By Don Santos, Cofense Phishing Defense Center
Online trading platforms are popular among investors. Both beginners and professionals use them to study the financial markets, manage investments, and make profits online. Interactive Brokers is one such trusted platform, known for its low pricing and global market access.
With presence in over 200 countries, the brand has now become a viable target for threat actors. The Cofense Phishing Defence Center (PDC) recently uncovered phishing campaigns impersonating Interactive Brokers, potentially putting accounts and financial investments at serious risk.
The campaign starts with an email shown in Figure 1. The subject appears to be an IRS Compliance Requirement from Interactive Brokers, requesting a renewal of Form W-8BEN. This form is a mandatory requirement for non-US individual account holders of Interactive Brokers (IBKR) to certify foreign status.
Users of the platform could easily view this as legitimate, but further examination says otherwise. Figure 1 below reveals that the sender email address is banking@pmcmlw.com, which is not the official email domain of Interactive Brokers (@interactivebrokers.com).
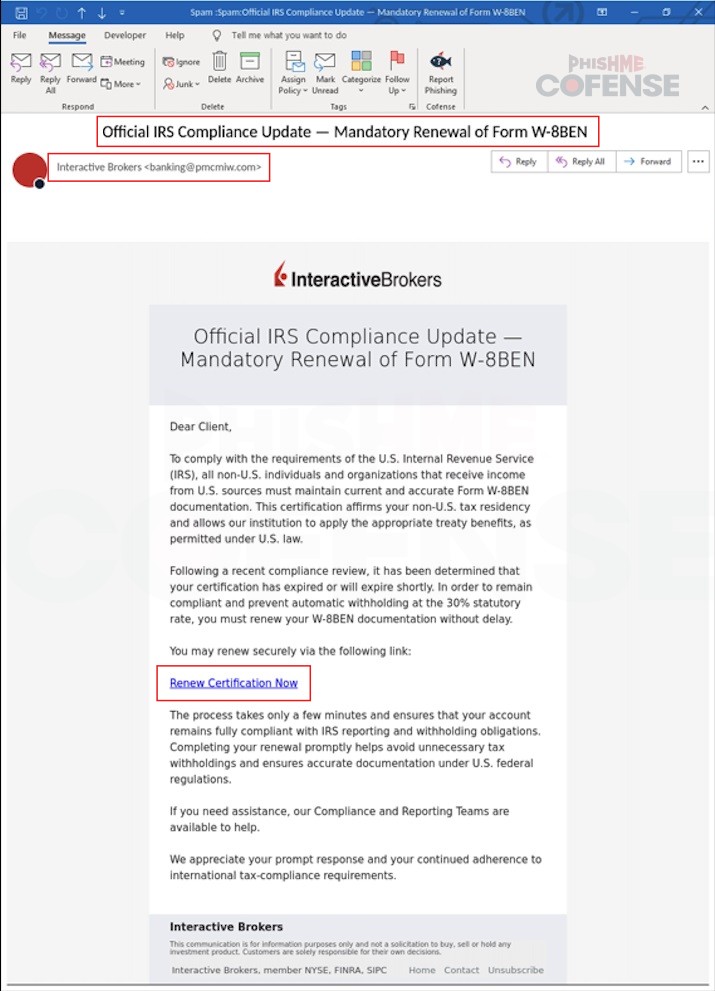
Figure 1: Email Body
This is the first indication that the email is suspicious. Checking the email content in Figure 1 explains the nature of the request, asking the receiver to renew their Form W-8BEN. The message also states the benefits of compliance, such as avoiding the automatic 30% withholding on US income and claiming tax treaty benefits.
This approach of using Form W-8BEN renewal can easily catch the receiver’s attention, as it leverages the actual requirements for using this platform. Included in the email body is a link with “Renew Certification Now”, prompting the receiver to click the URL to proceed.
Clicking the link opens a website that appears to be an Interactive Brokers login page, as shown in Figure 2. Checking the address bar reveals that it is indeed a different website <hXXps://wbnoebe[.]com/login>. If the recipient attempts to log in using their username and password, their credentials are sent over to the threat actor’s C2 server, <hXXps://wbnoebe[.]com?token
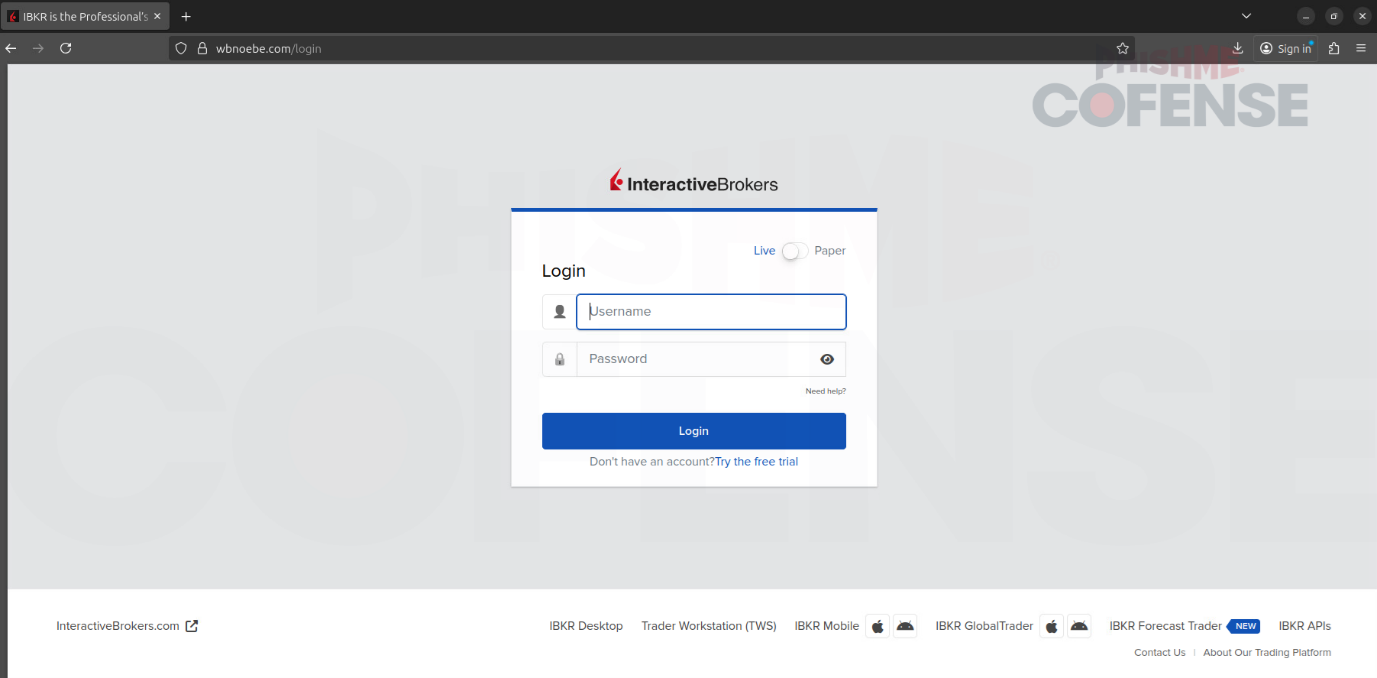.png?language=en)
Figure 2: Phishing Page
As online trading becomes more widespread, traders and investors are becoming increasingly attractive targets for threat actors. Not only for their login credentials, but also for their financial investments. This makes recognizing these threats a must to avoid potential losses. When receiving tax-related emails, users should always be alert, validate senders and URLs, and enable MFA as an additional layer of security.
Managed Phishing Detection and Response from Cofense can quickly identify and analyze threats that arrive in your inbox, giving customers a better defense against evolving email threats and malware campaigns like this. Schedule a demo with our team of experts today to learn more.
Email IOCs:
Stage 1 - Observed Email Infection URL: | Infection URL IP(s): |
hXXps://wbnoebe[.]com?token=eIqv7TknECn4EImFVxFD | 104.21.64.219 172.67.187.230 |