By: Madalynn Carr, Intelligence Team
In today’s world, there is an increasingly high focus on malware trends rather than repurposed legitimate tools. Repurposed or legitimate software is often overlooked, even though these have the capability to compromise devices, deliver and execute malicious payloads, and steal information from users. Legitimate websites being abused is very common and often mentioned in media. Yet, the actual programs and software are less often looked at due to the false assumption that there is little that can be done to avoid these. An example of a legitimate program that threat actors have repeatedly repurposed or abused is Microsoft products.
Microsoft products have had multiple vulnerabilities across the board which allow threat actors to use Remote Code Execution (RCE), which can then deliver malicious payloads. Remote Access Tools (RATs) are another prime example of this abuse, as there are legitimate RATs typically used by companies that are leveraged by threat actors. These are different from Remote Access Trojans which also use the acronym RAT. Remote Access Trojans pretend to be software that they are not, hence the Trojan part of the name.
This report will look over the span between December 2021 and December 2024 and will cover the wide array of weaknesses in legitimate or abused tools, including exploits such as CVEs, that Cofense has seen in this timeline.
Main Takeaways:
- Legitimate Software is being leveraged by threat actors to bypass EDR detection.
- The most common legitimate software being abused to deliver different malware are Microsoft Office products, primarily through CVEs and Office macros.
- However, Office macros have become very uncommon, as Microsoft came out with an update to automatically disable macros.
- Remote Access Tools have multiple capabilities which has been mentioned in previous reports, and have become more popular since.
- The most popular Remote Access Tools are ConnectWise RAT and NetSupport Manager RAT, being 75% of all Remote Access Tools.
- Many Remote Access Tools offer either free demos or charge very little for their service, making it feasible for threat actors.
Delivery Mechanisms
Much of the malware seen in Secure Gateway Environments (SEGs) is delivered via a delivery mechanism. Some of these delivery mechanisms abuse legitimate services to deliver malware. Some examples include CVEs and Office macros.
CVEs
A prime example which covers a wide variety of this abuse, although infrequently used in recent history, is Common Vulnerabilities and Exposures (CVEs). These CVEs should be patched shortly after they are exposed to the public, however, threat actors take advantage of companies that are still vulnerable.
Popular examples of CVEs include EternalBlue (CVE-2017-0144) and Log4j (CVE-2021-44228). One example that was seen frequently in the past is CVE-2017-11882, which takes advantage of the Equation Editor in Microsoft Office applications. This is also often paired with CVE-2017-0199, which is another vulnerability that allows threat actors to leverage RCE within the Windows API. An example of an email delivering these CVEs can be seen in Figure 1.
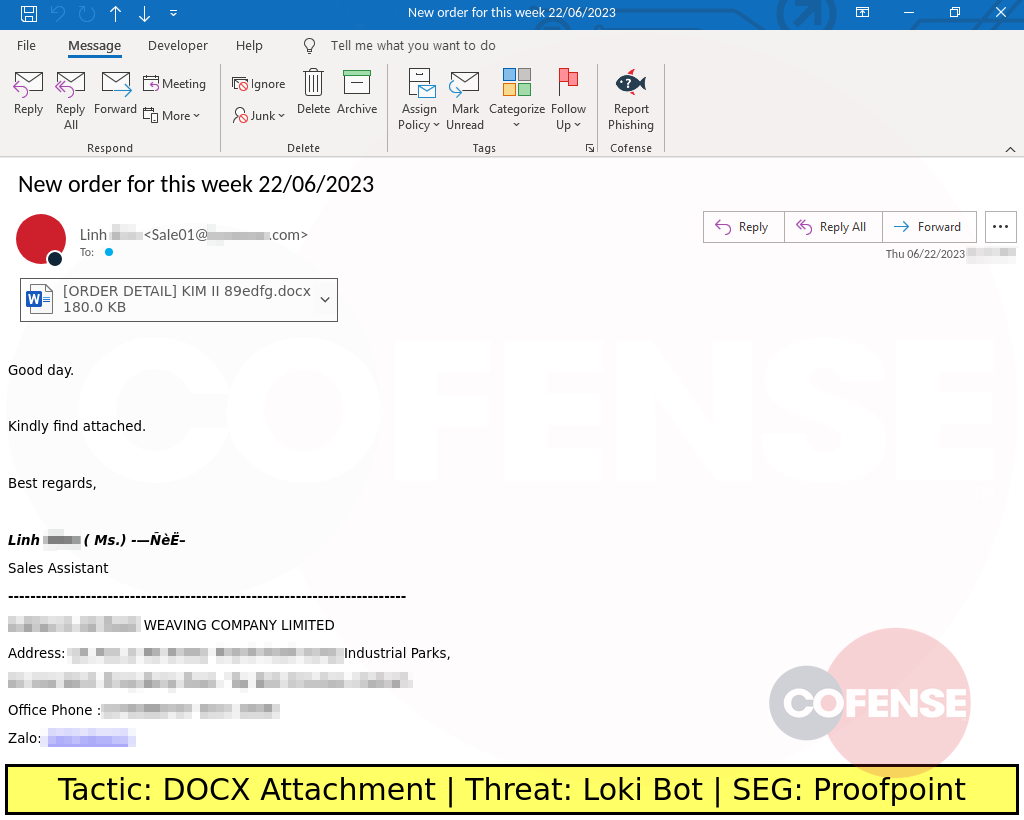
Figure 1: Email delivering malware via an Office Document containing CVE-2017-0199 and CVE-2017-11882.
A few other examples of CVEs that were prominent during the 3-year time range includes CVE-2018-0798 and CVE-2018-0806, both of which also take advantage of Microsoft programs, specifically the Equation Editor in Microsoft Office applications. These 4 CVEs all leverage RCE and take advantage of users by delivering a unique file with the payload embedded in the file.
Office Macros
Another delivery mechanism that was once often used is Microsoft Office macros. Although macros are not a common delivery mechanism anymore, threat actors took advantage of the remote code execution capability. Macros have been often used for legitimate purposes in multiple companies to increase productivity, however threat actors had taken advantage of these being automatically enabled in many company environments.
Even if companies did not use macros, Microsoft originally had this ability automatically enabled for any environment with Microsoft Office products. Microsoft did take action against this, and in June 2022, Microsoft started to release updates to Office products, defaulting macros to be disabled. This has mitigated many infections and has caused Office macros to be less frequently used to deliver malicious content.
Malware
The primary malware type which is compromised and abused by threat actors is Remote Access Tools (RATs). RATs have a wide variety of capabilities that can be used maliciously if a threat actor is in control. RATs generally can capture keystrokes, screenshot the desktop at any time, access webcam video and audio, and access all files.
RATs can also connect to the desktop manually at any point through multiple methods, which can further escalate into lateral movement by downloading additional malware. For more information about what RATs are capable of, Cofense has written a Strategic Analysis explaining it in further detail.
The RATs Cofense has seen most often in the last 3 years have been NetSupport Manager, ConnectWise, FleetDeck, and Atera. However, this list does not contain every legitimate RAT seen, as countless other RATs are abused or compromised to make up the last 13% of the graph in Figure 2.
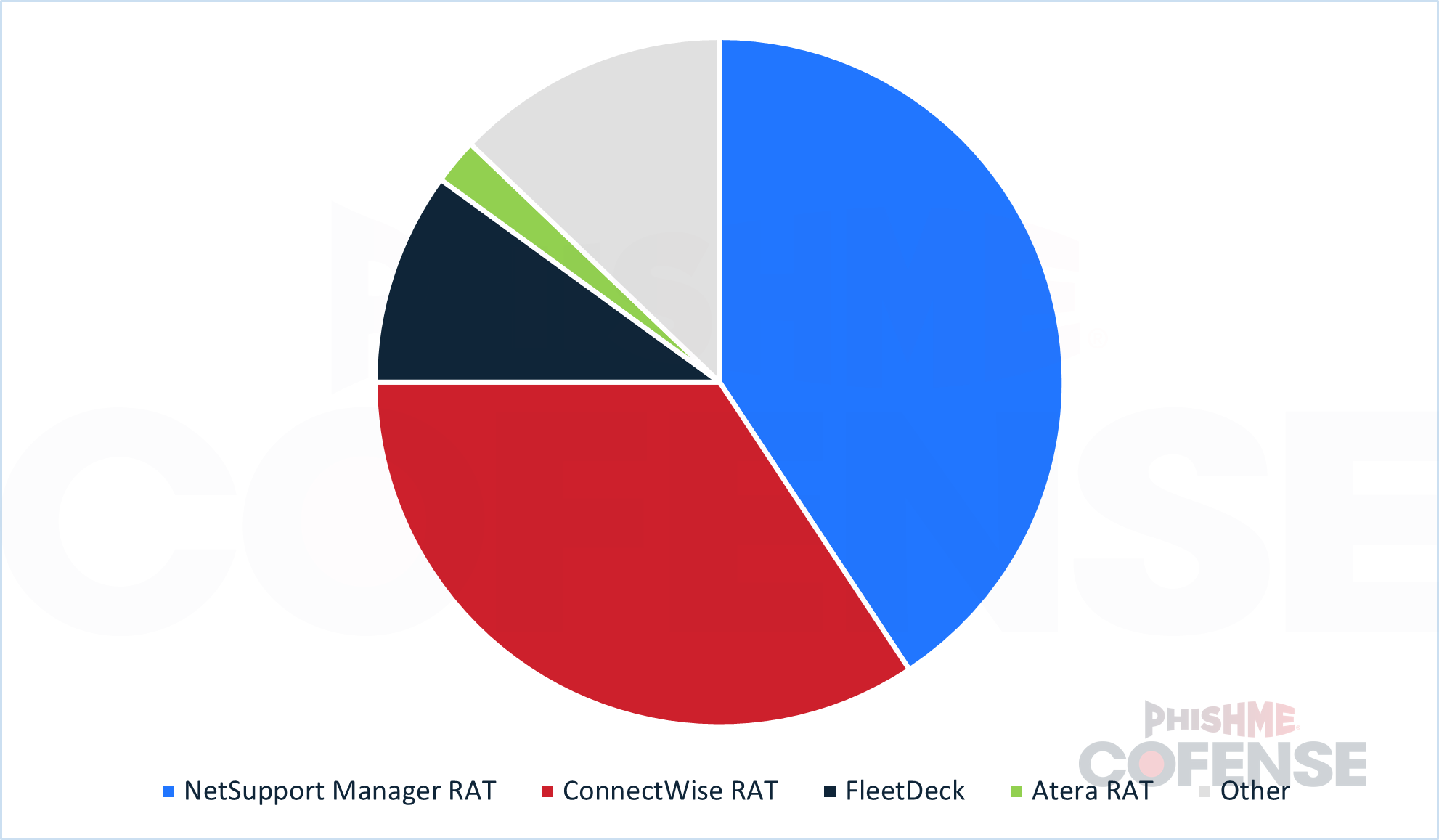
Figure 2: Pie chart showing the most common Remote Access Tools seen at Cofense from December 2021 to December 2024.
NetSupport Manager RAT
At the time of this report, the most common legitimate RAT is NetSupport Manager, making up over 40% of legitimate RATs seen in Figure 1. NetSupport has been a legitimate Remote Access Tool for over 30 years, which allowed this tool to gain a positive reputation towards the public. According to NetSupport Manager’s website, the average cost per device is only $15(USD), which allows threat actors to put little effort into their malware with little cost. There is also a free trial period that threat actors can take advantage of, lowering the cost even more. Cofense first saw high volumes of NetSupport Manager in the wild in 2022, but there are sightings of this RAT being used maliciously in 2016. There has been an article written by Cofense related to NetSupport Manager RAT at the time of this report.
ConnectWise RAT
Cofense has noticed ConnectWise RAT gaining an immense amount of traction towards the end of 2024, enough to take up 34% of all legitimate RATs in Figure 1. ConnectWise is an IT Management Software tool, and the company also offers other MSP tools. The main focus is the ScreenConnect tool that ConnectWise offers, ranging from $28(USD) to $53(USD) per month for a wide array of computers.
Before ConnectWise was widely known, this legitimate tool was referred to as Parcel RAT in 2020, however, there are articles referring to ConnectWise RAT by its newer name as early as 2022. ConnectWise was first seen by Cofense in significant numbers in March 2024, and this RAT has been prevalent in the landscape ever since at the time of this report. Cofense has released ConnectWise RAT Flash Alerts and Strategic Analyses in the past, as well as being mentioned in even more articles written by Cofense due to the extreme frequency of the tool being used in the wild.
FleetDeck
Another RAT that is a bit newer on the threat landscape is FleetDeck, which is a relatively newer legitimate RAT seen in the wild and is 10% of all legitimate RATs in Figure 1. FleetDeck is another RAT that was originally intended to help aid MSPs and IT management, however, threat actors have also taken advantage of this. One potential reason for this influx in FleetDeck is due to the low price of $5(USD) a month, which also includes a free trial. This allows threat actors to pay little to none while compromising computers. Cofense first noticed this tool being leveraged at scale in July 2024 and at the time of this report, FleetDeck has still been maintaining prominence in the threat landscape.
Atera
Atera is another RAT that is often paired with other Remote Access Tools, such as Splashtop, TeamViewer, AnyDesk, and ScreenConnect. Likely due to this, Atera only takes up 2% of the entire graph in Figure 1 compared to the other common legitimate RATs. Atera for legitimate purposes can alert the owner of a device’s health, can send information relating to the device to a cloud, and allows commands to be executed remotely on the device.
This RAT’s unique offer to threat actors is that it can work on Windows, Mac, or Linux operating systems, allowing for a more diverse set of users to gather information. Atera also offers a free trial with a flat fee afterward as promoted on their website, which allows threat actors to get away with using this tool without needing to spend money. Atera Agent RAT was released in 2016 and has been used by multiple companies.
However, in 2022 this RAT began to be abused by threat actors in large numbers. Atera was first seen by Cofense in significant volumes in October 2024 and has continued to stay at the time of this report. Although not as popular as the previous ones mentioned, this Remote Access Tool is extremely new to the threat landscape, allowing it to bypass simple EDR and other security measures. On top of this, many companies use Atera Agent and do not want this tool to be flagged as malicious, causing conflict between consumers and EDR/Antivirus companies.
As threat actors continue to exploit trusted tools and overlooked vulnerabilities, organizations must rethink how they detect and defend against these subtle yet highly effective attack methods. Strengthening visibility into legitimate software abuse and prioritizing timely patching are critical steps in closing these gaps. To see how Cofense can help your organization identify and stop these threats before they escalate, request a demo today and experience a more proactive approach to email and human-driven security.