Industries We Serve
An intelligent cybersecurity strategy is essential to safeguard your organization.

Critical Infrastructure
In every critical infrastructure industry — from defense to telecommunications to transportation — hackers are after the same thing.

US Federal Government
Phishing attackers often leverage social media, contracts, and information to infiltrate federal networks.

Higher Education
Many college and university “bring your own device” policies make it hard to implement a unified and secure network.
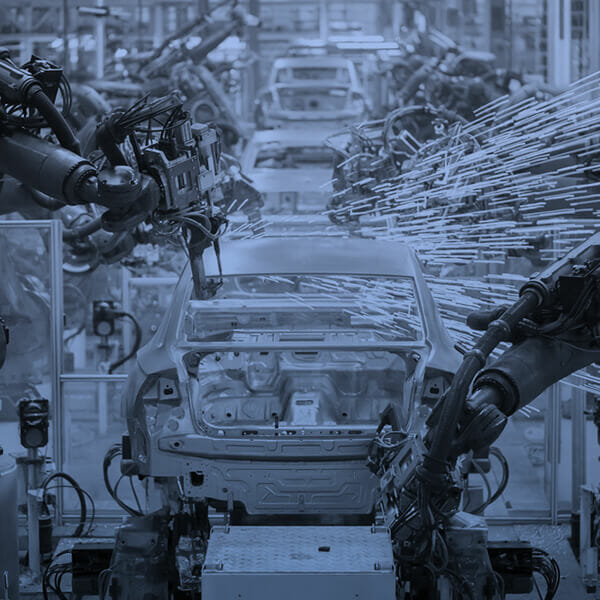
Manufacturing
Many still use outdated legacy security systems that don’t provide protection against modern phishing threats.

Technology
Since tech companies have access to large amounts of information and capital, they can be a favorite target of attackers.

Financial Services
As gatekeepers of important financial and personal information, financial services businesses are a favorite phishing target.

Healthcare
Healthcare data is notoriously valuable — for everyone from providers and patients to phishing attackers.

Legal & Professional
Legal and professional services businesses have access to lots of sensitive information, attackers are holding this information ransom.

Energy & Utilities
Unlike other industries, cybercriminals target energy and utility companies not for monetary gain but to inflict harm.

Retail
Whether it’s daily sales or the Cyber 5, opportunities for your business are also opportunities for phishing attackers.
End-to-End Email Security Built to Stop Threats.
Defend your organization with our complete suite of email security solutions.



