By Kaleb Kirk, Cofense Phishing Defense Center
The importance of having contactless, digital conferencing software (such as Zoom or Microsoft Teams) is well understood by many companies worldwide. COVID-19 has completely changed the way people work, and the Phishing Defense Center (PDC) has been endeavoring to make people more aware of threats that target these key platforms. Though similar subjects have been covered by other PDC blogs, this is another example of how attackers are constantly updating their strategies and tools.
The attack of interest here involves a Zoom branded phishing page that attempts to trick the user into believing it is an internal email. The PDC has seen similar modes of attack involving different brands but Zoom and Microsoft Teams have been the most prevalent.
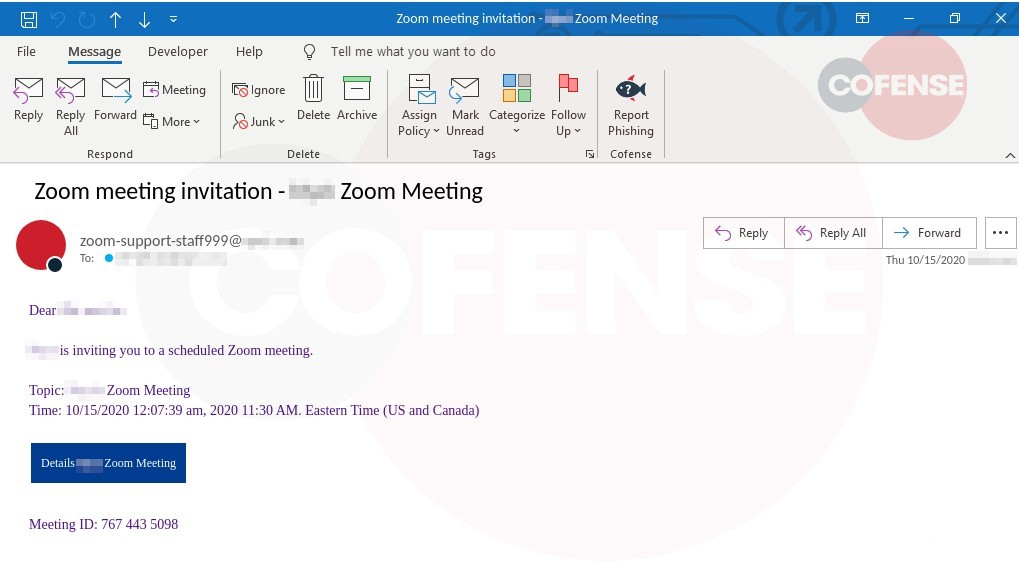
Figure 1: Email Body
For this attack the threat actor has utilized the theme of a Zoom invitation, again because of its increased use with remote workers during the pandemic. The subject is “Zoom meeting invitation – Zoom Meeting,” mentioning the user’s company name to establish that this is not an invitation to some random Zoom meeting but rather one that’s relevant. The threat actor has made sure to spoof the sender email to make it appear as though it’s coming from an internal address. The first part of the email shows as “zoom-support-staff999″ and the domain it’s supposedly coming from appears as the user’s company domain. Although a user may not know much about the sender address, it relates to the topic of Zoom and is coming from what appears to be their company. This makes the invitation appear company–approved and safe.
The email addresses the user by their first and last name, states that their company is inviting them to a meeting, complete with specific time and date details, as well as a fake meeting ID, all of which promote a sense of legitimacy.
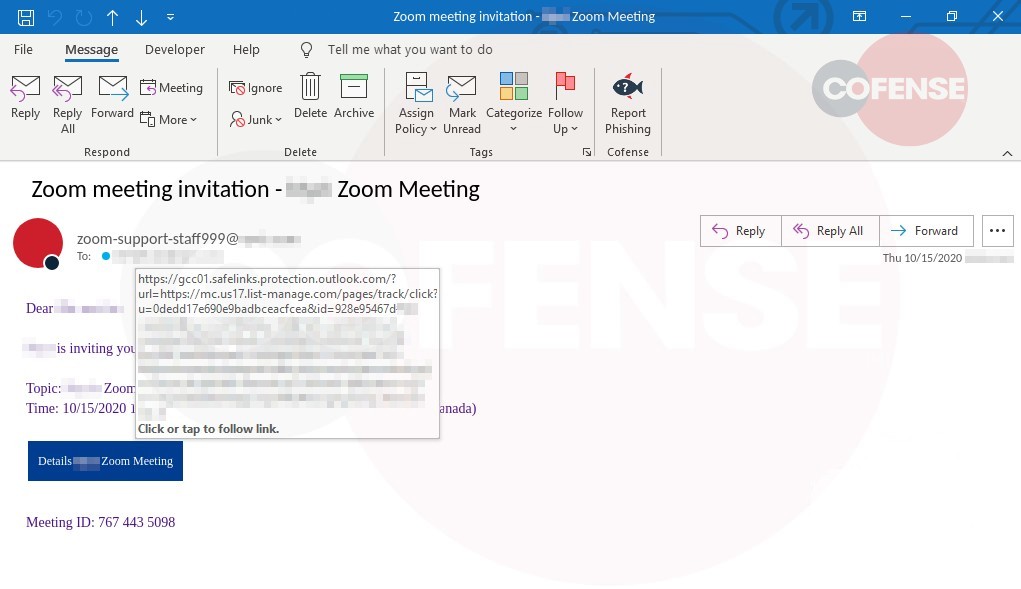
Had all of that been enough to draw in the recipient, and they seek to learn more about the “meeting,” the next step for most would be to click “Details Zoom Meeting.” The malicious URL is a redirector link, specifically list-manage[.]com, a MailChimp domain that is commonly used with newsletter/marketing emails sent through MailChimp by their own clients. The use of redirector links similar to the one used here is not unheard of and represents a trend seen often with phishing attacks. Regardless, these links are useful in that they hide a much more obvious malicious URL behind a cleaner, seemingly more legitimate, one.
Once the user clicks on the link about the supposed meeting, they will be redirected to the page seen in Figure 2.
Figure 2: Phishing Page
The page is meant to make the recipient believe this is a standard Microsoft login page to authenticate the user before they can see more regarding the meeting. The user’s corporate email address is prepopulated in the login field. However, upon closer inspection of the address bar, it can be seen that this is not the official Microsoft site. Multiple directories showcase the threat actor’s compromise of that domain to place malicious pages.
| Indicators of Compromise | IP |
| hXXps://mc[.]us17[.]list-manage[.]com/pages/track/click?u=0dedd17e690e9badbceacfcea&id=928e95467d | 1041022154 |
| hXXps://prescot[.]x-web[.]sk/ | 2131863317 |
| hXXps://test[.]lerocherparfaby[.]fr/wp-includes/pomo/owa/login/Login.php | 37917521 |
Threat actors are adept at quickly and cleverly modifying tactics to get around technical controls, as can be seen from the above examples. Software-only security systems can’t outsmart innovative and human-designed phishing attacks. Cofense combines the human input of 26 million people globally with state-of-the-art technology to help organizations find and remove phishing attacks in minutes instead of hours or days.
Learn more about our industry leading phishing detection and response solutions delivered as a suite of integrated products or as a managed service delivered through our five global phishing defense centers.