By Kyle Duncan and Dylan Main, Cofense Phishing Defense Center
Tax season can be a stressful time for many people, and it comes as no surprise that every year threat actors look to capitalize on this by using a variety of new tactics to exploit their targets’ accounts and systems. Some of these campaigns can be rather simple and easy-to-spot phish while others may have detailed designs and more thought put into them. The Phishing Defense Center (PDC) has identified such a tactic that spoofs the U.S. Internal Revenue Service (IRS) to download malware onto user systems. This campaign leverages Netsupport Manager, a troubleshooting and screen control program, as a malicious remote access trojan (RAT) the threat actor employs to remotely enter user systems. The PDC has seen tax related campaigns in the past that have been used to steal employee credentials; however this attack is unique in that it is installing malware.
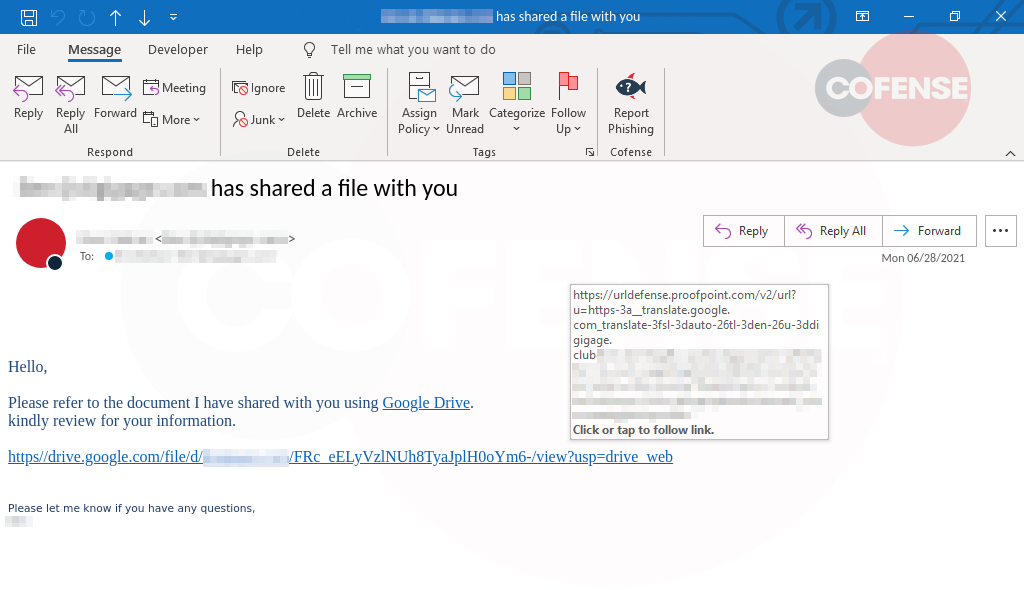
Figure 1: Email Body
In Figure1, the threat actor is attempting to impersonate an IRS audit request for a new federal law affecting U.S.-based companies. The email prompts users to click on the button to fill out “Form 4721” and update their company’s assets for tax purposes. While the IRS requires Form 4720 for certain excise taxes on charities, Form 4721 doesn’t actually exist. The email body appears to be designed well but the email address of the sender is hosted in Brazil and not likely to be used by the IRS for official communication. These are both indicators that were spotted by a well-conditioned user who quickly reported. Once a user interacts with the email, they are redirected to a captcha at hXXps://irsbusinessaudit[.]net/captcha.php.
Figure 2: Captcha Page
As seen in Figure 2, users are prompted to enter the three-digit code to access the form. When “continue” is clicked, an XLL file is downloaded. Unlike most Excel files, these files are used by companies to add functionality. In this case, the XLL file reaches out to a second directory found at the irsbusinessaudit[.]net domain and downloads a ZIP file named “DROP.zip.” Once downloaded, the contents of the ZIP file are not automatically initiated, requiring further interaction with the user.
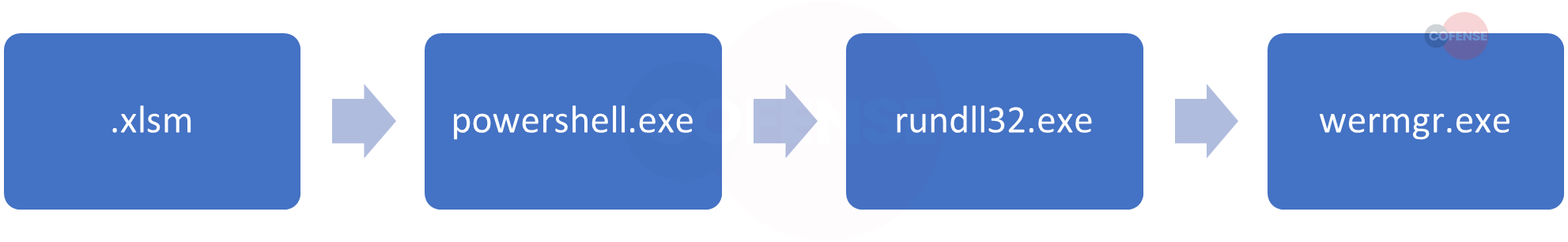
Figure 3: ZIP File
The contents of the ZIP file, seen in Figure 3, include all the necessary components to run Netsupport Manager. Netsupport Manager is an application typically used to give remote access to another machine. However, the main executable in the ZIP, client32[.]exe, was created just like any Netsupport binary and will check the location, via Netsupport Manager’s geolocation services, once initiated. However, a connection is then established with a threat actor-owned command-and-control (C2) server, instead of a legitimate IT service, which allows for remote access to the now-infected machine.
With tax season in full swing, sophisticated campaigns similar to this are dangerous to individuals as well as entire corporations. Remote access tools can be helpful, but, when used for nefarious crimes, they are extremely dangerous. Threat actors are always changing their tactics so malware can make it to the inbox of your users, even with a secure email gateway (SEG) installed and configured. Cofense products allow you quickly mitigate malicious emails that find their way to the inbox of users. With Cofense Managed Phishing Detection and Response, enterprises can have our full view of phishing attacks. Contact us to learn more.
| Indicators of Compromise | IP |
| hXXps://irsbusinessaudit[.]net/captcha.php | 185.225.19.116 |
| hXXps://irsbusinessaudit[.]net/DROP.ZIP | 185.225.19.116 |
| hXXp://45[.]76[.]172[.]113/fakeurl.htm | 45.76.172.113 |
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats. Past performance is not indicative of future results.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.