Author: Brad Haas
Conti is one of the most prolific ransomware operations in the threat landscape today. In a recent act of retaliation against Conti’s leaders for their support of Russia, an anonymous person leaked documentation and internal chat logs from the group. This blog post series covers important phishing-related takeaways Cofense Intelligence analysts discovered in the leaks. In Part 1, we discuss the background of the leaks, Conti’s segmentation of the attack chain, and how Conti operators use OSINT to select and harass their targets.
Background
A day after Russia began air strikes and ground invasion into Ukraine, Conti posted a statement of support for Russia on its public website. Although the group attempted to distance itself from the Russian government, the statement threatened retaliation if Western entities “attempt to target critical infrastructure in Russia or any Russian-speaking region of the world.” Two days later, an anonymous pro-Ukraine Twitter account published a large “leak” of Conti’s internal documentation, program code, and chat logs involving Conti operators and their associates. The leaked chats include Conti’s private Jabber and Rocket Chat instance, as well as chat logs from the TrickBot forums. They span most of Conti’s history, with logs from June to November 2020 and from January 2021 to March 2022. We examined the leaked information and identified several key takeaways for the phishing threat landscape.
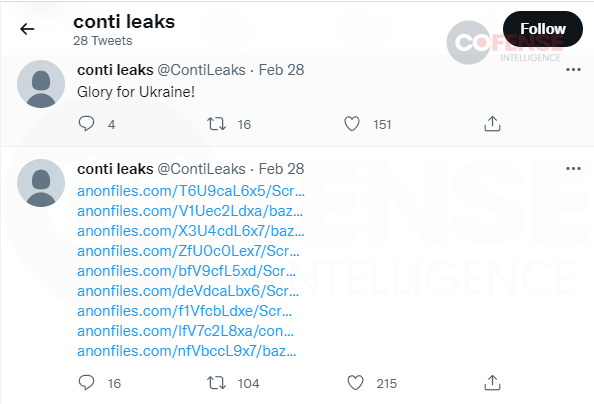
“ContiLeaks” tweets supporting Ukraine and posting a batch of leaked files.
Conti Intensely Favors Segmentation of the Attack Chain
In September 2021 we published a Strategic Analysis report to Cofense Intelligence customers, showing the significance of phishing and intermediate malware in ransomware attacks. Successful ransomware groups choose not to expend resources on scattered campaigns limited to encrypting only individual workstations that belong to individually compromised victims. Instead, they prefer to carefully select ransomware targets from organizations that have been compromised through phishing attacks against individual employees, or that can be compromised by other intrusion methods. They use any footholds in a network to perform reconnaissance and evaluate the viability and value of a target. If the effort seems to be worthwhile, they perform lateral movement to maximize the volume of data and systems they can ransom.
The Jabber chat leaks show that the Conti threat group fully embraced this approach. Reconnaissance experts associated with the group search for companies with indications of revenue exceeding a certain threshold and identify individual targets. For initial exploitation, they pay operators of other malware like TrickBot and Emotet to conduct phishing campaigns and establish footholds in the target organization. Conti managers distribute those footholds to a team of hackers who specialize in expanding access in remote networks and locating valuable data.
Beyond using specialists for each stage of attack, Conti’s leadership showed willingness to pay for sophisticated tools. They gave their reconnaissance staff access to business information services like ZoomInfo, SignalHire, and Crunchbase Pro. Their extensive work with TrickBot eventually led them to absorb its developers into their own team, and they influenced Emotet’s return to action after its 2021 takedown by law enforcement. For their intrusion team, they illicitly acquired access to Cobalt Strike licenses. The investments appear to have paid off: according to blockchain analysis group Chainalysis, Conti’s cryptocurrency revenue in 2021 alone was estimated at $180 million.
Conti Uses OSINT Research for Both Target Selection and Harassment
Conti’s OSINT researchers play an important role during multiple stages of an attack. Before infection, they help to identify target organizations (ones that are likely to be willing and able to pay large ransoms). Team members aggregate data from a variety of sources in order to present summaries, including company contact information, social media pages, industry, revenue, number of employees, and even website popularity ranking. For targeted organizations, they find contact information for potential phishing victims.
Once the ransomware has been successfully deployed and a victim organization has contacted Conti, the researchers identify influential figures associated with the company as targets for harassment. Conti’s negotiators reach out to these people to apply additional pressure to pay the ransom. In one case, a researcher listed two directors and two vice presidents within a victim organization, including multiple phone numbers for each one, and notes from the first time they had attempted to call. To create more pressure in instances where companies refuse to negotiate, the researchers go outside the organization and identify board members or investors as targets.
Stay tuned for Part 2, which covers Conti’s collaborations with other malware operators.
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats. Past performance is not indicative of future results.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.