Gateways Bypassed Symantec
Phishing attacks evolve over time, and attacker frustration with technical controls is a key driver in the evolution of phishing tactics.
In today’s modern enterprise, it’s not uncommon for our emails to run the gauntlet of security products that wrap or scan embedded URLs with the hope of finding that malicious link. Products like Proofpoint URL Defense, Microsoft Safe Links, and Mimecast URL Protect hope to prevent phishing attacks by wrapping or analyzing URLs. These technologies can only be effective IF they can find the URLs in the first place.
Fast forward to this week where our Phishing Defense Center™ stopped a phishing campaign aimed at customers in Finance. The analysis below outlines the attacker’s use of a URL encoded in a QR code to evade the above-named technologies. While you’ve probably seen QR codes in your everyday life, this might be the first time you are seeing QR code phishing used as a tactic.
The Phish:
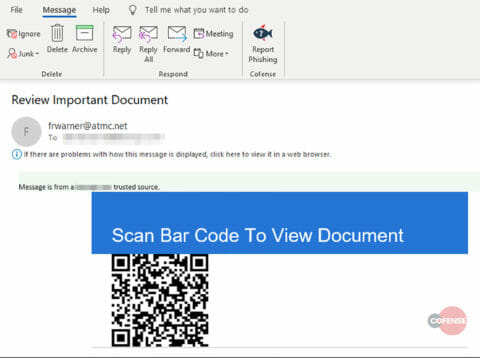
The email itself is relatively simple. It poses as a pseudo SharePoint email with the subject line: “Review Important Document”. The message body invites the victim to: “Scan Bar Code To View Document”. The only other visible content is a tantalizing QR code that a curious user may be tempted to scan.
Figure 1, Email Body
The message body in plain text consists of several basic HTML elements for styling and an embedded .gif image file of the QR code. Very basic, but very effective.
When the QR code is decoded we can see that that it contains a phishing URL: hxxps://digitizeyourart.whitmers[.]com/wp-content/plugins/wp-college/Sharepoint/sharepoint/index.php
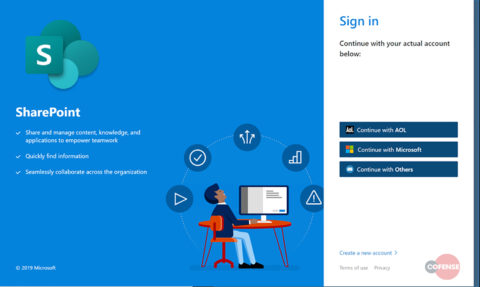
Most smartphone QR code scanner apps will instantly redirect the user to the malicious website via the phone’s native browser. In this case the victim would be redirected to a SharePoint branded phishing site. The victim is then confronted with options to sign in with AOL, Microsoft, or “Other” account services. While this sounds like a simple phish, there is a more nefarious tactic in play: removing the user from the security of a corporate business network.
Figure 2, Phishing site
Standard Security Controls Circumvented:
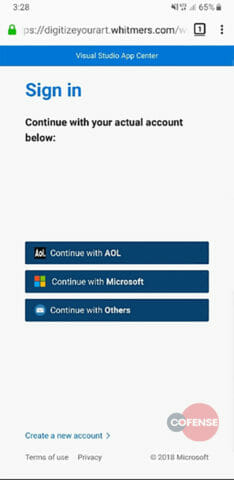
By enticing the victim to pull out their smartphone and scan the QR code the attacker manages to evade standard corporate security controls. Secure email gateways, link protection services, sandboxes, and web content filters no longer matter because the user is now interacting with the phishing site in their own security space: their mobile phone. And yes, the phishing site is optimized for mobile viewing. Here’s a glance at what the site looks like on a smartphone:
Figure 3, Phishing page viewed on phone
Though the user may now be using their personal device to access the phish, they are still in the “corporate” mindset as the original email was received at their business email address. Therefore, it is highly likely that the victim would input their corporate account credentials to attempt to access this “document”.
Gateway Evasion:
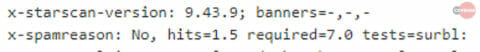
This attack was observed passing through an environment utilizing Symantec Messaging Gateway. When scanned, the message was deemed “Not spam” by the system as seen in Fig 4 below.
Figure 4, Email Header Snippet
Conclusion:
In the past QR codes were reserved for geeks on the bleeding edge of technology. Today we interact with QR codes more and more as we cut the cord on cable, setup home internet devices, transact crypto currencies, etc… Will QR codes be a common phishing tactic of the future? Time will tell. But THIS phishing attack that snuck past best in class phishing technologies was only stopped by an informed, in tune human, who reported it with Cofense Reporter ™ , so that their security teams could stop it.
Today over 90% of phishing threats observed by the Cofense Phishing Defense Center ™ bypassed secure email gateways. Condition users to be resilient to evolving phishing attacks with Cofense PhishMe ™ and remove the blind spot with Cofense Reporter.
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks.