By Tonia Dudley
CofenseTM was the pioneer of phishing simulation as a training method to defend against phishing incidents. We’ve evolved our products and methodology as we understand that real phish are the real problem. What has also evolved over time is the depth of our scenario templates—when threat actors shift to use a new tactic to make their way past the secure email gateway (SEG), Cofense is able to quickly offer a scenario based on that tactic.
When we say, “Real phish are the real problem” we mean organizations should set their phishing defense strategy from end to end. This starts with how we provide simulation training, teaching users how to identify phish and react, and then how Security Operations teams mitigate the potential incident. Training against real phish, the ones your organization actually faces, is essential.
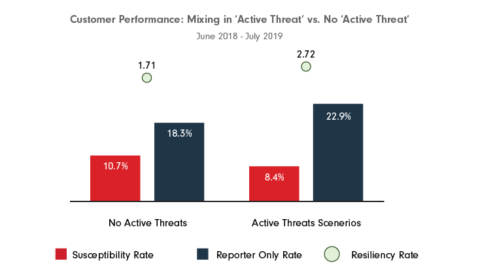
Let’s look at data to tell the story. It comes from our recently published Annual Phishing Report 2019. Looking at the data in Figure 1, which specifically related to “real phish,” we can see organizations that use templates based on real phishing emails (active threats) have far better results. Not only is the report rate higher, but we see the susceptibility rate also lower, ultimately affecting the overall resiliency rate.
Figure 1
When an organization has been running their program for a few years, they begin to wonder how much is enough and whether they should keep sending scenarios. We point to the phishing emails reported by our customers in our Cofense Phishing Defense CenterTM (PDC). More than 90% of emails reported came from environments that use a SEG. While the SEG is absolutely necessary to protect an organization, like any other defense it’s not infallible against threat actors who continually adjust their tactics to make their way into the inbox. This is why it’s vital to align your training scenarios to what gets past your SEG.
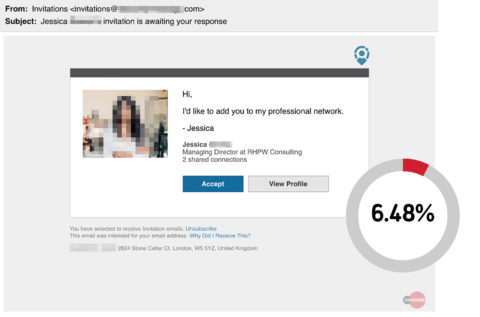
Taking another view, we see what happens with two common templates available for simulation campaigns. The first one is made to look similar to a social media message users might receive if they associate their work email with this site. You can see the click rate is fairly low. Are the threat actors really spending that much time making a phishing email look this fancy?
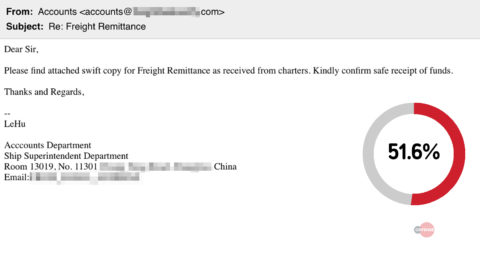
The second template looks very simplistic and our security awareness operator is less likely to select this template. It appears too basic, nobody would actually click the message, right? Yet, there is a much higher click rate on this template that mimics a real phishing message.
So are you preparing your organization to detect and report real phishing emails? Are you preparing them to defend against the actual messages that make it past your SEG? Our data shows that keeping it real makes a real difference.
View our report to learn other ways to double your resiliency to phishing.
HOW ELSE COFENSE CAN HELP
Most phishing threats observed by the Cofense Phishing Defense Center bypassed secure email gateways. Condition users to be resilient to evolving phishing attacks with Cofense PhishMeTM and remove the blind spot with Cofense ReporterTM.
Quickly turn user reported emails into actionable intelligence with Cofense TriageTM. Reduce exposure time by rapidly quarantining threats with Cofense VisionTM.
Easily consume phishing-specific threat intelligence to proactively defend your organization against evolving threats with Cofense IntelligenceTM.
Thanks to our unique perspective, no one knows more about REAL phishing threats than Cofense. To understand them better, read the 2019 Phishing Threat & Malware Review.
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats.