CISO Summary
Cofense IntelligenceTM has spotted a phishing campaign using the Lime remote administration tool (RAT), whose versatility makes it an especially dangerous malware type. Lime RAT is a mash-up of ransomware, cryptominer, stealer, worm, and keylogger. When skillfully deployed, it can filch a wide range of information, encrypt computers for ransom, or transform the target host into a bot.
Lime RAT appeals to novice and seasoned threat actors alike, thanks to its anti-virus evasion techniques, anti-virtual machine features, small footprint, and encrypted communications. Threat analysts will want to read the full analysis below. Security awareness managers will want to educate employees by simulating phishing emails containing diverse malware threats.
Full Details
Cofense IntelligenceTM analyzed a phishing campaign that delivered an all-in-one ransomware/cryptominer/stealer/worm/keylogger called Lime Remote Administration Tool (RAT). Lime RAT’s code is written in C# and is dependent on .NET 4.0. Lime RAT is part of a malware library which includes Lime_Miner, Lime_Crypter, and Lime_USB. This malware is open source and touts itself as a teaching tool for .NET malware. But being feature-rich and well-documented, Lime RAT can also be used for nefarious actions by malicious operators.
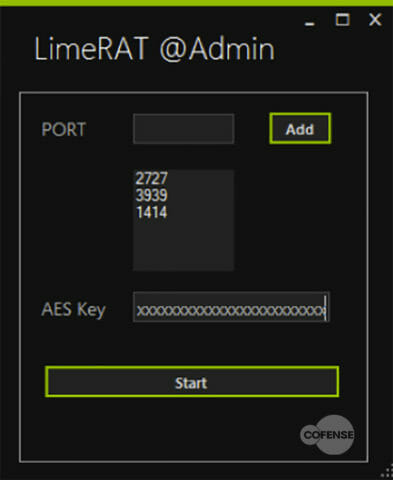
An interesting feature of this malware family is the use of multiple ports for communication, which establishes redundancy for the communication channels. The initial setup of the Lime RAT building platform and panel needs only two things: port numbers and an AES (Advanced Encryption Standard) 128-bit encryption key. The port number is used to open a port to listen on the server. The AES key is used to encrypt all communication between the client and the server. Figure 1 shows the initial setup pane with the ports and AES key as discussed above.
Figure 1: Setup process for Lime RAT
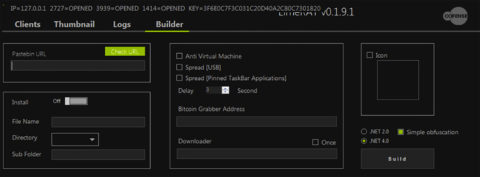
The builder for the payloads is simply comprised of checkboxes and text input fields that even the most novice operators can use to produce effective, malicious binaries. This panel allows you to customize the payload with different features and icons. It also allows you to set the Command and Control (C2) infrastructure and the location for the persistent drop file on the targeted machine. Figure 2 shows the features available to customize each payload, including the anti-virtual machine option.
Figure 2: Features available to the Lime RAT payloads
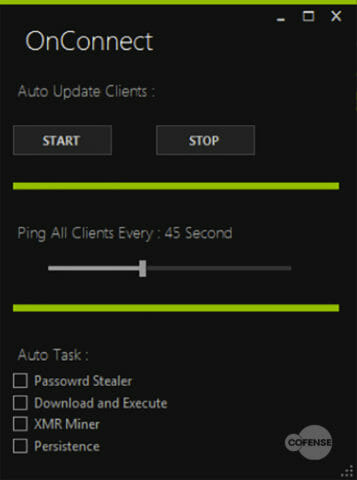
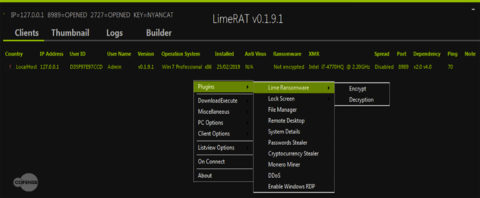
When the Lime RAT payload has been created, sent to and executed on a target machine, the binary connects to the panel. When the client connects, it sends information to the control panel and includes details about the operating system, CPU, user, country, and more. The control panel gives the option to automatically assign a task for the client, for example, downloading and executing a specific file. Figure 3 shows the control panel populated with information from the connected client, while Figure 4 shows the ‘OnConnect’ automatic tasking panel.
Figure 3: Control panel view of an infected client machine connected to the C2 infrastructure
Figure 4: ‘OnConnect’ automatic tasking options
The control panel allows the operator to manipulate the target by right-clicking on the selected machine and choosing a command. This is where the operator can specify the method of attack: initiate the encryption for ransomware, drop a Monero miner, enable Remote Desktop Protocol (RDP), steal information/cryptocurrency, and more. Figures 5 and 6 show the options available to the operator for a given target.
Figure 5: Ransomware and other plugins for the target machine
Figure 6: Keylogging and persistence options for the targeted machine
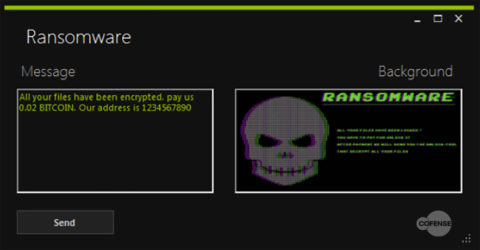
The ransomware feature lets you customize the message as well as the image displayed. When the targeted host is encrypted with the ransomware aspect of this RAT, the file extensions are turned to ‘.Lime’. Figure 7 shows the customizable message and default image that displays to the client after the encryption has been initiated.
Figure 7: Lime RAT’s default ransomware message
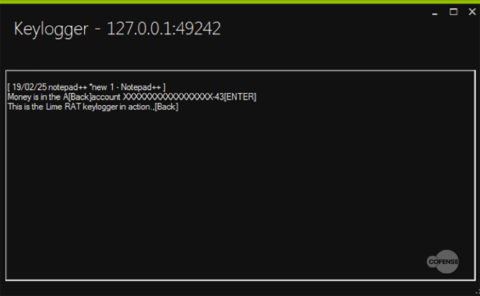
The keylogging feature is not very advanced in what it collects. It can only collect what is entered by the keyboard and not what is auto-filled or added from the clipboard. The keylogger output does show a timestamp and which application the text was written in. Figure 8 shows the control panel output of a running keylogger module on a client infected with Lime RAT.
Figure 8: Collection of text from the keylogger module
As shown earlier in Figure 2, Lime RAT can spread like a worm. When the payload is built, the operator can specify the ‘USB spreading’ and ‘pinned task bar application spreading’ features be included within the payload. The USB spreading feature looks for any connected type 2 device and then attempts to replace any file with an executable version of Lime RAT. When doing this, Lime RAT will keep the original icon for the file that has now been infected. The spreading through the pinned task bar applications takes it one step further by replacing the shortcut path to which those icons are linked.
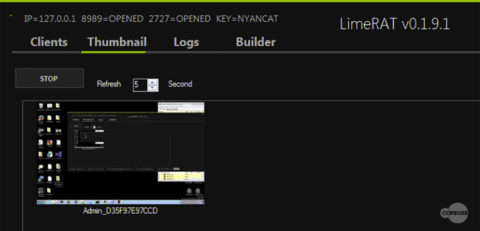
The ‘Thumbnail’ tab (Figure 9) within the control panel of Lime RAT is a screengrab of the infected machine. This screengrab can be turned on or off and has a timer that defaults to 5 seconds between screen grabs.
Figure 9: ‘Thumbnail’ tab that holds the screen grabs of the infected machines
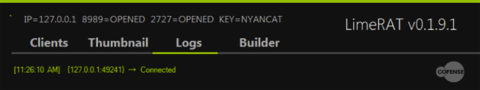
Logging in Lime RAT is not nearly as advanced as we’ve seen in other RATs. As shown in the Figure 10, the ‘Logs’ tab only logs timestamps and IPs of connections and disconnections.
Figure 10: ‘Logs’ tab and the connections made
Lime RAT is an open source, well documented, .NET framework malware suite with multiple features that make it devastating when properly used. The ability for this malware to steal a wide range of valuable information, encrypt for ransom, and/or turn the target host into a bot with basic capabilities, mixed with an intuitive control panel display, makes it a likely choice for novice operators. The anti-virus evasion, anti-virtual machine feature, the small footprint, and encrypted communications would appeal to threat actors across the capability spectrum. The number one way to keep multivariate threats like Lime RAT from infecting a machine via a phishing campaign is to educate the end user on suspicious emails and attachments.
To stay ahead of emerging phishing and malware trends, sign up for a FREE 90-day trial of Cofense Intelligence.
To see more updated information on Lime Rat, see the blog post, New Mass Logger Malware Could Be Massive.
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks.