The Cofense Phishing Defense Center (PDC) employs expert Threat Analysts to analyze emails on behalf of enterprise customers across the globe, in various industries, who are dealing daily with phishing attacks delivering malware. To help keep up with evolving tactics and top ongoing threats affecting real customers, the Cofense Phishing Defense Center (PDC) has created a breakdown of the top five malware families we have seen across the Managed Phishing Detection and Response (MPDR) customer base over the past thirty days. If you have any interest in learning more about how your organization can be protected by our expert Cofense Threat Analysts, please contact us for additional information.
Top Malware Families in December:
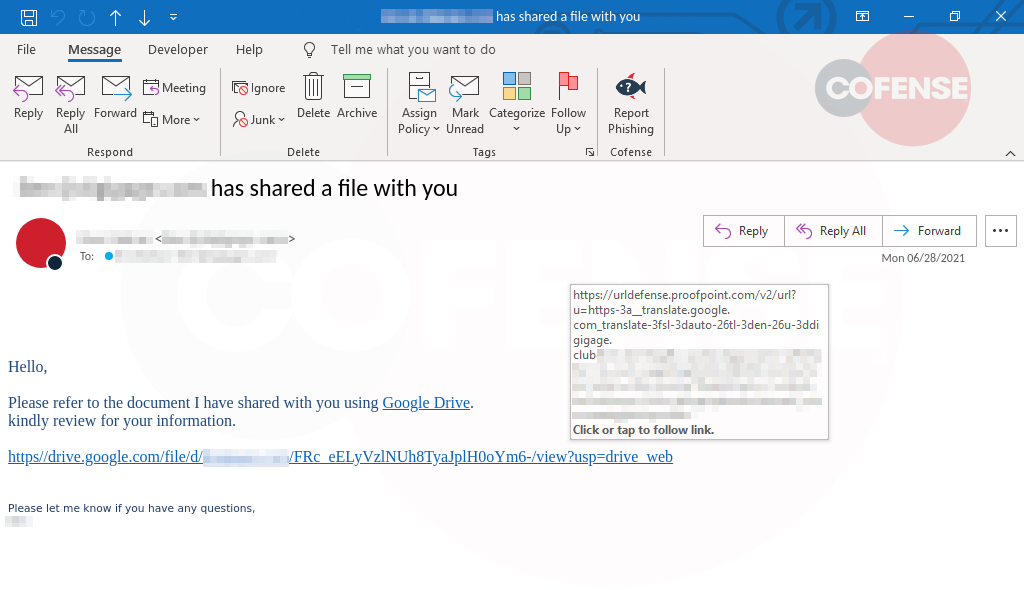
1. QakBot – A modular banking trojan with worm-like features that enable its propagation across a network. Once installed, it will use a man-in-the-browser technique to harvest credentials. The campaigns delivering QakBot re-use legitimate emails to deliver zip files containing the malicious word document.
- Subject: Qakbot subjects are typically forwarded or replies. This means that the subjects are varied.
- Attachment: Qakbot is delivered mostly using URL rather than an attachment.
- Behavior: .img/.iso/.vhd containing data files and a .lnk shortcut Is delivered. .txt and .dat files contained within are used to carry out the attack.
- Brand: RE: FWD: Replies
- Infection Chain:
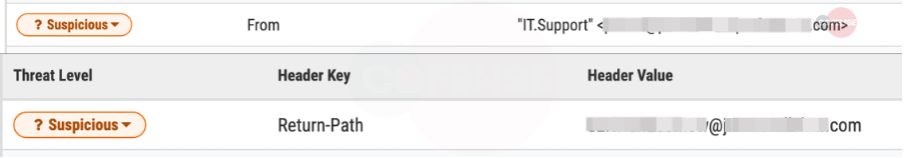
2. Agent Tesla – This information stealer is known for checking browser activity to steal banking information and will send the data through various methods. The most recent variants will use SMTP, FTP, Tor, and HTTP (via Telegram) to send data.
- Subject: Subjects delivering Agent Tesla this month were predominantly in Portuguese. Many were made to look as if they were traffic tickets or receipts.
- Attachment: Agent Tesla was delivered via a URL link instead of an attachment. Most do contain a .png file made to look like a PDF download.
- Behavior: URL Delivers a TAR or TGZ archive which directly contains the malware.
- Brand: Brazil / Portuguese
- Infection Chain:
3. IcedID – A banking trojan that has been appearing on and off in recent months, IcedID is often delivered through an OfficeMacro before reaching out to a payload utilizing uncommon file extensions such as “CAB” or “DAT”.
- Subject: Subjects delivering IcedID were primarily in Spanish or Portuguese this month and were made to look like tax documents.
- Attachment: IcedID used an HTML file attached to the email for many deliveries this month.
- Behavior: HTML file grabs a .rar archive containing the Malware and AutoIT file.
- Brand: Taxes / Portuguese / Spanish
- Infection Chain:
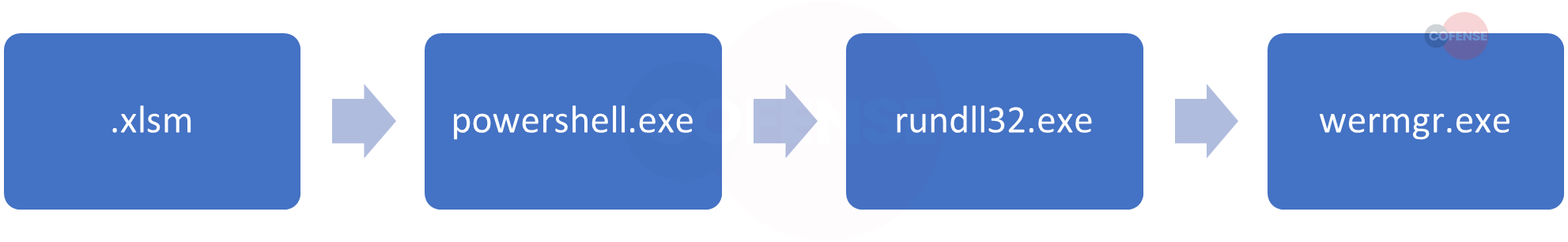
4. Remcos – Remcos was originally a remote desktop connection tool that has since been repurposed as a remote access trojan capable of taking control of a user's system. Its chief capabilities include keylogging, information stealing, and audio/visual monitoring.
- Subject: Most Remcos was delivered in Spanish this month and made to look like receipts for various purchases.
- Attachment: Remcos is delivered as a URL instead of an attachment.
- Behavior: Archive delivered directly contains the malware. Embeds in settings files and waits for orders.
- Brand: Mexico / Receipts
- Infection Chain:
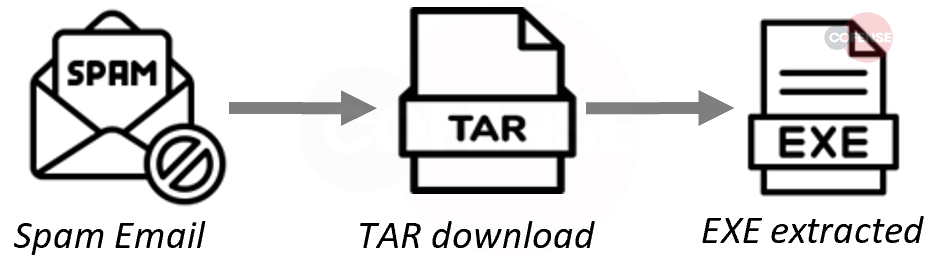
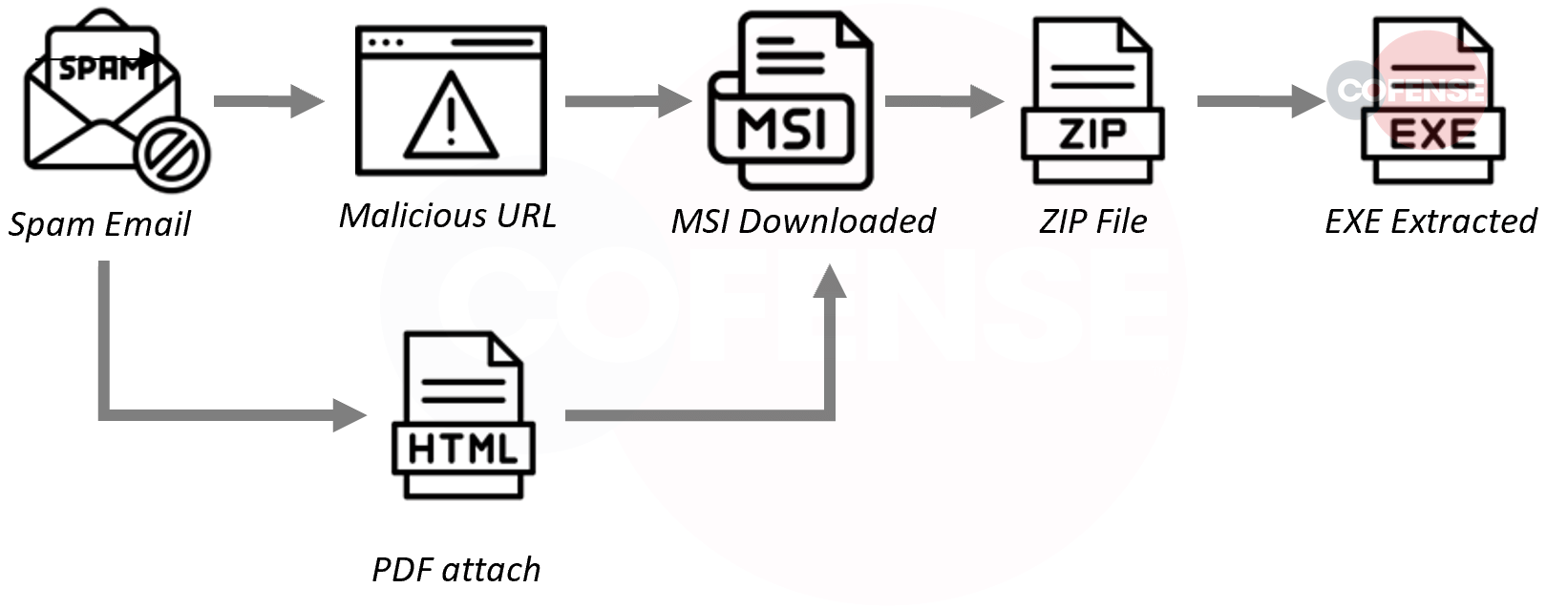
5. KL Banker – A toolkit used as a trojan to run Remote Overlay Attacks.
- Subject: Subjects were made to look like legal summons from Brazilian courts.
- Attachment: KL Banker was delivered both in a PDF and through an infection URL.
- Behavior: Delivered as the second stage of Grandoreiro. PDF baits the user into downloading malicious MSI file containing the stage one exe which pulls KL Banker.
- Brand: Bank of Brazil / Portugal
- Infection Chain:
Summary:
The month of December saw the Cofense Phishing Defense Center (PDC) continue the trend of seeing a large volume of Qakbot malware being delivered through phishing emails. This malware family has been pervasive across all industries and locations. New to the Cofense Phishing Defense Center (PDC) this month was the malware family KLBanker. KLBanker is a banking trojan written in C# and makes use of AES encryption for string obfuscation, this trojan is known for targeting users in South America and Mexico. This month the Cofense Phishing Defense Center (PDC) also saw a rise in IcedID. Given the volume of IcedID seen this month in the Cofense Phishing Defense Center (PDC), we believe that it will likely continue into next month as a popular threat for enterprise users. All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats. Past performance is not indicative of future results.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.