
PHISHING REMEDIATION
AI-Driven Phishing Campaign Defense
Stop phishing attacks in seconds. Combine AI-driven detection with human-validated intelligence to surface polymorphic phishing campaigns and remove every related threat across your environment.
Industry Leaders Trust Cofense to Stop Phishing Attacks
Identify Real Threats. Remove Them in Seconds.
Finding threats is the first step, but detection alone doesn’t reduce risk. Cofense removes polymorphic phishing attacks across the environment with AI-driven detection, human-validated intelligence, and automated response.
Detect Full Campaigns
Act with Confidence
Remove Every Instance
Decisive Phishing Defense at Scale
AI detection is common. Complete removal isn't.
Cofense Phishing Remediation goes further than detecting threats that evade perimeter defenses. By connecting detection, validation, and response into a unified solution, Cofense removes threats with 99.998% accuracy.
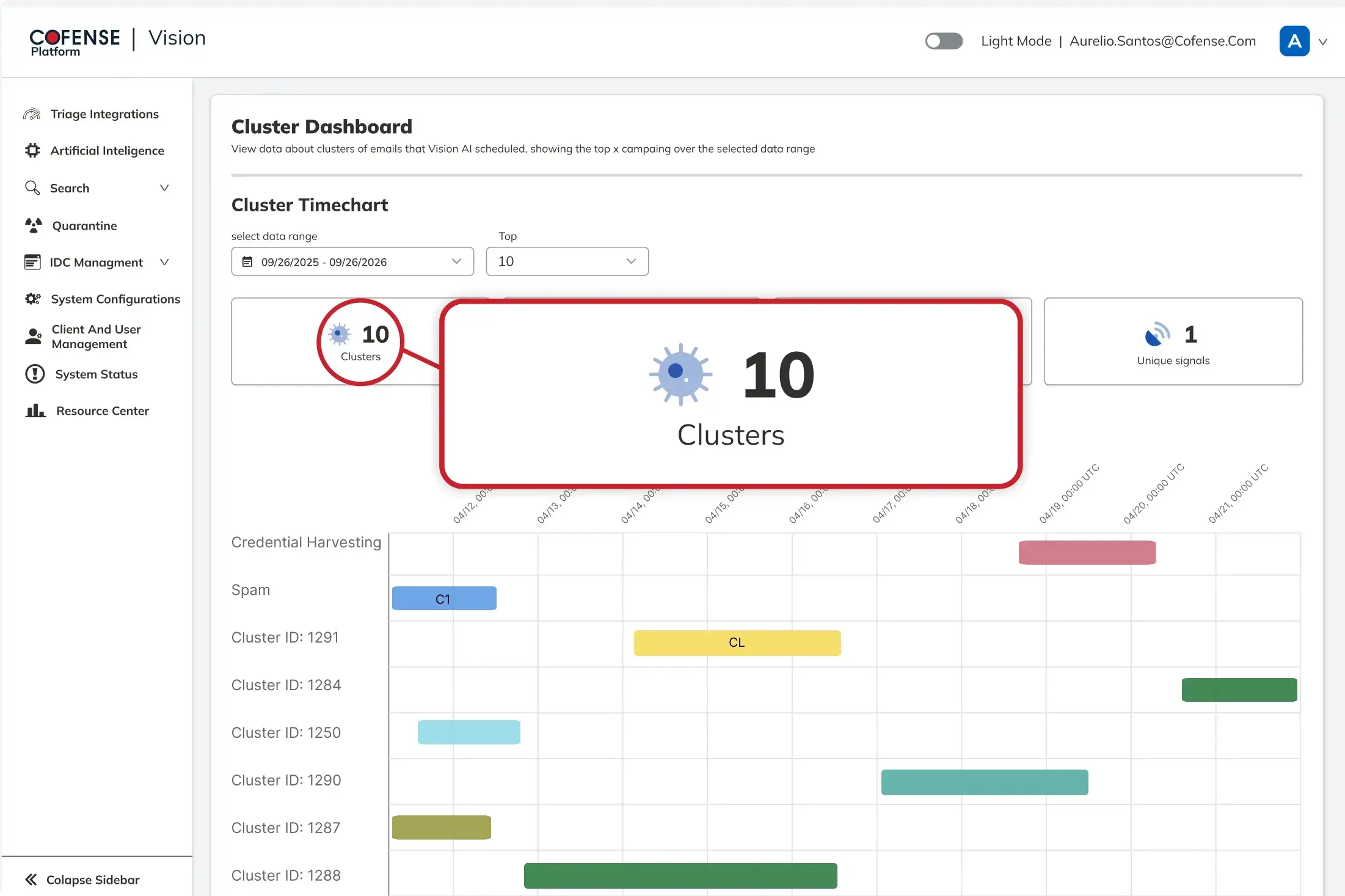
Campaign-Level Detection
AI-driven behavioral analysis identifies coordinated phishing campaigns across evolving variants, infrastructure, and delivery patterns that traditional detection misses.
Transparent, Supervised AI

Supervised AI, tunable thresholds, confidence scoring, and analyst-controlled workflows make automated remediation transparent, explainable, and safe to operationalize at enterprise scale.
Real, Validated Intelligence

Expert-validated phishing intelligence from billions of real-world data points continuously improves detection accuracy, threat validation, and remediation confidence across customer environments.
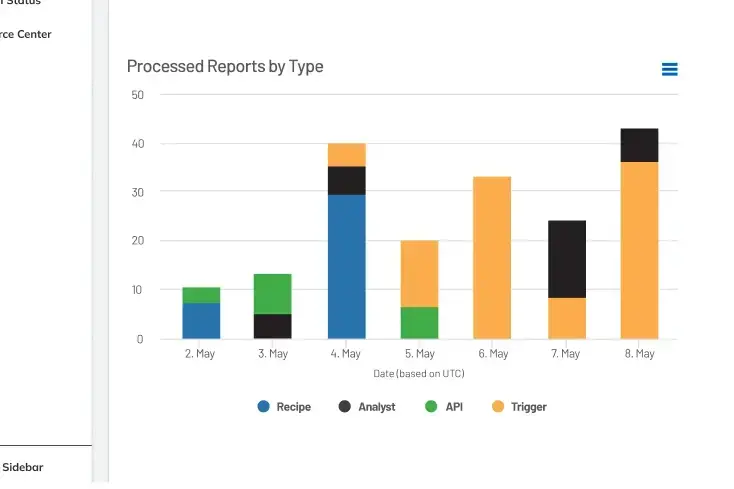
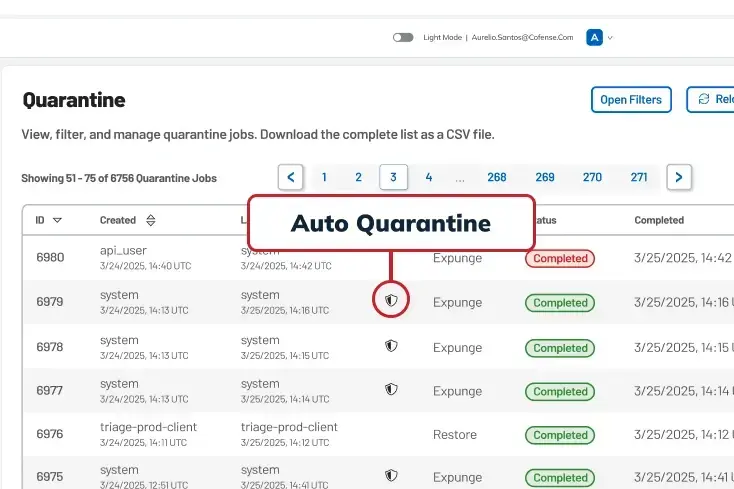
Inbox-Level Remediation
Continuous quarantine, enterprise-wide indexing, and automated remediation workflows enable security teams to identify and remove phishing threats across every inbox in seconds.
.jpg?language=en)
The Measurable Impact of Phishing Remediation
<1min
removal of detected threats
4x
increase in automation*
66%
lower false positive rate*
5x
return on investment
* Cofense Average vs. Industry Standards
Preferred by Security Teams, Trusted By Leaders
Stop Phishing Campaigns Before They Spread
Surface polymorphic campaigns, act on validated intelligence, and remove every malicious threat with AI-driven phishing defense.