Cofense Intelligence™ Strategic Analysis
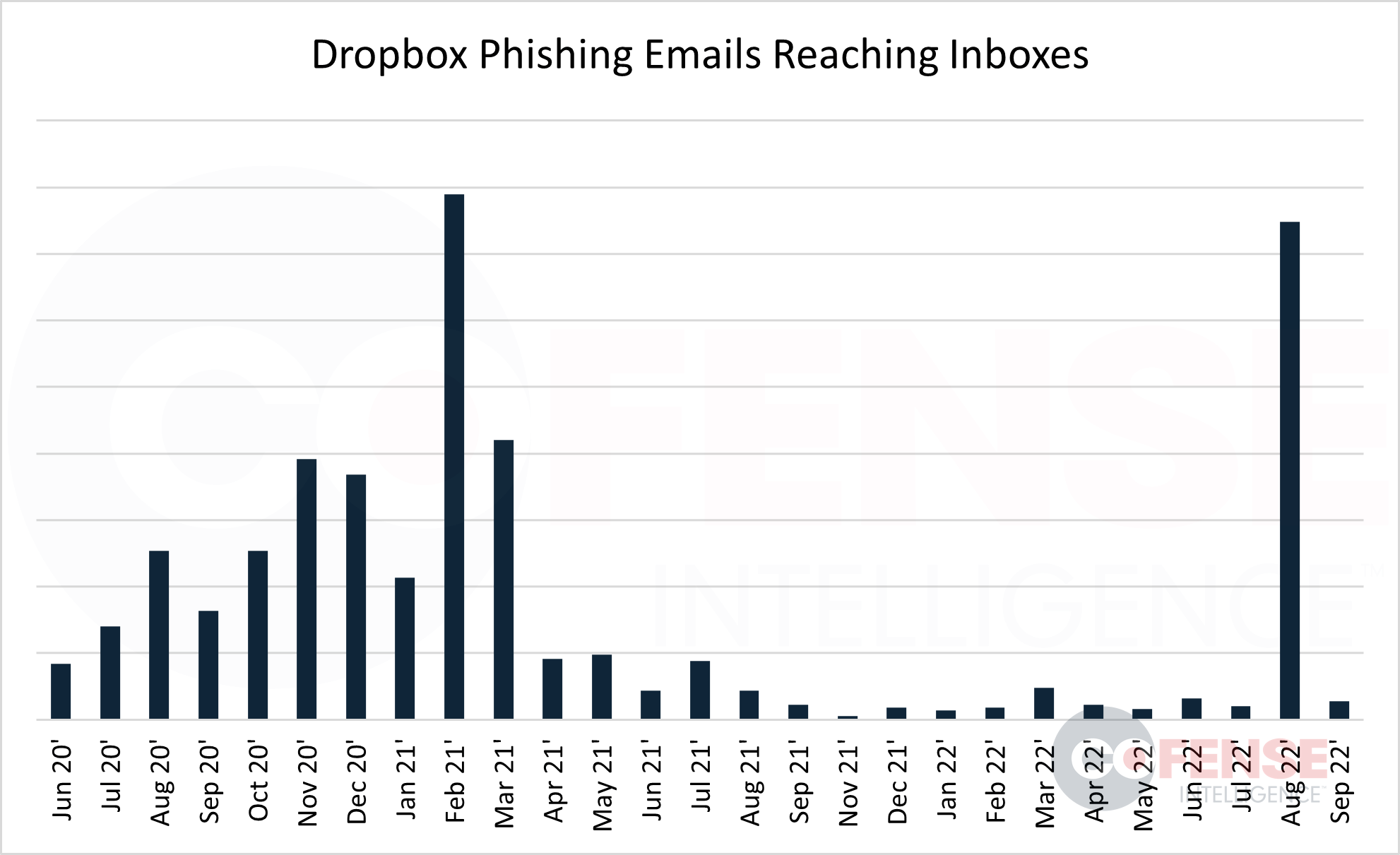
During August and September of 2022, Cofense observed an effective credential phishing campaign abusing Dropbox and reaching end users across many industries. The threat actor(s) behind the campaign have put in a considerable amount of effort in order to increase the chances of successfully stealing the email login credentials of enterprise users. By utilizing various tactics, techniques, and procedures (TTPs), the phishing emails have been very successful at reaching inboxes. These phishing emails reached inboxes in August at a volume far out scaling any other campaign that Cofense has seen effectively abuse Dropbox this year. However, the monthly volume from this phishing campaign has been inconsistent, dropping drastically from August to September.
Evasive TTPs
This campaign utilizes multiple TTPs known to increase the likelihood that the phishing emails reach the intended targets
- Trusted Domains – By abusing a well-known file hosting service like Dropbox, threat actors are able to host malicious content on a “trusted” domain. A domain is considered trusted when its primary use is legitimate. The use of these URLs can disrupt security measures that rely on automation since the domain cannot be blocked outright, and every URL must be analyzed individually. The use of Dropbox URLs can also create a sense of legitimacy for end users, making the phishing attempt all the more convincing.
- URL Redirection – The use of multi-layered links and redirection, multi-layered compression, and multi-layered encoding has become a common anti-analysis tactic. SEGs have the ability to follow redirections and do analysis on multi-step phishing campaigns, but there are usually limits set on the number of redirections a SEG will follow. This campaign combines the abuse of a trusted platform with multiple redirections. The embedded Dropbox link is not outright malicious, but it does start a redirection chain ending with a phishing page that harvests email login credentials.
- Blob URLs – Threat actors for this campaign have included an additional step within the URL redirection to create a Blob (Binary Large Object) for the phishing URL. A Blob URL allows Blob and file objects to be used as a URL source for data, images, etc. This step is not used for every email within the campaign, but when it is, it may be utilized as an anti-analyses and evasion technique. The first redirect starts the process of creating the Blob and uses JavaScript code to build it. This process is not likely to be noticed without tracking network traffic, meaning an everyday user is unlikely to notice. The key indicator that this process has occurred is that the phishing URL will have “blob:” in the address bar of the browser.
The combination of these tactics can disrupt security analysis and often results in phishing emails reaching the end user. Compromising employee credentials can lead to more high-level threats, potentially resulting in broader organizational compromise and financial loss.
Breakdown of the Phishing Campaign
This phishing campaign is well crafted and widespread, reaching enterprise users in many industries. The threat actors behind the phish have put in significant effort compared to ordinary phishing campaigns. The phishing emails tend to vary, as there seem to be multiple email templates used for this campaign. From an end-user point of view, some of the more convincing email themes being used are e-sign documents, fax notifications, project acknowledgments, and themes spoofing legitimate Dropbox emails. Figure 2 and Figure 3 below are both phishing emails from this campaign that were found in environments protected by SEGs. The first email (Figure 2) is convincing, appearing similar to a legitimate Dropbox shared file email. Employees that use Dropbox regularly may recognize this template and even feel safe interacting with it. Figure 3 is an example of an email spoofing Adobe Acrobat e-sign, suggesting that the recipient has financial documents that need to be signed. These are two of several email templates that have been seen within this campaign. At first glance, they appear to vary greatly. However, both contain Dropbox links that lead to a similarly hosted file which, when interacted with, will redirect to a credential phishing page. 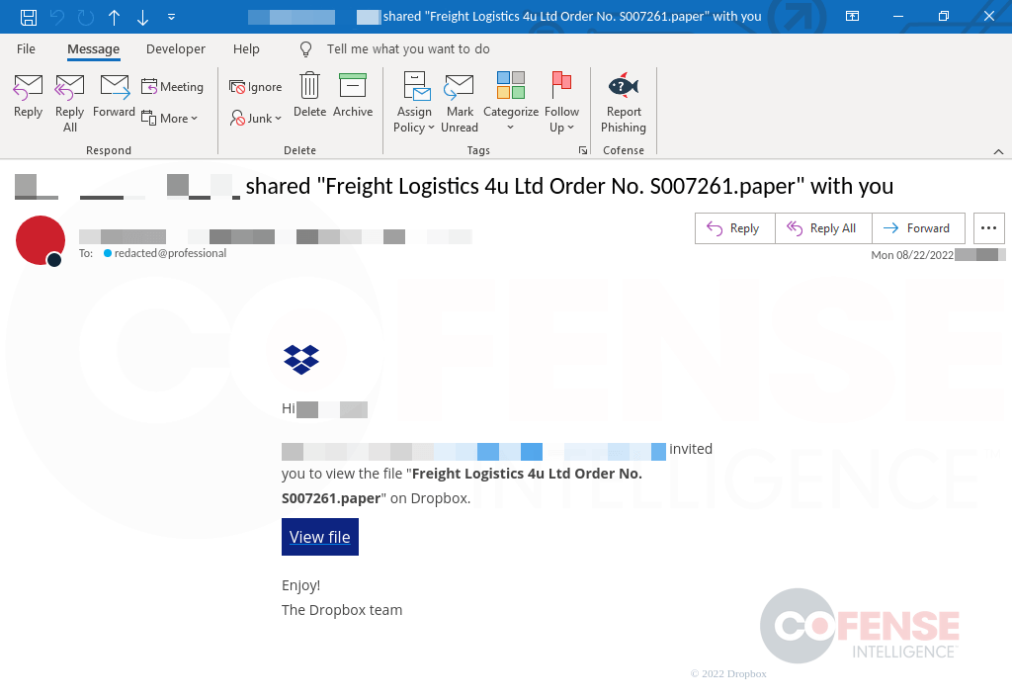
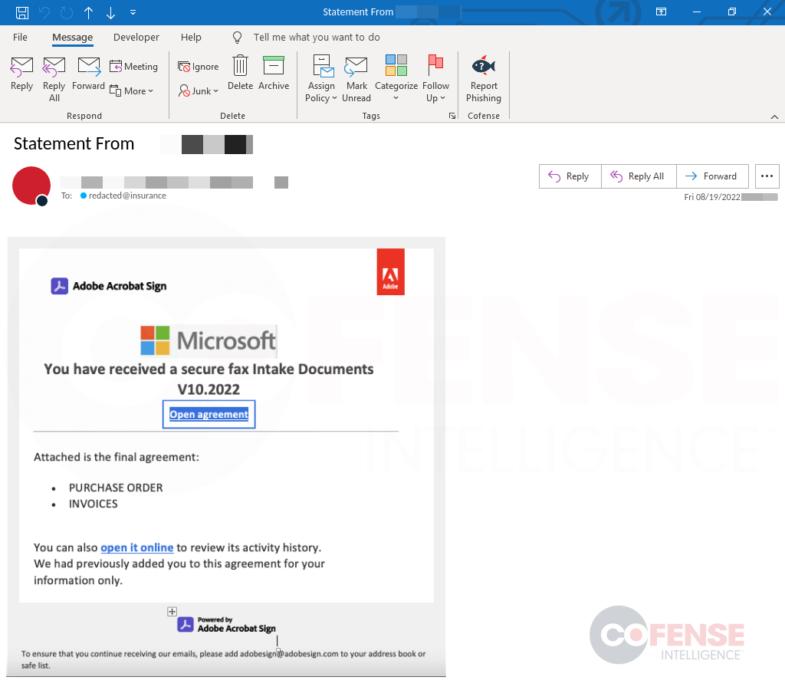
The threat actor’s use of such a wide variety of email templates can make it difficult to educate just on email appearance. While this is true, and education should be focused on the phishing tactics being used, it is important to understand the lure within the phishing emails. Table 1 shows some of the commonly seen subjects in this phishing campaign. The subjects almost always reference a shared file, which complements the threats actors use of Dropbox links. They also include some reference to the recipient’s name, employer, or other identifiable information to add a more legitimate appearance to the emails. Table 1: List of commonly seen email subjects in Dropbox phishing campaign.
| Commonly Seen Email Subjects in Dropbox Phishing Campaign |
| Shared Files with ‹recipient name or identifiable information› |
| DISITRUBUTED PROJECT FILES FROM ‹recipient name or identifiable information› |
| Distributions Acknowledgement from ‹recipient name or identifiable information› |
| Acknowledgement Project From ‹recipient name or identifiable information› |
| Acknowledgement For Project #55627 From ‹recipient name or identifiable information› |
| Acknowledgement Project For ‹recipient name or identifiable information› |
| Project Files From ‹recipient name or identifiable information› |
| Statement From ‹recipient name or identifiable information› |
| ‹recipient name or identifiable information› shared "‹filename›.paper" with you |
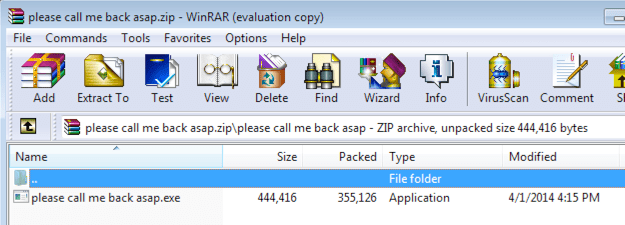
The embedded Dropbox links in these emails follow 1 of 2 Dropbox URL directory paths, /scl/fi/ and /l/scl/. These links can be created by manually uploading files to Dropbox and sharing the links, or by using the Dropbox API. The directory paths alone can't be used as indicators of compromise (IOC) because they are also found in legitimate Dropbox URLs. However, as commonalities in this campaign, they may be useful in separating it from other campaigns that abuse Dropbox. For instance, a standard PDF uploaded to Dropbox and shared will have a directory path of /s/, which is not used in this campaign. Below are two examples of full IOCs from this campaign: hxxps://www[.]dropbox[.]com/scl/fi/tz8lf0mlh36qk3imtvree/Your-mail-Password-is-set-to-expire-today[.]paper?dl=0&rlkey=6x59wvwcr6yggtbnz6eh2wmpe hxxps://www[.]dropbox[.]com/l/scl/AADV6XwJtJ583LJwbC9ucdLRsjs52-St6LI These links are often hidden in the email behind anchor text that follows the email theme, like “view file” or “see agreement”. Once a user interacts with the link, they will be brought to a file hosted on Dropbox like the one shown in Figure 5. This page in turn contains a clickable link that will start the redirection process, taking the user to a well-crafted credential phishing page like the one in Figure 6. These phishing sites are most often hosted on compromised domains and exfiltrate credentials to a PHP panel hosted on another compromised domain. 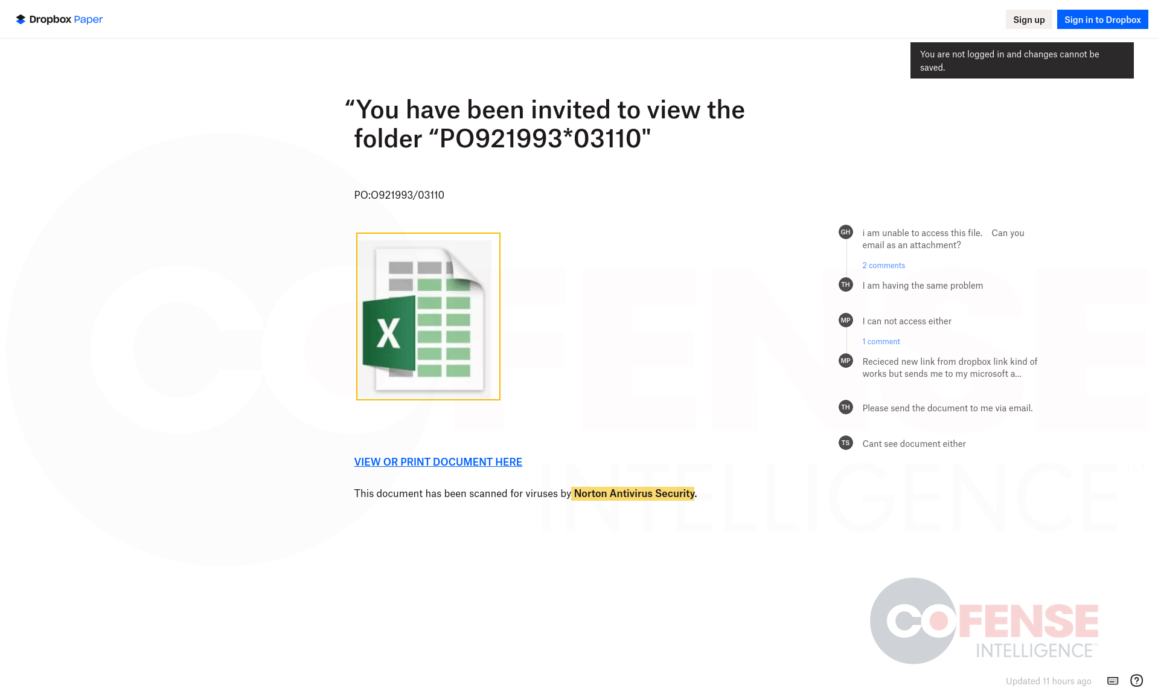 Figure 5: Dropbox site that redirects to phishing page.
Figure 5: Dropbox site that redirects to phishing page.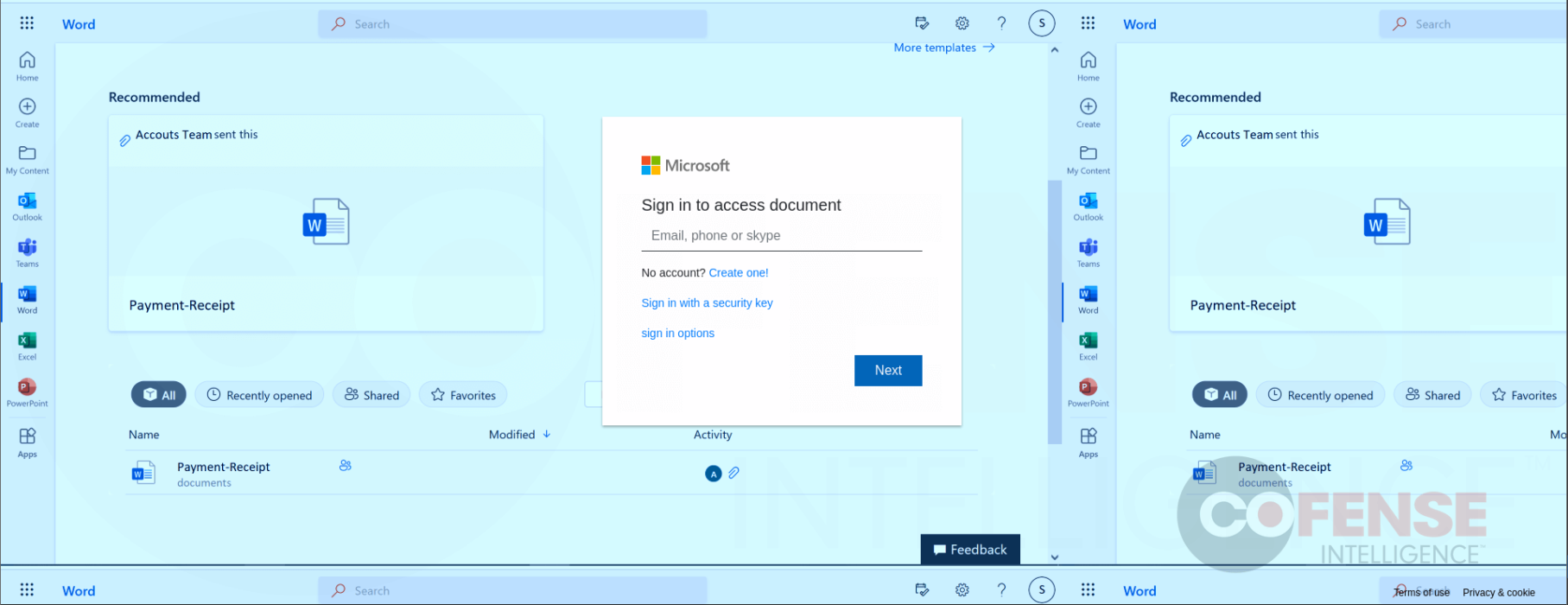 Figure 6: Phishing page used to harvest email login credentials.
Figure 6: Phishing page used to harvest email login credentials.