By: Andrew Remo
SEG Bypassed: Trend Micro, Microsoft The summer season is fast approaching, and with it come employee PTO requests. The Phishing Defence Center (PDC) recently observed a phishing campaign where the threat actor sent an email to a user that claimed to be from the ‘HR Department’ and provided the user with a link to submit their annual leave requests. This blog outlines the techniques used by the threat actor to both trick the user to provide their credentials and the techniques used to bypass security measures. As we can see in Figure 1, the user is informed that they must log in to their HR portal to verify their dates of annual leave. The sender is using a generic alias to impersonate Human Resources yet the domain from the email address is completely different to the company name, as well as a relevant subject ‘Annual Vacation Approval (Memo)’. These are common occurrences when a company-wide communication is sent to employees. The URL displayed in the email uses the company domain name and includes keywords such as ‘inter’, ‘staff’ and ‘folderaccounts’ in an attempt to appear as a legitimate business process. The email also refers to a list of names that follows a colouring scheme which indicates the ‘staff status’ of the employee. Outlining such information can prove to be effective as it can appear that the information provided in the link is ‘structured’, therefore, increasing the chances of being seen as legitimate by the user. Notice that the subject mentions the current year 2023, however the URL mentions ‘annual-open-vacation-ticket2022’, a clear indication that the email should be deemed suspicious. 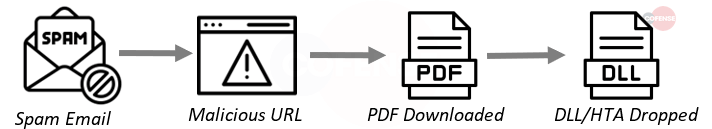
Figure 1
Once the user selects the URL from Figure 1, they will be directed to the login page as seen in Figure 2. The phishing page in Figure 2, simply asks the user to provide their username and password so they can submit their Annual Leave requests. Taking a closer look at the URL, it is clear that it is not the same URL provided in the email. The page is being hosted on the IPFS (InterPlanetary File System) network while simultaneously being translated by Google. IPFS, being a peer-to-peer file exchanging system, has become a common technique used by threat actors because once content is published on its network, it is likely to remain accessible and becomes difficult to remove. Here the phishing site is being accessed through a dedicated gateway from Infura. The PDC recently reported activity of this type. As seen in Figure 2, the Cofense home page appears as the backdrop for the login screen. The phishing page has been implemented to detect the domain from the user’s email address in the URL and to display the corresponding elements of that domain’s website, adding an element of trust. So in this case, our Cofense website was mimicked. 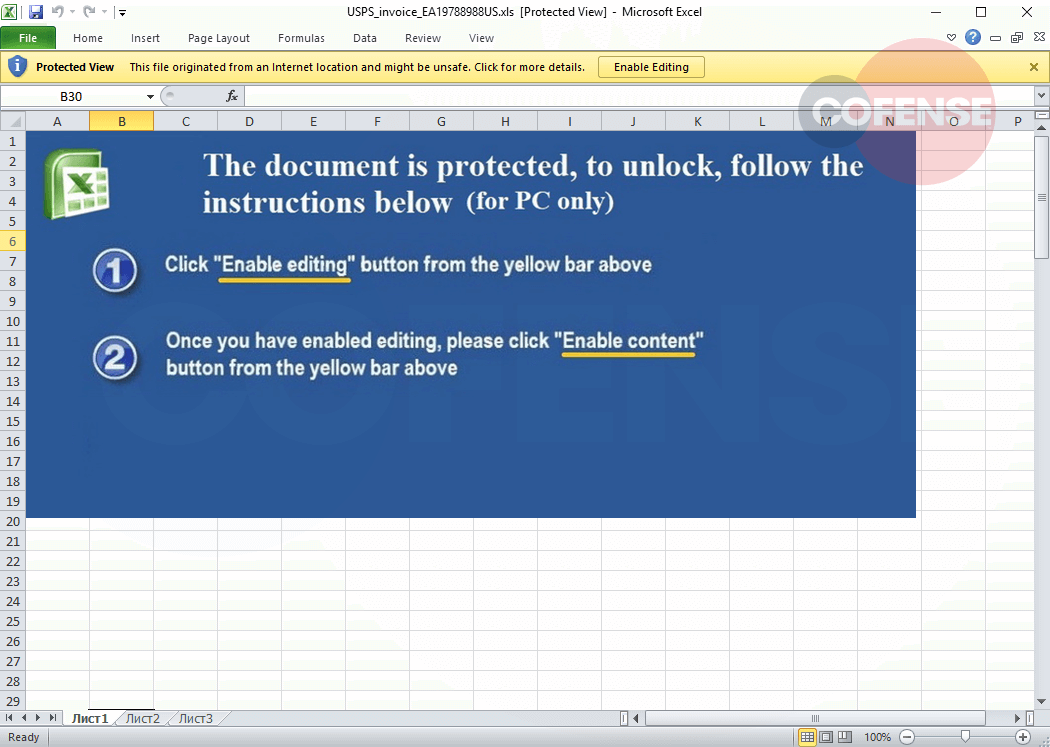
Figure 2
Once the user has entered and submitted their credentials to the form, it will fail on the first two attempts. This is a technique used by the threat actor to ensure the user is typing the password correctly or to use a different password in an attempt to gather multiple credentials. At the third attempt, the credentials will appear to have been processed successfully and the user is redirected to the company’s legitimate home page.
Conclusion
The PDC expects to see a potential increase in the coming weeks with phishing campaigns like this one. Due to the nature of these campaigns and their look of simplicity, the expectation is that this will be an effective threat vector against organizations, unless the appropriate phishing training is provided, and sufficient phishing
Indicators of Compromise:
| URLs |
|---|
| hXXps://prod-api[.]mailtag[.]io/link-events?mt__url=hXXps%3A%2F%2Fgeocities[.] ws%2F2067k%2Ff3002k300r820-382200h%2F123[.]shtml&mt__id= b5f5d386-9c3c-4383-9223-84813d047f98# |
| hXXps://20se-infura--ipfs-io[.]translate[.]goog/3cbab51d-6f44-4569-b131-140fd3802204/ajax?_x_tr_sl=auto&_x_tr_tl=en&_x_tr_hl=en-US&_x_tr_pto=wapp&u=hXXps%3A%2F%2Ffortonemold[.]com %2FM6%2FwebGRqZGpkbmF1d2llZDA5MzAzMDNtZG1kbWRtZA%2FwebGRqZGpkbmF1d2llZDA5MzAzMDNtZG1kbWRtZA [.]php%3Femail%3 |
| IPs |
|---|
| 34.211.43.45 |
| 52.35.199.214 |
| 172.253.122.132 |