By Darrel Rendell, Mollie MacDougall, and Max Gannon
Cofense IntelligenceTM has observed Geodo (also known as Emotet) malware campaigns that are effectively spoofing major US financial institutions in part by including legitimate URLs wrapped in Proofpoint’s (PFPT) TAP URL Defense wrapping service. This adds an air of legitimacy to the casual observer, designed to increase the chances of malware infection.
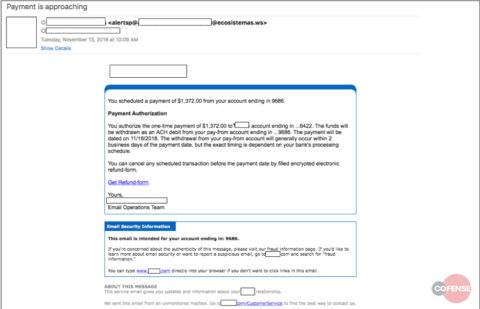
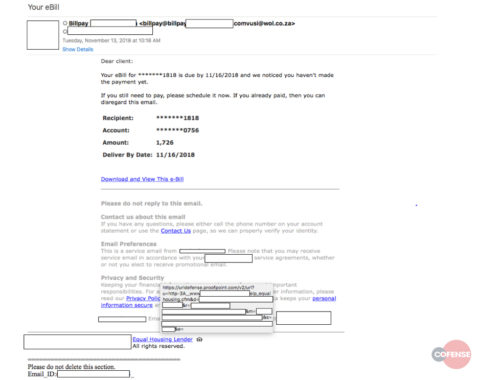
Figures 1 and 2 provide examples of the template and URL wrapping. Cofense Intelligence assesses the improved phishing templates are likely based upon data pilfered with a recently updated scraper module to spoof US financial institutions so effectively.
Figure 1: email template spoofing a major US financial institution
Figure 2: Proofpoint’s URL Wrapping service appearing within this campaign
After a month-long hiatus, Geodo returned on November 6th, 2018 with upgrades to its spamming module, supplementing existing capabilities – namely contact list and signature block theft – with functionality enabling the theft of up to 16KB of raw emails and threads. Although the exact reason for this module upgrade was unclear, Cofense Intelligence assessed it would either be used to bolster the actors’ social engineering efforts, using the stolen data to refine Geodo phishing templates, or for direct revenue generation – selling the raw message content to the highest bidder. Today, it appears the initial prediction was correct.
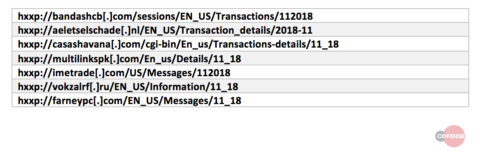
The campaign observed on November 13th was, in many ways, a standard Geodo campaign: messages distributed en masse to targets across the globe, spoofing a known and trusted organization, containing URLs (Table 1) pointing to Word documents containing hostile macros (Table 2). When executed, these macros retrieve a fresh sample of Geodo from one of five compromised web servers and execute it on the machine. As has become increasingly common with Geodo campaigns, the malware functioned as a downloader for other payloads, in this case retrieving a sample of IcedID.
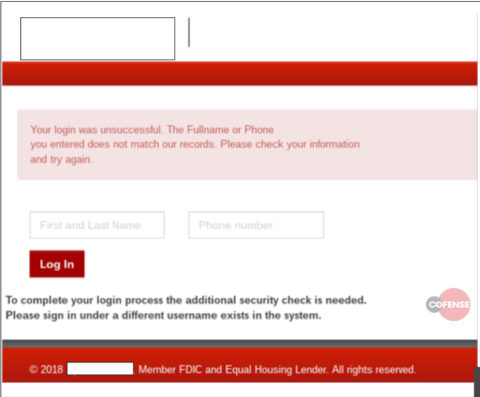
IcedID shares some basic behavior with TrickBot—another prolific banking trojan turned multipurpose botnet. However, IcedID targets both investment and financial institutions as well as several bank holding companies many of which even TrickBot does not target, as TrickBot is much less focused on investment banks or smaller US commercial banks. An example of an IcedID spoofed login page for a regional US bank can be seen in Figure 3.
Figure 3: a spoofed login page for a regional bank that led to a Geodo and subsequent IcedID payload
Geodo has always been a formidable botnet and continues to grow. During tracking, we have seen at least 20,000 credentials added to the list of credentials used by the botnet clients each week along with millions upon millions of recipients. The introduction of this new module has had clear and dramatic effects on the sophistication and efficacy of this social engineering effort. In July, Geodo began including more sophisticated phishing lures, imitating US banks and including graphics that made the emails look less generic and more convincing.
This most recent campaign demonstrated a shocking improvement from that initial upgrade, demonstrating the value of the email scraping module. Considering that where Geodo goes, TrickBot often follows, we are concerned that this type of module will show up in other malware campaigns. The new inclusion of ProofPoint URLs wrapped with URL Defense adds an additional false sense of security to a user and may indicate the malware scraped the wrapped URLs from a compromised user.
Several members of the Cofense Intelligence team discussed Geodo in a recent open customer call. Any customers who were unable to attend are welcome to email [email protected] for a recording.
Cofense is also offering a complimentary Domain Impact Assessment, powered by the Cofense Research and Intelligence teams, for any organization that may be affected by this Geodo update. Learn more here.
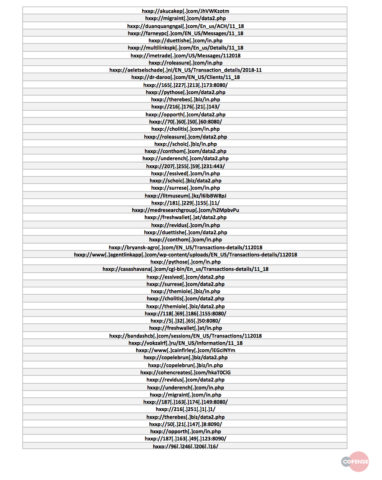
Table 1: Payload URLs observed during this campaign
Table 2: Files associated with this campaign
Table 3: Command and Control infrastructure identified during this campaign
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks.