PHISHING TRAINING
Train Smarter, Defend Better
Employees are your last line of defense against phishing. Strengthen their resilience
through human-vetted intelligence and simulations based on real threats.
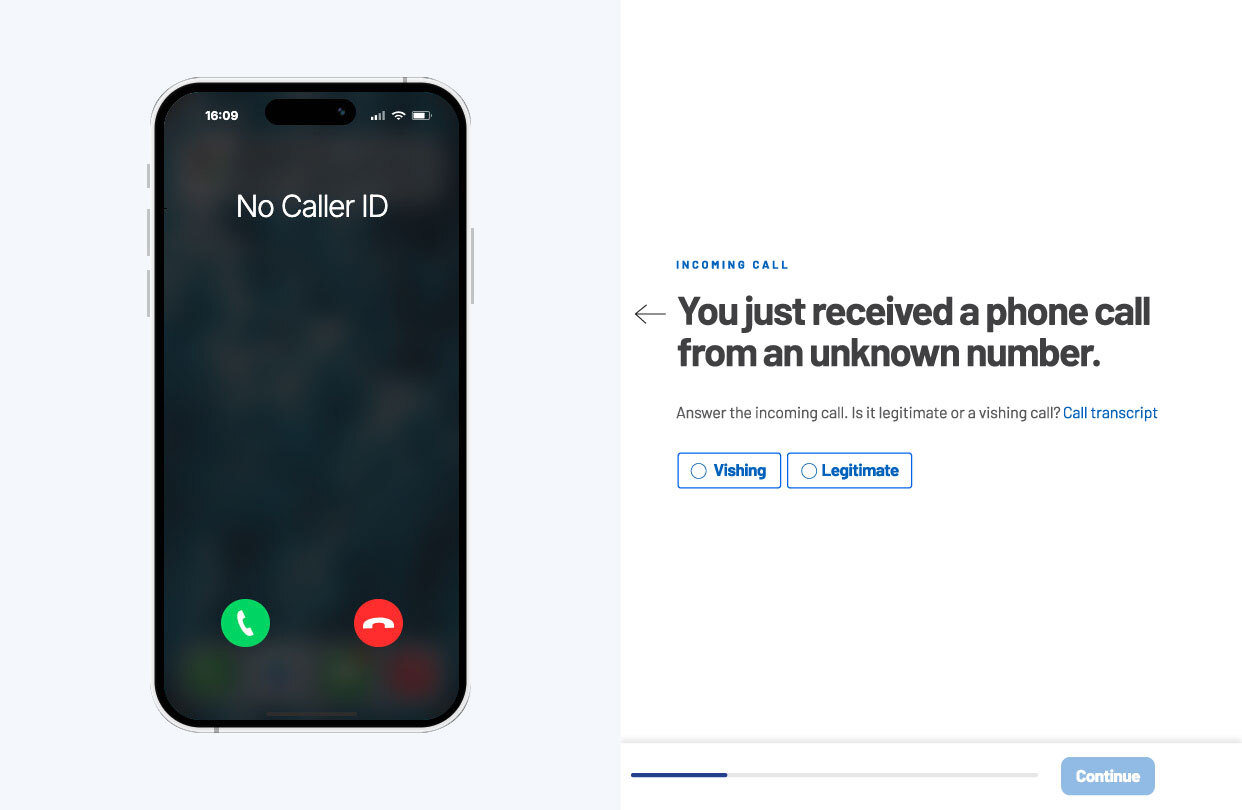
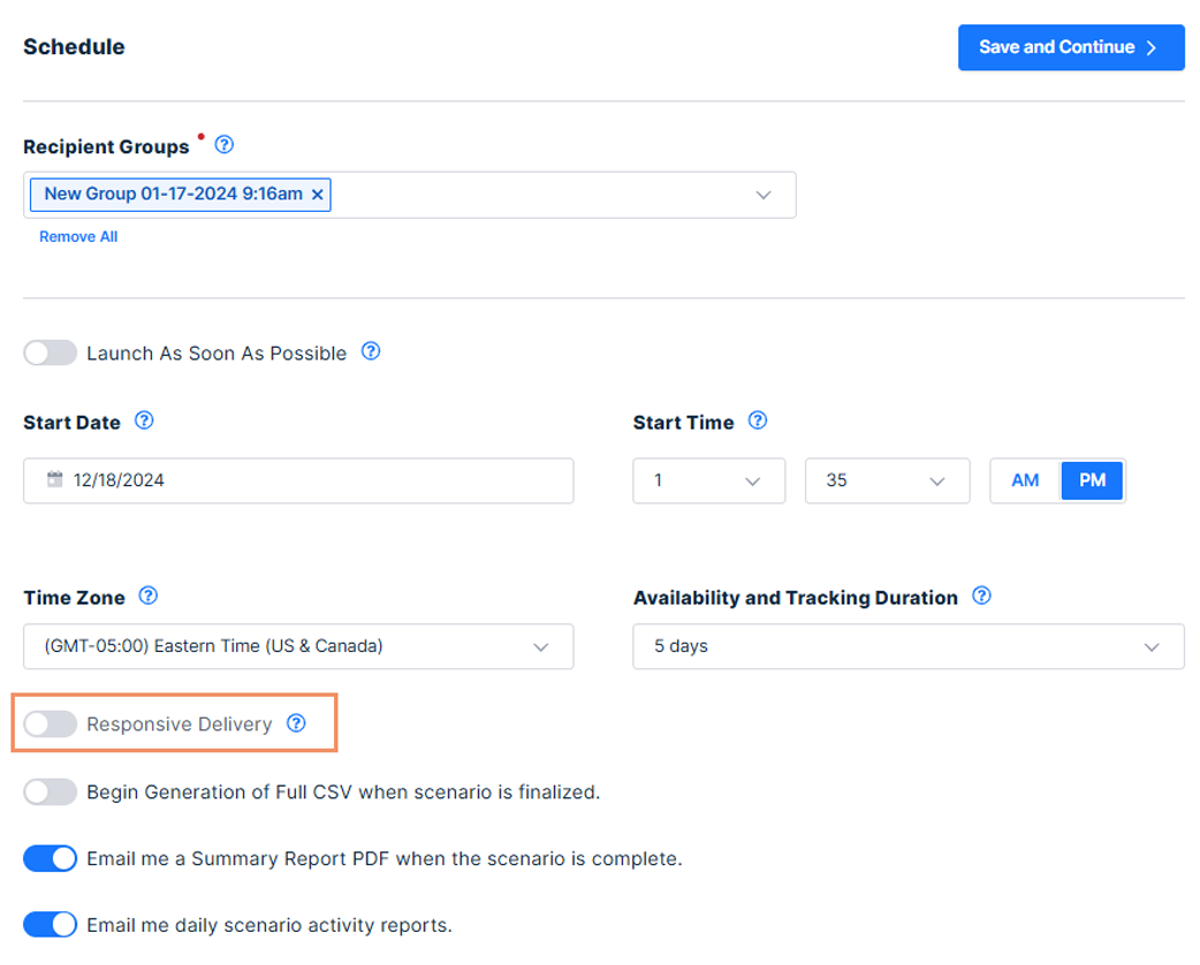
Train on Real and Relevant Threats
Cofense Phishing Training leverages real phishing data for adaptive simulations and awareness programs that learn with every incident.
Build Behavioral Change
Cofense integrated tools such as the Reporter button improve response times and foster positive behavioral change. Employees are able to quickly identify and report phishing threats, and provide actionable insights to mitigate human risk.