By Schyler Gallant, Alex Geoghagan, Cobi Aloia, Cofense Phishing Defense Center
The Cofense Phishing Defense Center (PDC) employs expert Threat Analysts to analyze emails on behalf of enterprise customers across the globe, in various industries, who are dealing daily with phishing attacks delivering malware. To help keep up with evolving tactics and top ongoing threats affecting real customers, the PDC has created a breakdown of the top five malware families we have seen across the Managed Phishing Detection and Response (MPDR) customer base over the past thirty days. If you have any interest in learning more about how your organization can be protected by our expert Cofense Threat Analysts, please contact us for additional information.
Top Malware Families in May:
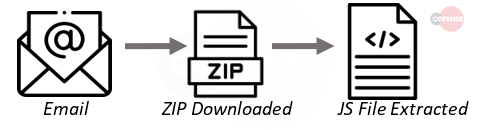
1. Qakbot – QakBot is a banking trojan with worm like features for self-propagation. It is a modular malware that is capable of information stealing, securing a backdoor, self-propagation, and anti-research / anti-virus evasion. This malware also has a sophisticated persistence ability, including frequently changing the file and recompiling the entire binary to evade detection.
- Subject: Emails delivering Qakbot re-used past email communications and so the subjects are varied greatly, however, most are replies or forwards.
- Attachment: Qakbot is delivered using a URL instead of an attachment.
- Behavior: Javascript contained within zip folder will nest in Wermgr.exe once it is acted upon.
- Brand: Re: // FWD // Replies
- Infection Chain:
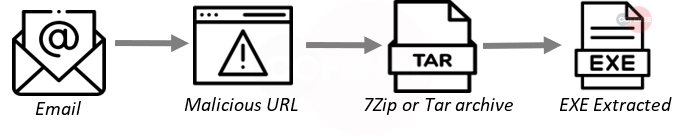
2. Agent Tesla – Agent Tesla is a stealer written in .NET. It is not only a keylogger, but is also a sophisticated stealer, capable of decoding and exfiltrating data from various applications, such as: Chrome, Firefox FileZilla, Steam; and many more. In addition to sophisticated monitoring capabilities – including on-screen keyboard hooking and screenshotting – Agent Tesla can use multiple exfiltration avenues to hand-off stolen data to its designated C2. SMTP, HTTP and WebPanels are all avenues available to Agent Tesla.
- Subject: Subjects delivering Tesla this month were made to look like either purchase orders or requests for quotations.
- Attachment: Tesla is delivered using an infection URL instead of an attached file.
- Behavior: Archive (either 7z, .tar or .tgz most commonly) contains an exe that when ran will nest in processes and use Telegram/tor server connections for C2.
- Brand: PO // Purchase Inquiry // RFQ
- Infection Chain:
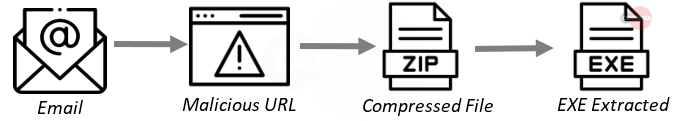
3. Remcos – Remcos was originally a remote desktop connection tool that has since been repurposed as a remote access trojan capable of taking control of a user’s system. Its chief capabilities include key logging, information stealing, and audio/visual monitoring.
- Subject: Subjects were made to appear as though the emails were from Legal/judicial authorities or were made to look like electronic invoices. Emails are predominantly in Spanish.
- Attachment: Remcos is delivered using a URL instead of using an attached file.
- Behavior: The compressed file contains a malicious executable made to look like a legitimate program. Once clicked, it will run in the background like your typical RAT and wait for orders.
- Brand: Factura // Mexico // Legal
- Infection Chain:
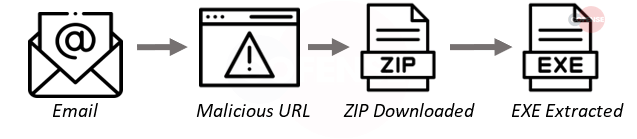
4. Grandoreiro – The Grandoreiro Banking Trojan malware is malware written in Delphi which is used by the threat actors to target Latin American victims. Using an intentionally inflated file size which can help avoid detection, various application and online banking credentials are targeted.
- Subject: There was some variety in the subjects of emails delivering Grandoreiro, however, the major theme was towards fake invoices.
- Attachment: Grandoreiro is delivered using an infection URL not an attachment.
Behavior: Unlike previous deliveries, the executable is directly located within the zip rather than being inside of an MSI file. Once activated this .exe will sit in processes and compromise information (commonly banking information) - Brand: Factura // Azure // South America
- Infection Chain:
5. Lokibot – This trojan targets South American users and will download its payload using various methods. The current campaign has a focus on Spain and will download a ZIP file. After running, the downloaded ZIP file will contain a JS, DLL, and an AHK file. The JS will use AutoHotKey (AHK) to run the DLL which is the main Mekotio payload. A new varialoadsf Mekotio is utilizing a DLL side-loading technique where DLLs related to legitimate applications are ran, which then load in Mekotio.
- Subject: Subjects were crafted to appear as though they were invoices. Emails were mostly delivered in Portuguese.
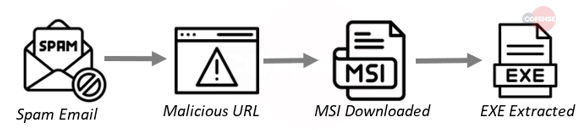
Attachment: Delivery is accomplished using an infection URL instead of an attachment. - Behavior: ZIP delivered holds an MSI file which itself contains the EXE and supporting files. Commonly makes use of AHK files/scripts in this process.
- Brand: Invoice // Brazil // Nota Fiscal
- Infection Chain:
Summary:
The month of May has seen a continued increase in the QakBot campaign that we have been following for months. This QakBot campaign has also been accompanied by a curious campaign of “TrueBot” or “Pikabot” which has only just begun in the closing weeks of the month and closely mirrors what we have seen from QakBot in the past. It is also worth noting that all of the top 5 families for the month have been delivered using infection URLs and NOT using an attached file. It is more important than ever to train employees on how to spot a fraudulent email/link and to practice caution when following links contained within the bodies of emails. The PDC will continue to monitor the situation and update as needed.
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats. Past performance is not indicative of future results.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.