On May 22, 2018, the Cofense Phishing Defense Center observed a Microsoft credential phishing attack that was received by one of our Managed Service customers. The Phishing Defense Center’s goal is to provide our customers all the relevant information on an attack against their employees, within an hour of an email being reported, so customers can take the necessary steps to prevent further attacks. By doing a deep dive investigation into this attack we were able to find multiple other phishing attacks listed on the site, the kits used to create the phishing pages, and several other domains created by the same threat actor.
The phish was a fake Microsoft email informing the victim that they’ve recently blocked several sign-in attempts on their account, and that they should check their account’s recent history by clicking the provided link. Figure 1 displays a screenshot of the phishing email received by the victim.
Figure 1—The phishing email spoofs Microsoft by enticing victims to click the embedded link
The embedded link in the email contains the URL, hxxps://klqiowsa[.]info/>/>?email. However, when visited, the link redirects the victim to the actual Microsoft phishing page located at hxxps://motoblognordeste[.]com[.]br/fire/see/account-s/megoze3uon2xex1kobv2ds5g[.]php, as seen in Figure 2.
Figure 2—The phish emulates a Microsoft login page
When investigating this phish, an open directory was found on the domain of the redirected URL containing links to other phishing attacks as well as zipped archives containing kits used to create these pages. Figure 3 shows the open directory found at hxxps://klqiowsa[.]info.
Figure 3 – The root directory (klqiowsa[.]info) contains links to other phishing scams and phishing kits
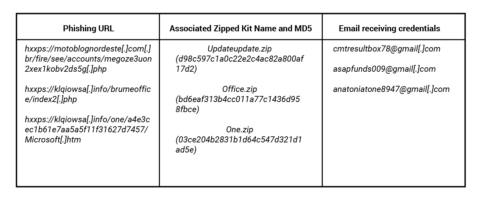
By investigating the individual phishing kits, we were able to discover where the threat actors were emailing stolen credentials for each of the phishing pages. The Figure 4 table displays each of the phishing pages found in the open directory, the zip kit associated with the phish, and the emails receiving the stolen credentials.
The domain hxxp://klqiowsa[.]info was registered on 2018-05-18 by “Frablex Waronez” on the German IP address 62[.]108[.]34[.]46 with the email address wbx45610@cjpeg[.]com. Using open source tools, we searched for any other domains registered with that email address and found two additional domains registered on the same day. We discovered both URLs were still live at the time of our analysis.
The two websites were hxxp://ujrtqwas[.]net and hxxp://qwkoiasd[.]com. We found that they used the same phishing method of using an open directory to host phishing kits and several different phishing pages.
By investigating every lead we could find, we were able to discover additional information that could be used to block future attacks. This allows the Phishing Defense Center to provide customers with as much information as possible when attacks like this occur. By using this information, customers can make decisions that will help save their employees from becoming victims of current and future malicious attacks. To stay ahead of emerging phishing and malware attacks, sign up to receive free Cofense threat alerts.