Microsoft 365 EOP
Last week, the Cofense Phishing Defense CenterTM observed phishing threat actors using low-level trickery to avoid detection, by utilizing basic percentage-based URL encoding. This takes advantage of Google’s nifty ability to decode the encoded URL data on the fly. The easiest way to trick a secure email gateway (SEG) is hiding the true destination of the payload.
Here’s how it works:
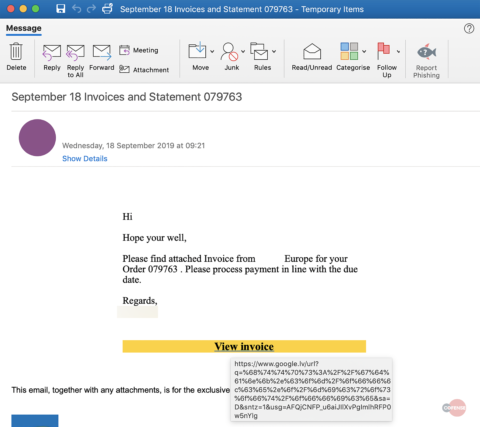
Figure 1: email body
The phishing email is simple and originates from a compromised email account of a relatively well-known American brand, informing recipients that they have a new invoice awaiting payment. The email body has an embedded hyperlink button, highlighted in yellow, where users can click to view the invoice.
As we can see in Figure 1 above, the true destination of the hyperlink is not immediately obvious to the untrained eye and unfortunately the same is true for many perimeter security devices. We note that the URL’s top-level domain is google.lv which is the home page for Google Latvia.
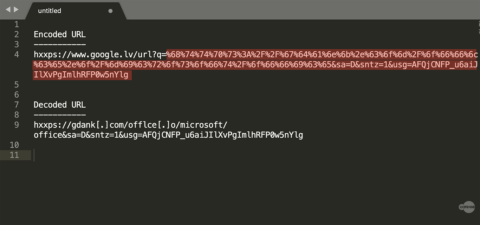
Figure 2: URL Encoding
If we take a deeper look into the embedded hyperlink, we see that Google is being used to redirect the recipient to a secondary malicious URL. The first part of the URL is benign “hxxps://google.lv/url?q=”, which tells the web browser to use Google to query a specific URL or string.
The second part of the string, highlighted in red (Figure 2), is the payload which is a string that is encoded with basic URL encoding. This is sometimes referred to as percent encoding, which replaces ASCII characters with a “%” followed by two hexadecimal digits. Most web browsers recognize URLs that contain hexadecimal character representations and will automatically decode them back into ASCII on the fly without any user interaction. When users click on the hyperlink within the email, they are redirected through their browsers to Google to query the encoded string. This is recognized as a URL to redirect the user to the final destination of the malicious payload.
This is enough to fool basic URL and domain checks by perimeter devices, a simple yet effective way for threat actors to ensure delivery of malicious payloads.
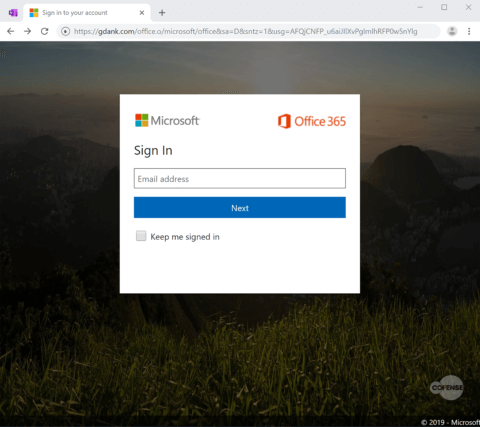
Figure 3: Phishing Page
The phishing page itself is a simple imitation of the Office 365 login portal and aims to steal corporate users’ credentials. With businesses’ growing reliance on Office365, it’s fast becoming a favorite target amongst phishing threat actors.
| Network IOCs | |
| hxxps://gdank[.]com/office[.]o/microsoft/office/ | 107[.]180[.]27[.]240 |
HOW COFENSE CAN HELP
Cofense Resources
Cofense PhishMeTM offers a simulation template, “New Invoice,” to educate employees on the phishing tactic described in today’s blog.
75% of threats reported to the Cofense Phishing Defense Center are credential phish. Protect the keys to your kingdom—condition end users to be resilient to credential harvesting attacks with Cofense PhishMe.
Over 91% of credential harvesting attacks bypassed secure email gateways. Remove the blind spot—get visibility of attacks with Cofense ReporterTM.
Quickly turn user-reported emails into actionable intelligence with Cofense TriageTM. Reduce exposure time by rapidly quarantining threats with Cofense VisionTM.
Attackers do their research. Every SaaS platform you use is an opportunity for attackers to exploit it. Understand what SaaS applications are configured for your domains—do YOUR research with Cofense CloudSeekerTM.
Thanks to our unique perspective, no one knows more about the REAL phishing threats than Cofense. To understand them better, read the 2019 Phishing Threat & Malware Review.
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats.