Cofense IntelligenceTM has uncovered an advanced campaign that uses multiple anti-analysis methods to deliver Quasar Remote Access Tool (RAT). A phishing email poses as a job seeker and uses the unsophisticated ploy of an attached resume to deliver the malware. Quasar RAT is freely available as an open-source tool on public repositories and provides a number of capabilities. Organizations find a higher degree of difficulty with the ‘.doc’ file attachment distributing Quasar RAT itself, because the document employs a multitude of measures to deter detection. Such methods include password protection—which is a built-in feature of Microsoft Word—and encoded macros. Along with automated tools, educating employees on new phishing trends is the best way of countering a campaign such as this.
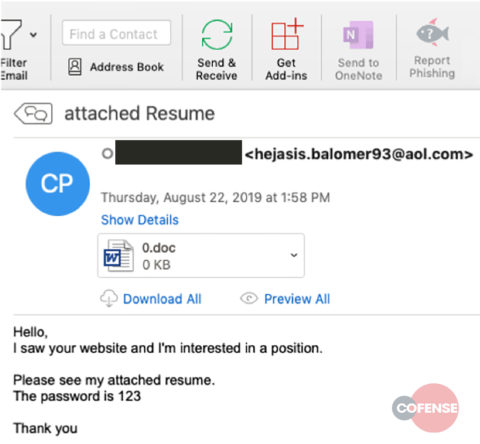
Figure 1: Original Email
Technical Findings
The initial email used to deliver this malware, seen in Figure 1, uses a relatively common “resume” theme with an attached document. As previously mentioned, Quasar RAT is not particularly unusual or advanced compared to other toolkits. A US-Cert report states that Quasar RAT “has been observed being used maliciously by Advanced Persistent Threat (APT) actors to facilitate network exploitation,” however, Quasar is also “a publicly available, open-source RAT” and can be found on GitHub. Since the tool is easily accessible, attributing the activity to a specific threat actor is tedious at best.
The malicious attachment used by this campaign employs counter-detection measures to reach the end user. Even if the email is marked as being suspicious, the attachment may be treated as legitimate and delivered. Despite a simplistic and apparent first stage delivery, threat actors took advantage of increasingly sophisticated methods to increase the difficulty of analysis and delay detection. This delay can provide threat actors with enough time to gather information and potentially install additional, more subtle, malware before being detected or removed.
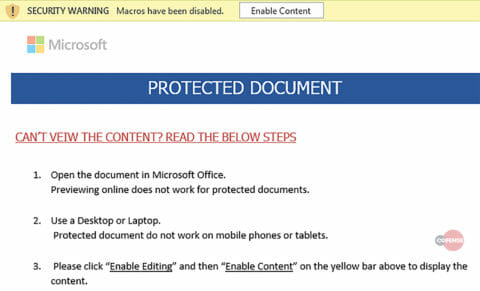
The first stage of the avoidance practiced by the document in this campaign is simple password protection. A password of “123” is not particularly inventive, but to an automated system that processes attachments separately from emails it means that the document will be opened and no malicious activity will be recorded because the system has not determined either a need for a password or what the password is. Sufficiently advanced systems should still be able to guess a password of “123”; however, this only opens the document and does not necessarily trigger malicious activity. The resulting prompt is shown in Figure 2.
Figure 2: Request to enable macros
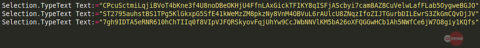
If an analyst or automated system were then to attempt to analyze the macros using an analysis tool (such as the popular tool ‘olevba’ by Philippe Lagadec), the script would fail and potentially crash from using too much memory when it attempted to analyze the macro. This is likely an intentional effect by the threat actor in the form of more than 1200 lines of garbage code that appears to be base64 encoded. Forcing the script to attempt to decode the garbage strings causes, in all likelihood, a crash due to the magnitude of decoding required. An example of some of these garbage strings is shown in Figure 3.
Figure 3: Example of the fake encoded strings
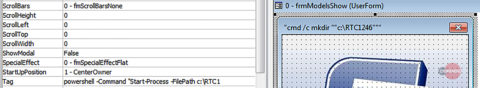
If those strings are not decoded or the process decoding them has enough resources allocated, the resulting content still lacks the all-important payload URL. Instead, partial strings and filler text give some semblance of legitimacy. Portions of the payload URL, as well as additional information, are in fact hidden as meta-data for embedded images and objects, as shown in Figure 4.
Figure 4: Script content in the meta-data of a form object
Other script content bears essential information within its comments. Below, you can see evidence that this macro may originate from a template or guide. Here, some of the commentary relates to if the operating system is Windows or Mac.
Figure 5: Commentary included in the script
Embedded comments describe the usage of a shelled application and the startup process. If the macro is successfully run, it will display a series of images claiming to be loading content while repeatedly adding a garbage string to the document contents. It will then show an error message while downloading and running a malicious executable in the background.
The last significant step the threat actors take to avoid discovery is to download a Microsoft Self Extracting executable. This executable then unpacks a Quasar RAT binary that is 401MB. The technical maximum file upload size for the popular malware information sharing website, VirusTotal, is 550 MB. However, the commonly used public methods of submission, email and API, are set to 32MB maximum with special circumstances for API submission going up to 200MB. By using an artificially large file size the threat actors make sharing information difficult while also causing problems for automated platforms that attempt to statically analyze the content.
Table 1: Malware Artifacts
| Filename | MD5 |
| 0.doc | 1d7328b01845117ca2220d8f5e725617 |
| Period1.exe | 15dbb457466567bfeaad1d5c88f4ebfe |
| Uni.exe | e7bcec4d736a6553b4366b0273aaf6f8 |
Table 2: Network IOCs
| IOC |
| hxxp://1xv4[.]com/due[.]exe |
| toptoptop1[.]online |
| toptoptop1[.]site |
Yara Rule:
rule PM_Intel_Quasar_27476
{
strings:
$message_lede = "the password is " nocase
$attachment = /[0-9]{1,3}.doc/ nocase
$subject = /subject:s*attached resume/ nocase
condition:
all of them
}
HOW COFENSE CAN HELP
90% of phishing threats delivering malware payloads analyzed by the Cofense Phishing Defense CenterTM bypassed email gateways. Condition users to be resilient to evolving phishing attacks with Cofense PhishMeTM . Quickly turn user reported emails into actionable intelligence with Cofense TriageTM. Reduce exposure time by rapidly quarantining threats with Cofense VisionTM. Easily consume phishing-specific threat intelligence to proactively defend your organization against evolving threats with Cofense IntelligenceTM.
Looking for a holistic phishing defense solution? Cofense provides everything you need to catch them stop phish quickly. Our combination of technology and unique human insight allows us to detect and stop attacks — before they hurt your business. Learn more about our managed phishing detection and response (mPDR) solution.