a customer to experience the ROI on their recent Vision implementation and enabling the auto-quarantine feature. With just a few users reporting this email to our Phishing Defense Center (PDC), the team was able to find another 130 emails which were automatically removed from inboxes company wide.
Key Takeaway #1 – Why we pioneer phishing simulation methodology
As organizations continue to mature their phishing defense program, there’s often many questions around how much, how frequent and when can we stop. We discussed the reason for creating a safe place for the user to experience the threat in the same place they manage their email. We highlighted several do’s and don’ts as you run your program, including the reason to align simulations to the threats your organization is experiencing.
Key Takeaway #2 – Metrics that matter to your Phishing program
Your phishing program is more than your simulation click rate. For years we’ve stressed the importance of focusing on the number of users reporting. Even more critical is combining this data with your real phishing threats. Are you looking at your program holistically to ensure you’re measuring what matters? Are you able to articulate to leadership the value you’ve invested in making sure your organization is protected against a phishing incident? Measure the time the email hits the inbox, beyond the user reporting it, to closing the ticket after full remediation of the phish (password resets, network block and end point scans or rebuild).
Key Takeaway #3 – Not everything needs to be a simulation template
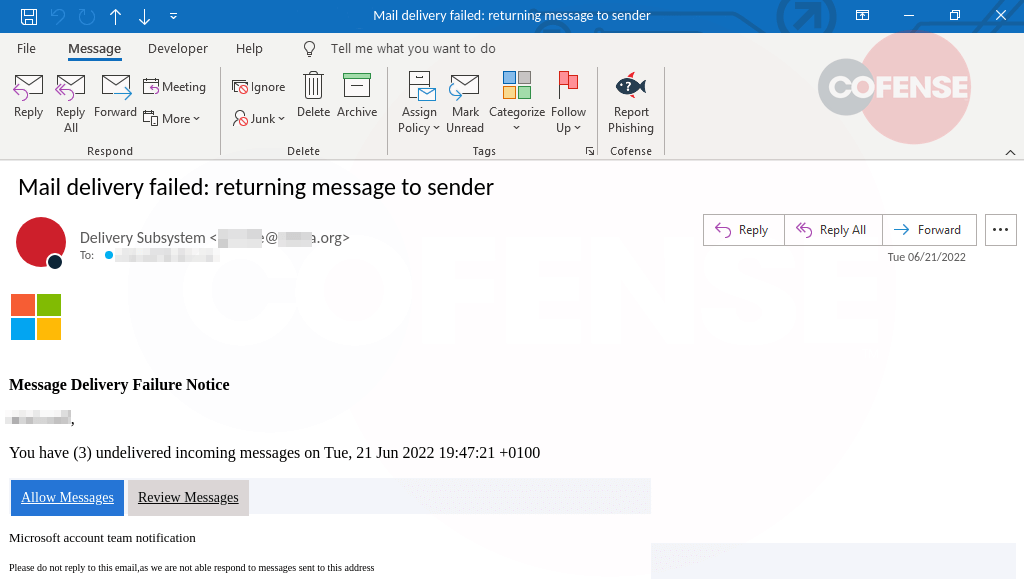
There are times when a threat emerges quickly, or a sensitive topic is being used in a real phishing campaign. This is when its critical to get the word out to your users to stay on alert. This is best done using a simple newsletter with images of the real phish.
For additional insights from our 2022 Annual State of Phishing Report webinar series:
- Three Highlights from the Cofense 2022 Annual State of Phishing Report
- SEG Effectiveness: Three takeaways from the 2022 State of Phishing Report
- BEC Insights: The Need for Better Business Controls