By Harsh Patel, Cofense Phishing Defense Center
War in the modern era extends far beyond the physical battlefield. The ongoing conflict in the Middle East involving the United States, Israel, and Iran continues to generate widespread fear and uncertainty, particularly among civilians in affected and neighboring regions. This climate of heightened anxiety creates ideal conditions for cyber threats, as malicious actors exploit fear-driven narratives to target individuals through digital attacks such as phishing and disinformation campaigns.
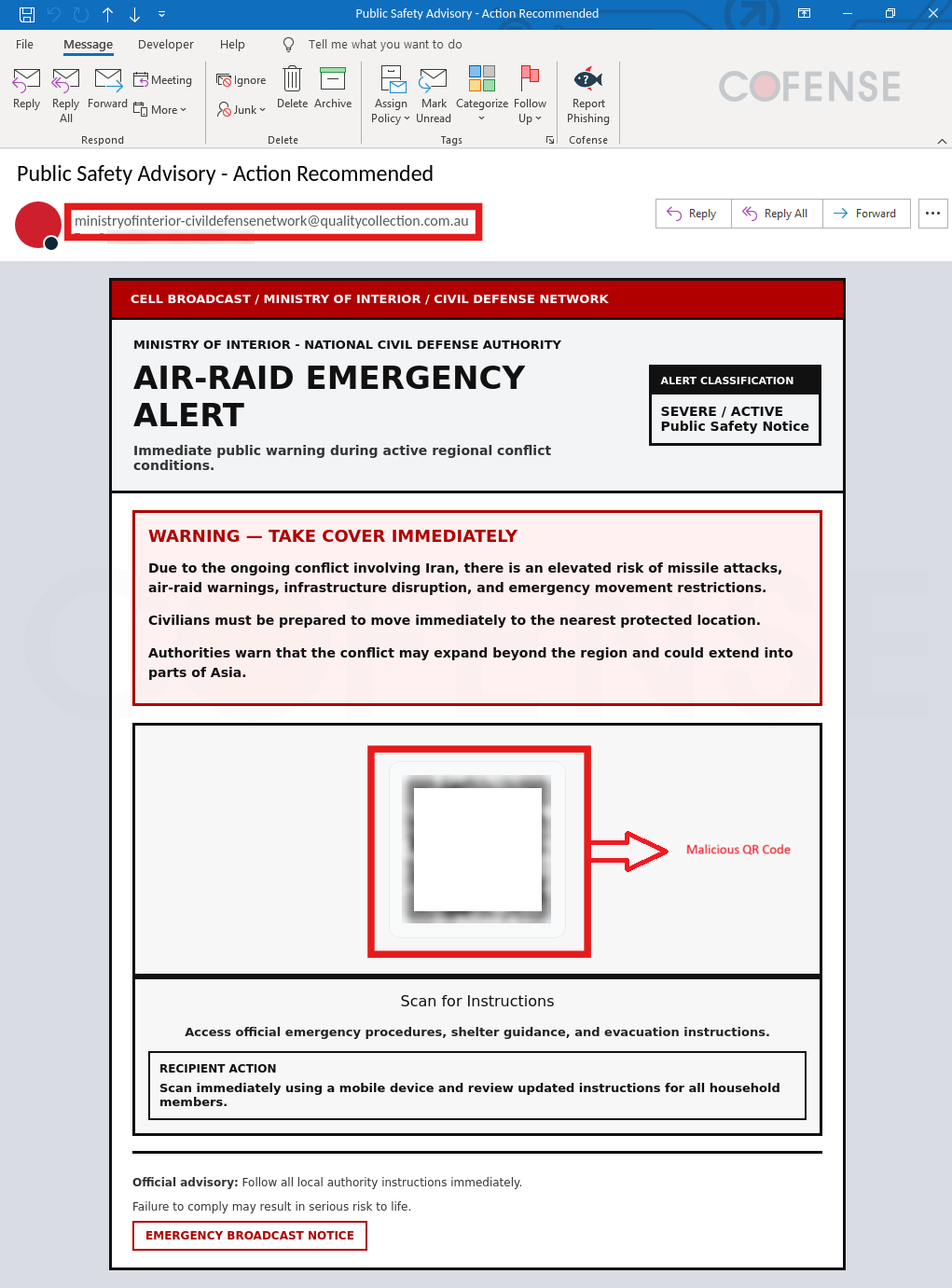
The Cofense Phishing Defense Center (PDC) has recently identified a phishing campaign that impersonates a government emergency alert, referencing entities such as the Ministry of Interior and Civil Defense. The message presents itself as a high-level emergency alert labeled “SEVERE / ACTIVE,” warning of imminent threats tied to an alleged regional conflict involving Iran. Recipients are urged to scan a QR code for “official” instructions, but the code instead leads to a Microsoft-themed phishing page designed to capture sensitive information.
.png?language=en)
Figure 1: Email Body
Analyzing the email in Figure 1, the subject line “Public Safety Advisory – Action Recommended” appears to originate from the domain “ministryofinterior-civildefensenetwork@qualitycollection[.]com[.]au.” The email uses urgency and fear-driven language, telling the recipients to “take cover immediately” and prepare for missile attacks or emergency evacuations. It also directs the user to scan the QR code for instructions for “official emergency procedures, shelter guidance, and evacuation instructions.” This is a classic example of social engineering, leveraging panic and authority to trick users into acting quickly without verification. The repeated phrasing, lack of personalization, and reliance on a QR code instead of a verified source all indicate a mass phishing attempt designed to exploit situations of panic and prompt impulsive actions.
Figure 2-3: Human Check Page
Once the QR code is scanned, the user is directed to a website that presents a “human verification” check, mimicking a standard security measure, as shown in Figure 2-3. The page prompts the user to click on a simple checkbox to confirm they are not a bot, after which the verification appears to be completed successfully. This step is designed to build trust and create a false sense of legitimacy, making the site seem safe and routine. It serves as a gateway to the next stage of the phishing attack, lowering the user’s suspicion before they are prompted to provide sensitive information.
Figure 4: Microsoft Phishing Page
After being redirected, the user is taken to a Microsoft-themed phishing page designed to capture sensitive information, as shown in Figure 4. The page closely mimics the familiar Microsoft sign-in portal, appearing highly convincing and trustworthy, and is intended to harvest any credentials entered by the user.
This attack demonstrates how threat actors continue to evolve their tactics by combining current global events with impersonation of authoritative sources and emergency alerts to exploit a wide audience. By leveraging a familiar Microsoft sign-in page, attackers further increase the likelihood of credential compromise. This serves as an important reminder that even in highly urgent situations, messages like these should be approached with caution, especially when they demand immediate action or rely on unconventional methods such as QR codes.
Threats like this demonstrate how easily sophisticated phishing attacks can bypass traditional defenses and exploit human trust. With Cofense Managed Phishing Remediation and the Cofense Phishing Defense Center (PDC), organizations gain access to expert analysts who rapidly identify, investigate, and neutralize phishing threats before they can cause harm. By combining human intelligence with advanced automation, Cofense helps security teams respond faster and stay ahead of evolving attacks. Schedule a demo today to learn more about how Cofense can strengthen your phishing defense strategy.
Email(s) IOCs:
Stage 1 - Observed Email Infection URL: | Infection URL IP(s): |
hXXps://ministry[.]sharedfilescorps[.]com/interior/$ | 104[.]21[.]91[.]60 172[.]67[.]167[.]123 |
Stage 2 – Observed Payload URL(s): | Payload IP(s): |
hXXps://global[.]sharedfilescorps[.]com/interior/ | 104[.]21[.]91[.]60 |
hXXps://wivoumea[.]ru/HAPApOYtrk1Zzs0iF6mk@/$ | 104[.]128[.]128[.]129 |
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats. Past performance is not indicative of future results.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.