By: Marie Mamaril, Intelligence Team
Cloudflare's suite of services like Workers, Tunnels, Turnstile, Pages and Cloudflare R2 (*[.]r2[.]dev) continue to be abused by threat actors to orchestrate stealthy phishing attacks and deliver malware in ways that are difficult for traditional security measures to detect or prevent. This abuse underscores a perilous shift wherein Cloudflare’s legitimate services are now being repurposed by malicious actors to bypass security defenses and evade detection.
Here we will explore specifically how Cloudflare services, especially Workers and Tunnels, became powerful enablers of cyber threats, drawing from actual campaigns that Cofense Intelligence has seen that have bypassed defenses to end up in employee inboxes.
Key Points
- Threat actors continue exploiting Cloudflare's services for credential phishing and malware distribution and evading email-based security controls like Secure Email Gateways (SEGs).
- Threat actors exploit Cloudflare Workers to host phishing pages that convincingly replicate legitimate authentication portals, facilitating credential theft.
- Cloudflare Tunnels are being exploited by threat actors to set up covert connections - this allows them to deploy remote access trojans (RATs), maintaining persistent access to compromised systems that reduce the likelihood of detection.
- What started as free legitimate platforms—designed for website performance, security, and reliability has dangerously evolved into tools that threat actors abuse to bypass defenses.
Understanding Cloudflare and Its Key Services
Cloudflare was founded in 2009 and is a global technology company that has evolved into a powerhouse of web infrastructure, offering a content delivery network (CDN) - which is a system of interconnected servers designed to deliver web content more quickly. When a user requests content, the CDN routes the request to the nearest server, minimizing the distance the data must travel and resulting in faster load times and improved performance. In addition to the speedy content delivery, Cloudflare provides distributed denial of service (DDoS) protection and developer platforms to make websites faster, safer, and more reliable. Its services empower over 20 million sites, from e-commerce giants to personal blogs, by optimizing performance and security without the hassle of hardware management.
Cloudflare Key Services
- Cloudflare Workers are serverless computing platforms that let developers write and run JavaScript (or other supported programming languages) code directly on Cloudflare's massive global network of servers or their “edge network” which makes applications and websites fast and available instantly to users everywhere, without the programmers having to take care of any complex tasks. Programmers only need to write code, upload it, and it will run automatically.
- Cloudflare Tunnels (TryCloudflare) allows secure exposure of local services to the internet without opening firewall ports. It creates a secure connection between your local machine or network and the Cloudflare network, effectively "tunneling" traffic through to Cloudflare’s edge. Once the tunnel is set up, Cloudflare manages traffic securely, making it look like the service is hosted on the Cloudflare network instead of directly on the local machine. TryCloudflare has a free tier that is often abused by threat actors.
- Cloudflare Turnstile is an anti-bot CAPTCHA alternative that verifies users invisibly, minimizing interruptions while blocking automated threats (e.g., malicious automated scripts, DDoS bot traffic, spam bots, crawlers, etc.).
- Cloudflare Pages (*[.]pages[.]dev) and Cloudflare R2 (*[.]r2[.]dev) belong to Cloudflare’s developer platform and are widely used for static site hosting and object storage, respectively. Both services provide zero-cost tiers, simple deployment workflows, and automatic caching via Cloudflare’s global CDN. These functionalities have become a widespread abuse vector for threat actors to frequently launch malicious web pages that mimic legitimate services (e.g., Microsoft Office 365 login, banking portals, crypto wallets, or other spoofed brands). These pages steal credentials, personal data, and payment information.
Overall, these domains are especially attractive to threat actors as it stems from Cloudflare's strong reputation, customizable subdomain (e.g., yourproject[.]pages[.]dev) and the service can automatically provide secure, encrypted connections (HTTPS) for domains and subdomains without the user having to buy, install, or manage their own TLS/SSL certificates or complex web server configs.
How Cloudflare Workers and Tunnels Are Being Abused
Cloudflare offers a wide range of services designed to optimize and protect websites, but their utility for legitimate users has made them an attractive target for threat actors.
One of the reasons that threat actors frequently abuse Cloudflare is that Cloudflare’s infrastructure lends credibility to otherwise suspicious activity. Malicious sites hosted on subdomains like *.workers[.]dev or *.trycloudflare[.]com often slip past network defenses, as they're seen as "trusted."
Additionally, because of their accessibility, many are offered at little to no cost, which renders them susceptible to abuse, so cybercriminals hide behind Cloudflare's reputable domains to bypass security filters.
Cloudflare Workers
While this service is meant to facilitate development for fast and efficient web applications, attackers use them to construct "conventional or adversary-in-the-middle (AiTM) phishing" pages that imitate sign-in interfaces for platforms like Microsoft, enterprise portals, or financial institutions. AiTM phishing is an emerging and advanced type of phishing method that involves the threat actor deploying a relay server that intercepts traffic between the real login system and the unsuspecting individual. The distributed nature of Cloudflare Workers makes it difficult for security teams to track malicious payloads, as they are often distributed across multiple locations globally.
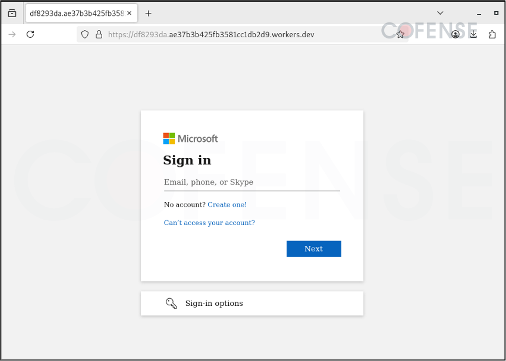
Figure 1: A fake Microsoft login page hosted on Cloudflare Worker Dev.
Cloudflare Tunnels
Cloudflare Tunnels creates secure, private connections between internal servers and Cloudflare's network, providing access to internal services while protecting against DDoS and other attacks. However, threat actors leverage Cloudflare Tunnel primarily by abusing its free TryCloudflare feature to create temporary, obfuscated connections that expose locally hosted malicious content to the internet without revealing the threat actor’s infrastructure.
With this, the free TryCloudflare's quick tunnels have become a significant infection vector for malware campaigns - conduits for delivering Remote Access Trojans (RATs) and Information Stealers frequently associated with web distributed authoring and versioning (WebDAV). WebDAV is a protocol that allows people to manage and edit files on remote servers over the web. It's like a more advanced version of FTP (File Transfer Protocol), letting users upload, download, and edit files on a web server. It’s commonly used for file storage or collaboration platforms, but because it allows file uploads, it could potentially be exploited to deliver malware.
In WebDAV campaigns threat actors use Cloudflare Tunnels or tunneling method to act effectively as DNS system for locating servers that host malicious files and hide behind the [.]trycloudflare[.]com@SSL/DavWWWRoot/ (specific file, folder, or resource path) domain (Figure 3 shows the decoded URL of a [.]trycloudflare[.]com@SSL/DavWWWRoot/). RATs and Information Stealers are delivered through drive-mapping protocols, these protocols make the malicious files appear as “regular network shares” or basically shared folders that people use to exchange files in offices over the web.
The majority of campaigns abusing Cloudflare Tunnels seen by Cofense Intelligence have an embedded link that leads to download a URL shortcut file (see Figure 3). Once the shortcut/URL file is opened/clicked, it pulls a window script file (WSF), which then triggers a harmful set of commands called a batch script. The malicious batch script delivers a Python installer and executes Xeno RAT and XWorm RAT – which enables attackers to gain unauthorized remote access and take control of the infected host/computer from a distance
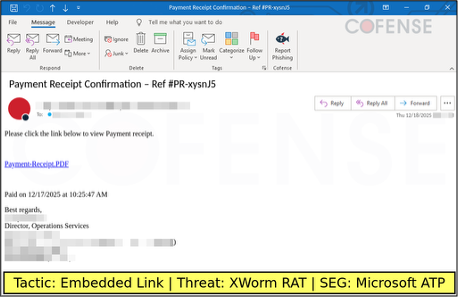
Figure 2: Finance themed emails deliver an embedded link to a file that contains a malicious URL Shortcut hosted in Cloudflare Tunnel.
This whole process retrieves malicious files/payload hosted on Cloudflare-associated web addresses, using this tactic to avoid being flagged by sandbox systems - a virtual environment that cybersecurity experts use for malware analysis. Thus, making it harder for defenders to identify malicious traffic since legitimate Cloudflare IPs are involved in communication.
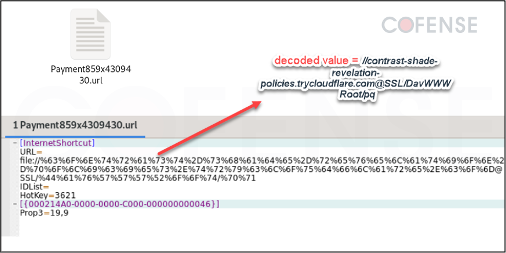
Figure 3: This shows where the URL shortcut file downloaded when opened leads to a remote WebDAV server directory containing a WSF file.
Cloudflare Tunnels helps spin up a phishing page locally or on a compromised host in seconds, which then obtains a Cloudflare-provided domain (e.g., random-system-generated[.]trycloudflare[.]com) without DNS registration. This enables fast campaign creation and deletion as well as rapid rotation to evade blocklists.
Cloudflare Tunnels tend to be more effective overall for threat actors in delivering RATs and broader malware delivery campaigns due to better evasion of detection through traffic obfuscation.
Our data reveals a significant increase in credential phishing attacks leveraging Cloudflare Tunnel and Workers service. The chart below reveals a major threat campaign peak in 2025 for Cloudflare Tunnels and Workers for credential phishing and malware delivery incidents —far exceeding prior years since 2021 tracking began.
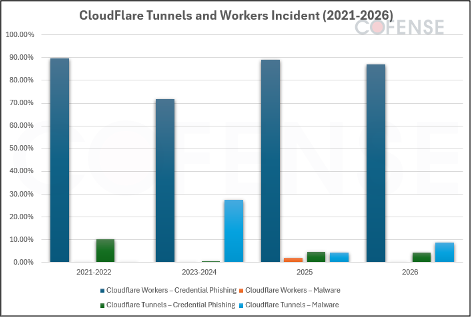
Figure 4: Graphical summary of published IOCs based on Cofense Active Threat Reports (ATR) showing credential phishing and malware incidents for Cloudflare Workers and Tunnels service from 2021 to 2026.
How Cloudflare Addresses Continued Abuse of Their Services
Cloudflare proactively counters malicious platform abuse with multiple defenses. It deploys API-based detection using behavioral analysis and machine learning to spot and block anomalous activity. Enhanced CAPTCHA protections feature dynamic, bot-resistant challenges that evolve continuously. The company also blocks known malicious IP addresses from its network and conducts regular internal audits, sharing transparency reports on abuse handling effectiveness.
Conclusion
The abuse of Cloudflare's infrastructure by threat actors highlights a major challenge in modern cybersecurity: legitimate services are increasingly becoming abused by threat actors. This is the case for legitimate websites, legitimate files, legitimate email providers, and more.
We've seen how Cloudflare's innovative services—designed to empower the web—are being co-opted by cybercriminals for phishing, malware delivery, and evasion tactics. From Workers-powered transparent phishing to Tunnel-hidden RATs and fake Turnstile traps, these abuses turn trust into a vulnerability.
This issue matters not just for security professionals, but for any business that relies on Cloudflare’s services for performance or security.
As threat actors continue to exploit trusted platforms like Cloudflare to bypass traditional defenses, organizations must adopt a more proactive, intelligence-driven approach to phishing and malware detection. Cofense combines real-time threat intelligence with human-driven reporting to help security teams identify and stop these evolving attacks before they cause damage. To see how Cofense can strengthen your organization’s defense against advanced threats like those outlined above, learn more and request a demo at https://cofense.com/demo.