By: Kahng An, Intelligence Team
Cofense PDC (Phishing Defense Center) and Cofense Intelligence have found an Internal Revenue Service (IRS)-spoofing email that purports to give a $5000 tax refund provided by Elon Musk. However, the link to access the purported tax refund redirects to a credential phishing page with IRS and Elon Musk branding images. Upon filling out the credential phishing form, the victim is asked to access a fake cryptocurrency market where they will be given $5000 to withdraw after verifying a photo ID and bank account information. The extensive amount of personally identifiable information (PII) stolen in this campaign allows the threat actors to pivot to social engineering attacks on the victim’s personal financial, government, and online service accounts. This Flash Alert will briefly analyze the overall impact from the campaign’s email, credential phishing sites, and threat actor’s motivations.
Campaign Email
Emails from this campaign claim to be a $5000 tax refund benefit “from the IRS, courtesy of Elon Musk” which needs to be accessed via the included link. However, the link redirects to a credential phishing site that continues to spoof the IRS and Elon Musk while claiming to present a government form that is necessary to receive the tax refund. As shown in Figure 1, the email includes an IRS branded image header and sender name set to “Internal Revenue Service(IRS)”. Notably, the emails also include a legitimate IRS phone number in the footer. This phone number is the actual IRS phone number for the IRS Practitioner Priority Service and has likely been included by the threat actor to make the email seem legitimate.
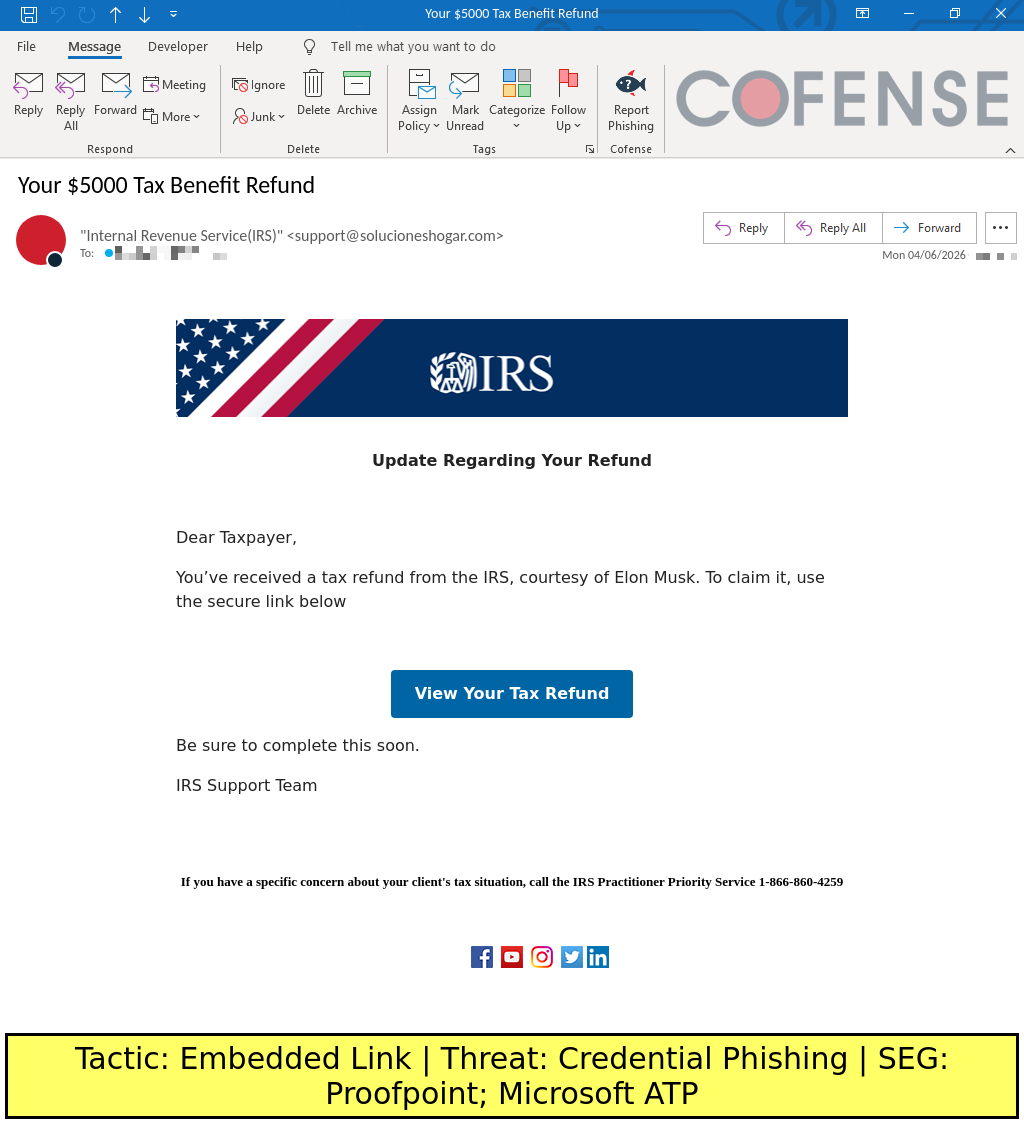
Figure 1: The campaign’s email template. Note the use of IRS branding and the included legitimate IRS Practitioner Priority Service phone number in the footer.
Credential Phishing
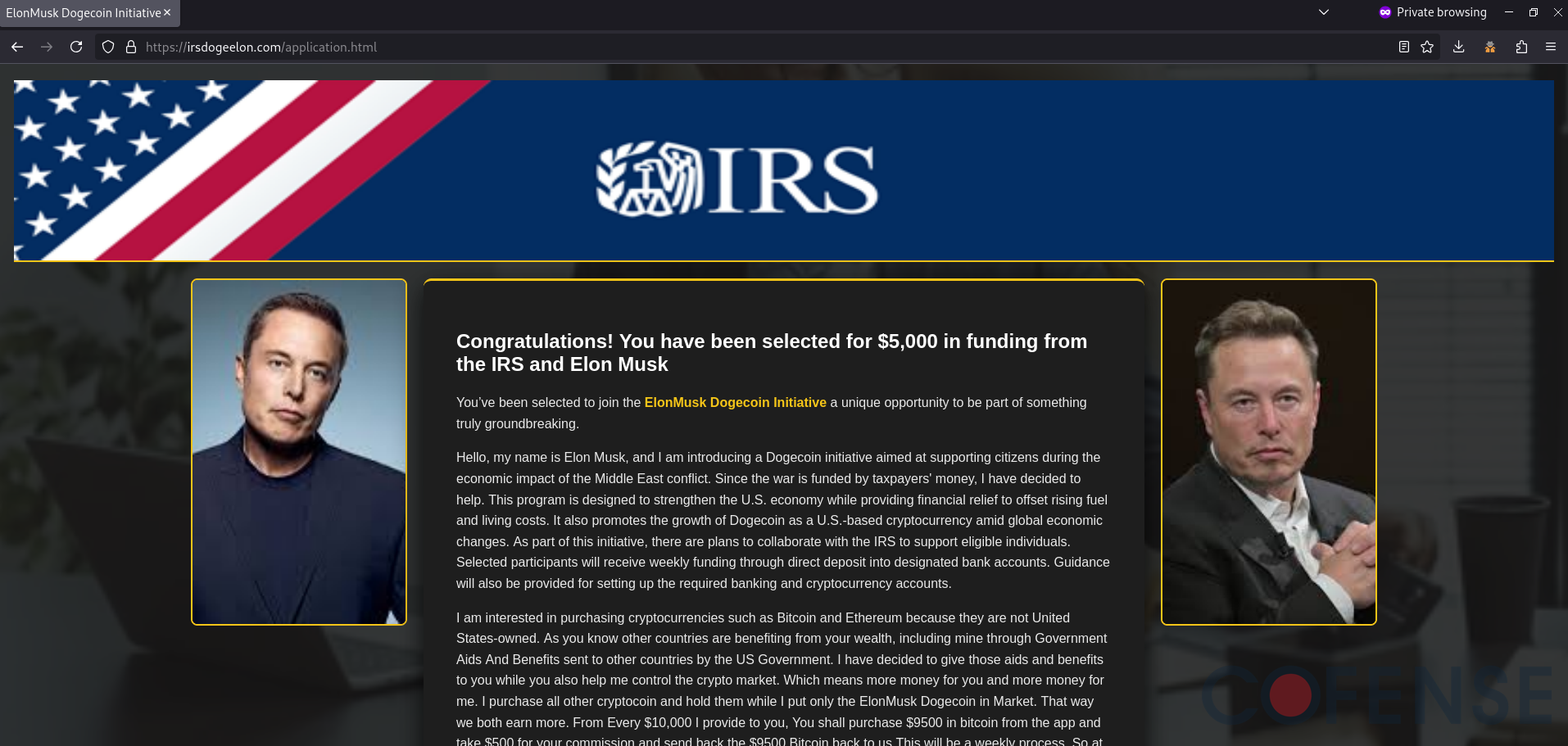
The embedded link in the email redirects to the credential phishing site shown in Figure 2. The site continues to use the same IRS branded image header and includes Elon Musk photos to make the site seem like an IRS and Elon Musk related site. The actual main message of the site shown in Figure 3 includes a lengthy speech about cryptocurrency and introducing this alleged new tax refund benefit called the “ElonMusk Dogecoin Initiative” due to the ongoing conflict in Iran. The speech purports that the tax benefit will include a one-time $5000 deposit and recurring $10,000 deposits that require purchasing $9500 in Bitcoin that will be returned back to Elon Musk as a part of this initiative. The threat actors use this speech to lead into the cryptocurrency scam part of this campaign, which is accessed after filling out the credential phishing form found in Figure 4.
.png?language=en)
Figure 2: The initial credential phishing site. Note the continued use of IRS branding assets and Elon Musk photos to make the site appear legitimate.
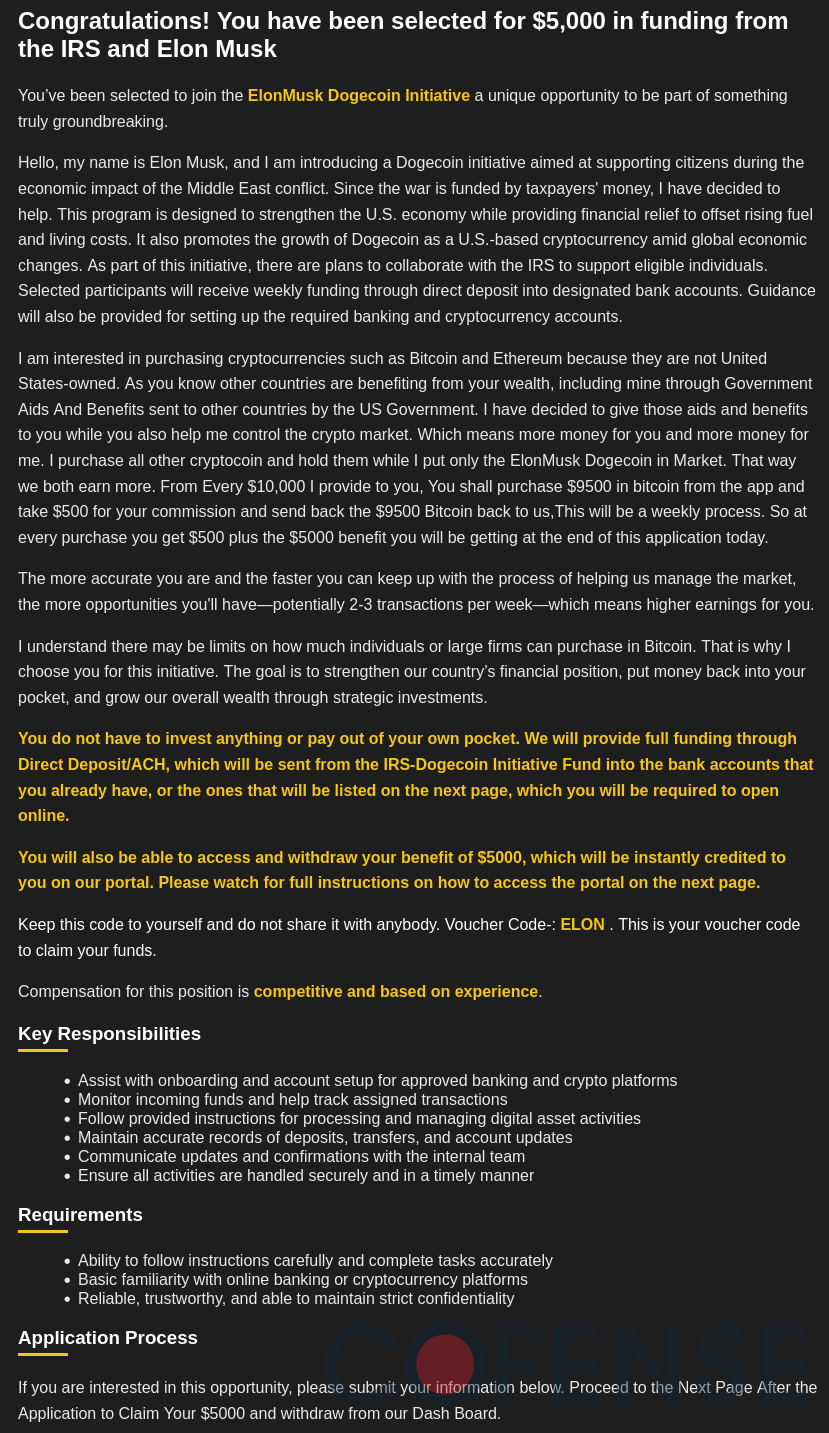
Figure 3: The full speech included in the credential phishing site. Note how it includes a cryptocurrency scam to receive a $10,000 direct deposit that requires returning $9500 in Bitcoin back to the threat actor.
Figure 4: The credential phishing form found at the bottom of the credential phishing site. Completing it will give the victim access to the cryptocurrency scam website.
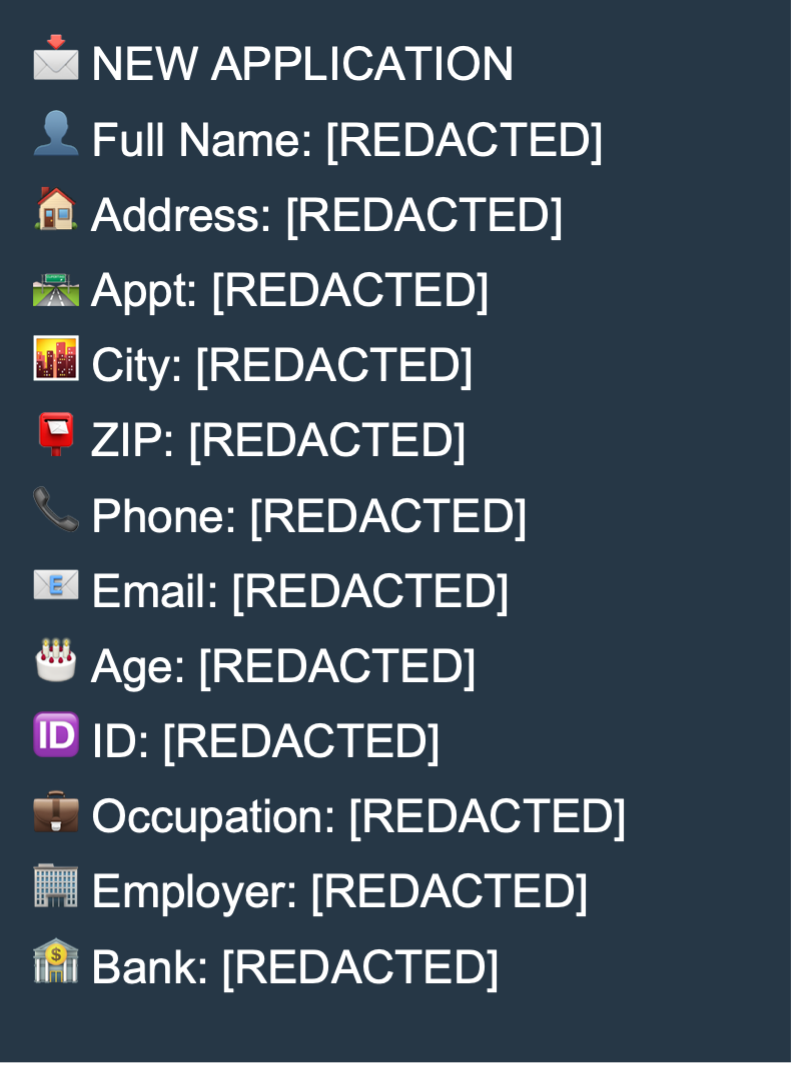
The threat actors exfiltrate the information included in the form via a Telegram bot. By using the sendMessage API call, the form contents are then sent out to a Telegram channel that the threat actor controls. The following is an example of what the exfiltration message looks like based off the API call.
Filling out the credential phishing form leads to another page that includes directions on how to access the cryptocurrency scam website. The victim is given instructions as shown in Figure 6 on how to claim their $5000 tax refund and further instructions onboarding for the alleged cryptocurrency initiative.
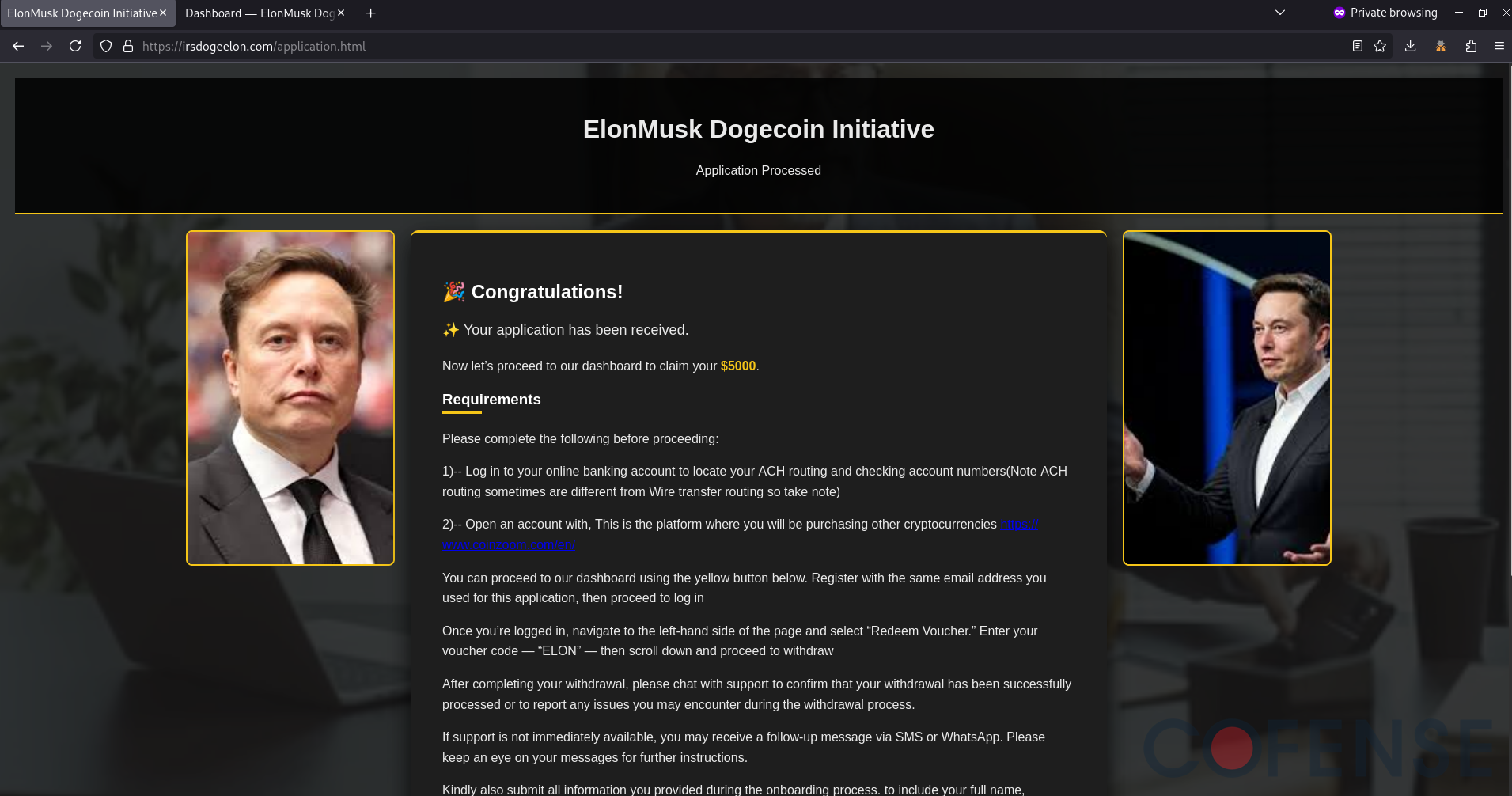
Figure 5: The website shown after completing the credential phishing form.
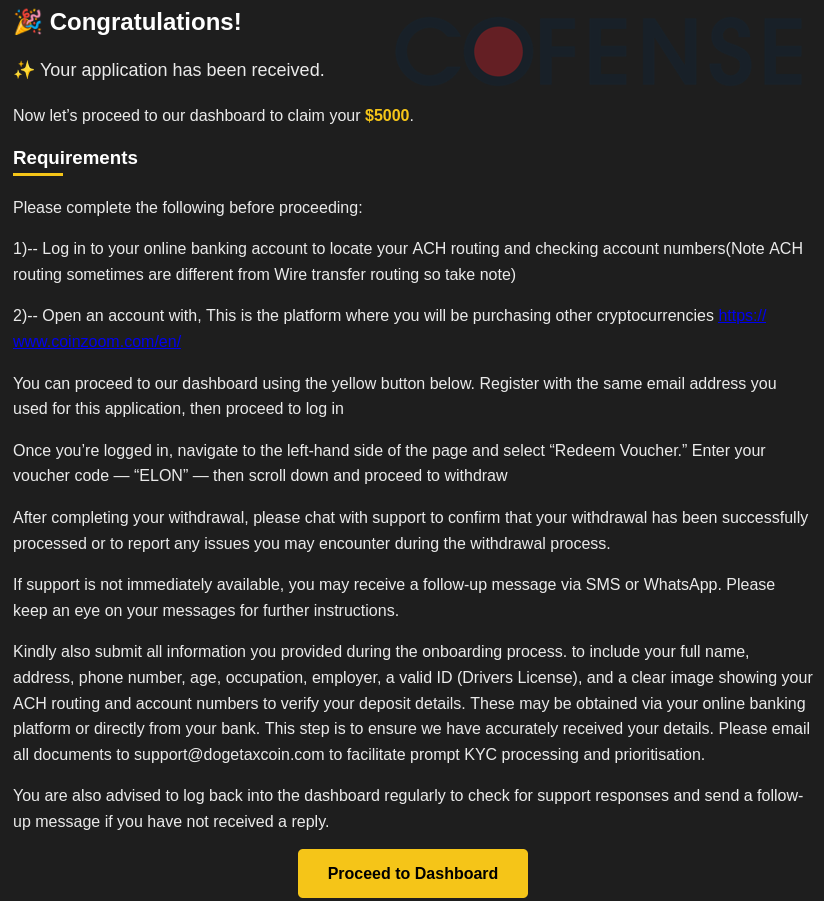
Figure 6: Instructions on accessing the cryptocurrency scam website. Note how the platform solicits additional information by asking for a valid photo ID and bank routing and account numbers.
Cryptocurrency Scam
The cryptocurrency scam website as shown in Figure 7 appears to be a cryptocurrency marketplace platform, though is primarily used to make the victim provide additional PII by submitting a photo ID (such as a driver’s license) and banking information. While there are many functions on this site, such as a cryptocurrency trade platform, this analysis primarily focuses on the $5000 benefit withdrawal and additional Bitcoin deposit parts of the scam.
Figure 7: The cryptocurrency scam website. Note how it continues to use Elon Musk photos to appear connected to the supposed ElonMusk Dogecoin Initiative. At this point in the campaign, IRS branding is no longer used.
Following the instructions from Figure 6, the victim is told to access the “Redeem Voucher” page to use code “ELON” to receive their $5000 deposit, which can then be withdrawn from the platform. Figure 8 shows the voucher redemption process, and Figure 9 shows that the alleged $5000 deposit is redeemed.
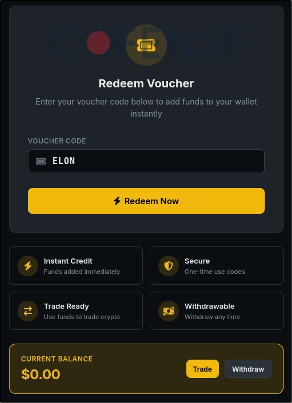
Figure 8: The voucher redemption form using code “ELON”.
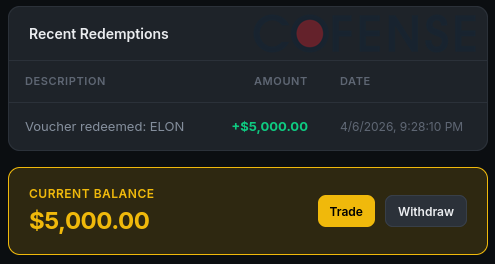
Figure 9: Upon redeeming the voucher, the victim’s balance on the scam website is updated to include the $5000 deposit.
Afterwards, the victim can attempt to withdraw funds, which prompts them with a message claiming that the withdrawals require being active on the cryptocurrency scam for three months. This allows the threat actors ample time to sway the victim into potential months of payments before the victim can expect to receive money.
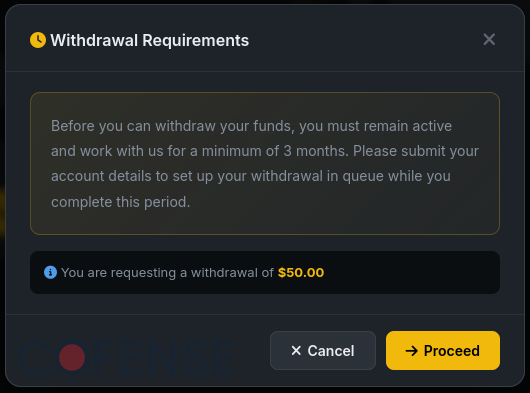
Figure 10: When attempting to withdraw funds, the site claims that withdrawals are only processed after three months of active participation on the site.
To join the withdrawal queue, the victim is prompted to upload a government-issued photo ID and banking account and routing numbers as a part of the withdrawal process.
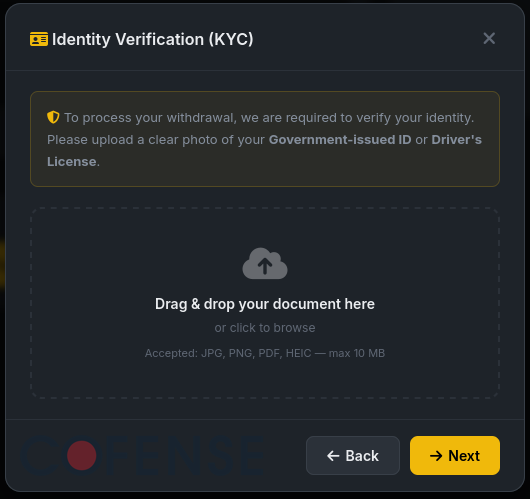
Figure 11: The scam asks the victim for a photo ID for verification purposes as a part of the withdrawal process.
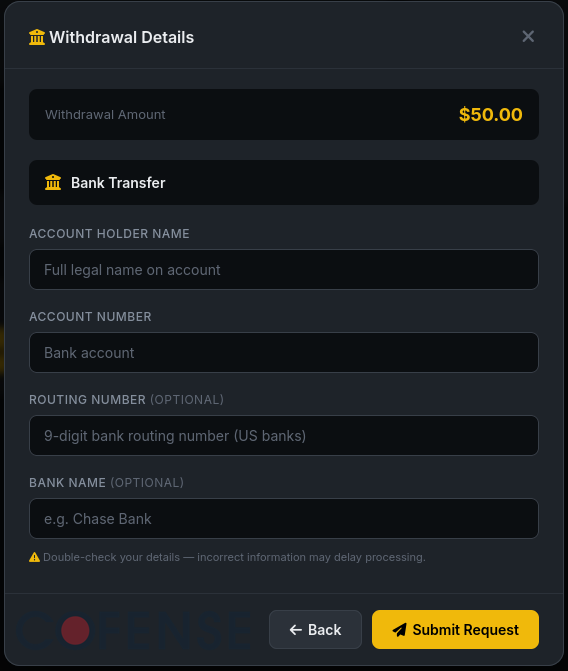
Figure 12: The scam also asks the victim for a bank account to allegedly do an ACH transfer to.
Using this information, the threat actors would be capable of much more sophisticated identity theft and social engineering attacks beyond the information exfiltrated from the credential phishing form in Figure 4. The threat actors would also be able to steal money directly from the victim’s bank account due to having access to the account and routing numbers.
Beyond the withdrawal process, the scam also includes a Bitcoin deposit page shown in Figure 13 that includes a wallet address that the victim is intended to send $9500 of the supposed $10,000 deposit to on a weekly basis.
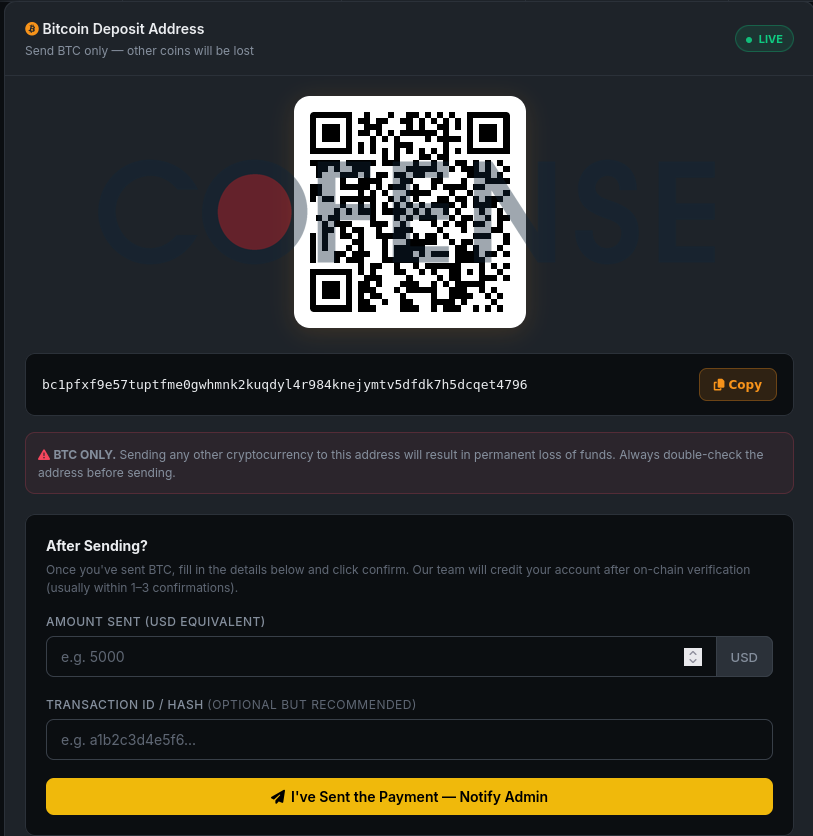
Figure 13: The threat actor’s Bitcoin address is included on the Bitcoin deposit page.
At the time of this report, the included threat actor Bitcoin address appears to have zero transactions on the blockchain, meaning that no Bitcoins have been sent to or withdrawn from this wallet.
Ultimately, this campaign highlights how modern phishing attacks have evolved into multi-stage fraud operations that blend social engineering, credential theft, and financial exploitation into a single seamless experience for victims. Organizations must move beyond traditional email security and empower users to recognize and report sophisticated threats before they escalate into full compromise. At Cofense, we combine human-driven defense with advanced phishing detection to stop attacks like these at every stage. To see how your organization can strengthen its resilience against today’s most deceptive campaigns, schedule a personalized demo with one of our experts today: https://cofense.com/demo