“Secure” Email Gateways (SEG)
100% of the phish we find in customers’ environments were reported by end users. Zero percent were stopped by SEGs. Let’s learn what is a SEG and explore why.
What is a SEG?
Secure email gateways (SEG) are a form of email security technology that provides an additional layer of protection from spam and malicious emails. Secure email gateways defend against phishing attacks, spear-phishing attacks, ransomware and other forms of malware threats.
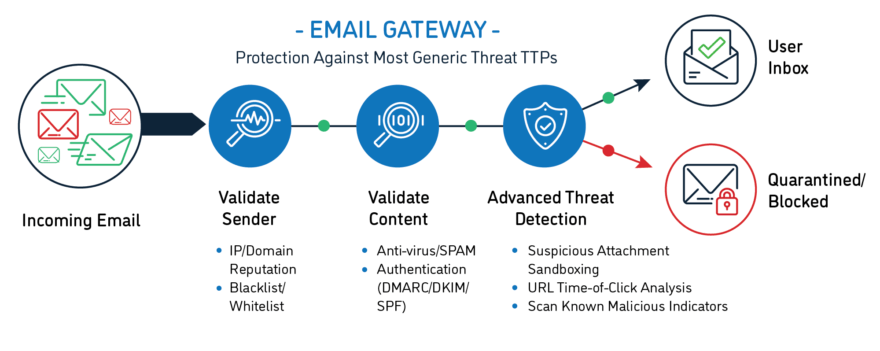
How SEGs are Intended to Work:
Secure email gateways—AKA email gateways or email security solutions—are the most common type of perimeter technology used to stop phishing emails from reaching the inbox.
SEGs are designed to work in two main ways. They attempt to validate an email’s sender through domain authentication and sender reputation. And they try to validate its content using threat intelligence, antivirus, and content analysis tools. While SEGs do their job to a point, it’s hard to ignore the facts.
Why Do SEGs Fail?

BUSINESS CAN’T WAIT
Businesses depend on email to keep operations running, so tuning a SEG to drastically slow down messages isn’t feasible. You’re forced to choose between speed and organizational security.
ATTACKERS OUTSMART TECHNOLOGY
Threat actors constantly adapt phishing attacks to security advances, often changing tactics by the hour. Using BEC, for example, an attacker relies on social engineering, not URLs, attachments, or other clues SEGs look for.

SEG VENDORS ARE REACTIVE
Whether Proofpoint, Microsoft, Symantec, Mimecast, Cisco Ironport, you name it, SEG vendors are playing a game of whack-a-mole, reacting to fill countless holes when attackers need just one.
The Impact of Phishing…
Average cost of a data breach globally
Source: Ponemon Cost of Data Breach 2022
Average cost of a data breach in the U.S.
Source: Ponemon Cost of Data Breach 2022
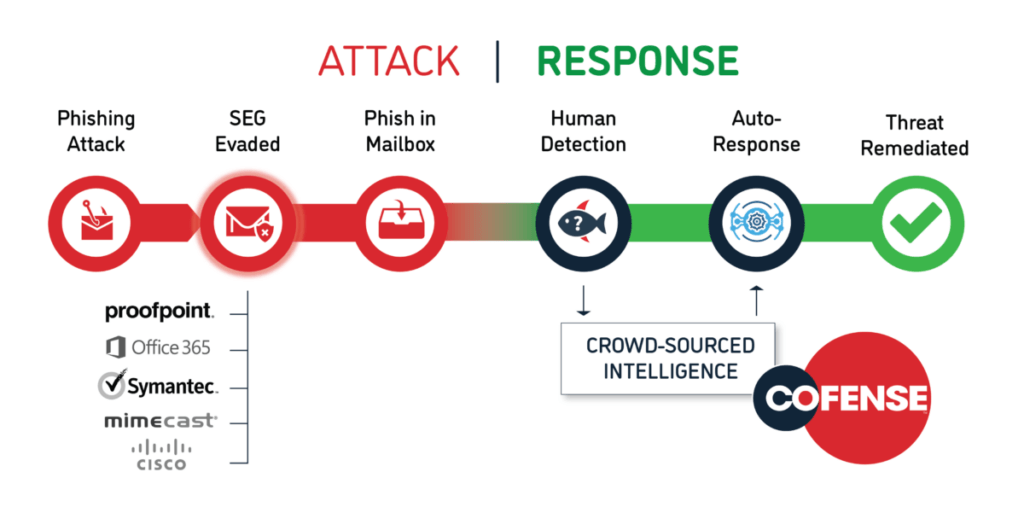
We catch the phish your gateway misses. In seconds.
Built on the world’s largest data lake of phishing threats found by real people, Cofense combines the power of human detection with automated response, enabling your teams to stop phishing attacks in minutes. It’s advanced technology augmented with collective human intelligence – the first solution purpose-built to quickly detect and stop phish that reach the inbox. Contact us to find out how Cofense can help with choosing an email security solution that does everything your enterprise requires.
Did You Know This About SEGs?
SEGs undergo NO third-party validation
Unlike firewall and other security technologies, SEGs appear to be immune from any regulatory or compliance oversight.
Phishing emails still land in the inbox
No matter what percentage of emails your gateway successfully stops, malicious emails continue to reach user inboxes daily.