By: Max Gannon
Regardless of the device it is installed on or how it got there, most malware steals information from the platform it has infected. The question is, what do the threat actors controlling the malware do with the stolen information?
We are going to take a look at what kind of information is stolen by some of the top malware families, what threat actors do with the stolen information, and what value the stolen information has. We are also going to briefly cover how Initial Access Brokers (IABs) fit into the threat landscape in relation to what kind of access some of the top malware families pursue.
The price ranges used for the information gathered were derived from a number of dark web marketplaces.
Information Collected and Activities
Each of the following malware families has different methods of collecting the information that they steal but the end result is the same; threat actors can recover a trove of stolen data from each computer that they infect. However, the actual prices are so low that, for most threat actors, crime really does not pay well.
The following are some highlighted malware families consistently seen in the top 5 over the last year. It is worth noting that each one originally fell into a different malware “type” with QakBot breaking the trend over the years until it became the multifeatured malware that it is today.
Emotet is being excluded due to lack of recent activity, but it is worth noting that Emotet’s primary functionality became acting as a malware loader with increasingly less focus on stealing credentials.
QakBot
QakBot began as a relatively straight forward banker with a basic self-propagation component. It has since advanced to the point that, with all plugins loaded, it can act as a fully featured Information Stealer, log keystrokes, perform reconnaissance, spread laterally, load additional malware, and generally act as a Remote Access Trojan (RAT).
The Information Stealer plugins are advanced enough that it searches not just installed applications but also system files used to store password hashes.
As a result, it quickly attains the level of access needed to be able to sell access to the computer to an Initial Access Broker. In fact, QakBot is well known for consistently providing IABs with access and is particularly known for selling access to threat actors who deliver ransomware.
Agent Tesla Keylogger/Snake Keylogger
Agent Tesla Keylogger and Snake Keylogger are two of the top malware families seen by Cofense, but they have remarkably similar capabilities. In fact, the only significant difference is that Snake Keylogger can also interact with the victim’s clipboard.
Otherwise, they are both able to act as a Keylogger, take screenshots, and perform some basic credential recovery from browsers, FTP programs, and mail clients. Given their limitations and general inability to accept commands, these Keyloggers are unable to perform additional actions that would be required to sell access.
FormBook
Despite being designed as an Information Stealer, FormBook has a suite of capabilities far beyond what is typical for a basic Information Stealer. FormBook is capable of keylogging, file management, clipboard management, screenshotting, network traffic logging, and password, cookie, and form recovery from browsers.
A picture of a FormBook web panel, including the various programs targeted by the stealer, can be seen in Figure 1. Making use of FormBook’s ability to run remote commands as well as download and execute files, threat actors could use a basic FormBook infection to install additional malware and tools, allowing them to sell access to the computer to an Initial Access Broker.
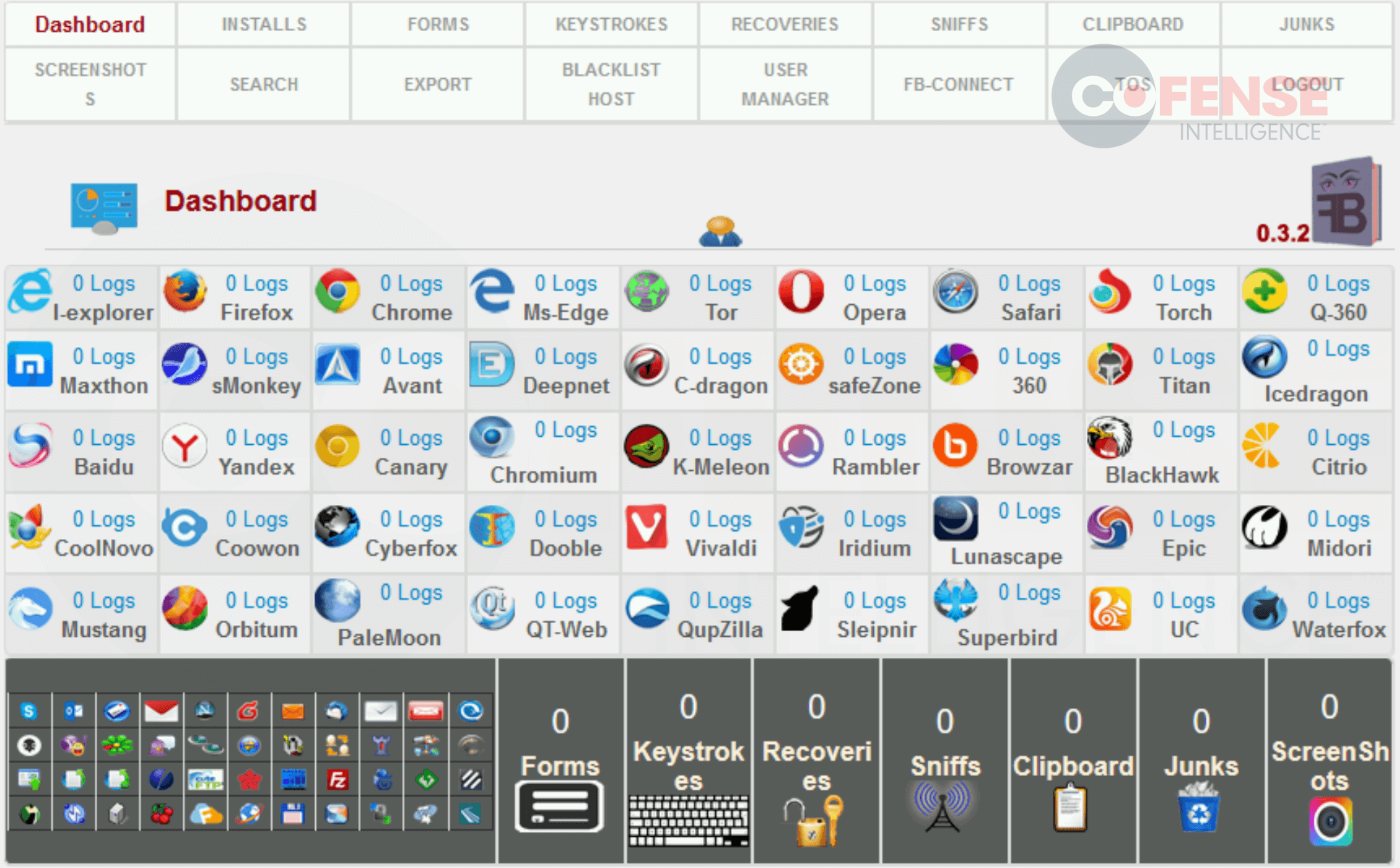
Figure 1: FormBook web panel displaying tools and targets.
Remcos RAT
Remcos RAT is a fully functional Remote Access Trojan, which means it has a large number of built in capabilities. These include keylogging, file management, clipboard management, screenshotting, password and cookie recovery, and camera and microphone logging.
Moreover, because it is a RAT, threat actors are allowed full access and can do just about anything to the computer if they are careful. This means that if the threat actors are careful about how they establish their foothold they can sell access to the computer to an Initial Access Broker.
Value of Access and Initial Access Brokers
Initial Access Brokers (IABs) offer some of the most expensive services found on dark web forums and marketplaces. Specifically, they offer initial access to infected systems. This access is gained by threat actors such as the ones behind QakBot when the successfully infiltrate a system.
There are many different types of access but, the most important aspect is to note that they are often gained my malware as part of the infection process. Initial access is used for a variety of purposes from extortion to loading additional malware to delivering ransomware.
The payoffs from these actions can be significant, therefore, access is a hot commodity and has been sold for hundreds of thousands of dollars based on the company that has been compromised. Of course, for individual home computers access can be sold for $5 or less so there is a significant range.
According to most industry experts the average cost of initial access is just under $3,000. The financial incentive of that payoff (compared to an average of $1.5 for full botnet logs of an infected computer) means that advanced threat actors typically look to achieve access that can be sold in addition to stealing all the information that they can.
Value of Information Stolen
Stolen information can be sold in many different ways and comes in many different types. Most of it is sold in batches of up to several hundred on dark web marketplaces where the stolen information has typically not been verified as being accurate or usable by the seller, even when they claim to have verified it. Instead, the buyer must check the information. If it has problems, the buyer must then provide proof to the seller within a certain time frame in order to receive a refund.
Given how easy it would be to fake that the information is invalid in order to get a refund, this system seems to be run with a surprising amount of trust that the buyer will not exploit the refund system. A small number of sellers do not offer refunds and instead seem to operate off of their reputation for providing quality information. The following sections cover some of the more commonly seen information that has the most sellers.
It is worth noting that these prices ranges were determined using multiple dark web marketplaces but there are a large number of marketplaces out there, including some particularly specialized ones, so the actual prices listed likely go for even less on one of the specialized marketplaces. Alternatively, some of this information likely goes for more when it is sold on an individual basis rather than in bulk.
Credit or Debit Card
Credit or debit cards with full addresses and associated information sell for anywhere from $10 each to $30 each depending on the nationality, amount of associated information, and type of card. This can also vary greatly depending on the marketplace, reliability of the seller, and number of cards sold in a batch. Refunds are typically available if the credit card has no balance or if the information is inaccurate.
Full Profile With SSN
A person’s full profile, including their SSN (or regional equivalent), address, etc. can go for anywhere from $2 to $5 per person and is often sold in batches of several hundred at a time. Refunds are typically available if the information is inaccurate. A threat actor can buy a person’s full profile and essentially ruin their life and credit score for less than stolen streaming service credentials.
An image of one store selling full profiles in bulk can be seen in Figure 2.
Figure 2: Dark web marketplace selling bulk full information bundles.
Online Retailer Credentials
The cost of credentials for an online retailer varies greatly but the most consistent range for a leading online retailer’s credentials was $0.10 to $5 per credential, and they were often sold in bulk of several hundred at a time. Unlike with many other sorts of information sold, if these username/password combinations are not correct there are no refund available.
Online Banking Credentials
The cost of credentials for an online bank also varies greatly, but this is more of a function of the balance available in the compromised account.
For example, for 200 sets of usernames and passwords for a leading financial organization that are not confirmed and have no refunds it costs $90.
For one account that is confirmed to have a balance of $458,462 it costs $4,500, as seen in Figure 3, and there are refunds if the information is inaccurate.
Botnet Logs
Another category of information is for Botnet Logs. These are all the information gathered on an infected computer, such as cookies, keystrokes, screenshots, and stored credentials and are typically sold based on network traffic.
For example, a compromised computer that has a record of network traffic to a leading financial organization is $30, one with network traffic to a different financial organization is $25, and one with traffic to Target is $5.
When these botnet logs are sold in bulk without any checking of their contents, they range from $0.50 per record to $2.50 per record.
Other Information
Other information trafficked on these websites includes credentials to social media websites, license keys, streaming services, small business email accounts, lists of valid emails to spam, and loyalty rewards programs, such as frequent flier miles, for rates like $4 for an account with 8612 miles.